Check Point SASE extends your VPN capabilities, reducing admin workload, simplifying access operations, and improving the hybrid user experience.
Strengthens threat prevention with advanced ThreatCloud engines, enhanced MCP visibility, and smarter phishing and encrypted traffic protections.
4 New ThreatCloud AI Engines: PDF security with advanced image and text analysis, malicious GitHub-hosted account and repository detection, automatic creation of file and IPS protection rules, and a new web security model with enhanced decision-making capabilities.
Zero Phishing: Protects users from phishing attacks even without HTTPS Inspection, leveraging Server Name Indication (SNI) in TLS handshakes.
DNS Security: Introduces DNS-over-TLS threat prevention to block malicious DNS activity over encrypted channels.
HTTPS Inspection: Supports Hardware Security Module (HSM) for TLS 1.3, enabling secure and high-performance decryption and inspection of encrypted traffic.
HTML Smuggling: Blocks HTML smuggling - an advanced technique that evades detection by building malware locally within a target's web browser.
Adaptive IPS: Automated detection and remediation of CPU-intensive IPS protections, with the integrated bypass metric analysis.
MCP Detection and Visibility: New detection and visibility for managing and monitoring Model Context Protocol (MCP).
Seamlessly manage 1,500 gateways from a single Management Domain and 1,000,000 identities with Identity Awareness.
Scalable Identity Awareness: Each PDP now supports up to 1,000,000 identities and shares with 300 PEP gateways, even across multiple domains.
SD-WAN Support with Maestro: Adds SD-WAN capabilities to Maestro Security Groups, enhancing branch office scalability, reliability, and redundancy.
Security Management Scalability: Scale up to 1,500 gateways per Management Domain and 10,000 gateways with Multi-Domain configuration.
Streamlines operations with automated Route-Based VPN setup, smarter logging, and a faster, modern management experience.
Unified Identity Management & Scale: Seamless integration with Check Point Identity to provide unified policy enforcement, major scale improvement in identity sharing across Policy Decision Points (PDP).
Web SmartConsole: Enhanced capabilities in the Web-based UI that delivers a smoother user experience and significantly faster response times for managing policies and logs.
Log Improvements: New logging mode enables streamlined control over daily log output, with improved granularity into log levels and analytics for high-volume rules.
Simplified Route-Based VPN: Automatically configures Site to Site VPN based on network topology, enabling one-click setup and dynamic routing with BGP.
For more information, refer to the R82.10 Release Notes
New streamlined and assured approach to deploying HTTPS Inspection
Deployment assessment: Phased deployment for performance assessment
Full fail-open: Automatically detects and adds exceptions for client-side Inspection failures improving end-user experience
Default HTTPS inspection policy for best practice
HTTPS monitoring: a comprehensive status overview and detailed statistics
Web Security: Support of HTTP/3 over QUIC for Threat Prevention and Sandboxing
Experience
Introducing new deployment modes for Clustering and VSX
New clustering technology (ElasticXL):
- Single Management Object (SMO), delivering simplified cluster configuration
- Automatic sync of configuration and software versions between cluster members
New VSX mode (VSNext):
- Added capabilities to VSX with streamlined management experience for all types of gateways, physical and virtual
- Improved provisioning by supporting Gaia Portal, Gaia Clish, Gaia REST API, and Management API
Prevention
Four New AI-Powered and cloud-delivered threat prevention engines for detecting malware, phishing & C2 communication
Advanced DNS Security enhancements:
- Protection against NXNS Attacks
- Support DNS over HTTPS (DoH)
- Detailed statistics on DNS Security in SmartView Dashboard
- Advanced DNS Security settings in Threat Prevention Profile
SNORT rules as an IoC Feed: Loading of SNORT rules file as a Custom Intelligence Feed to be enforced as an IPS protection
For more information, refer to the R82 Release Notes
Threat Prevention
Superior Threat Prevention with new AI Deep Learning engines.
-
Prevents 5x more DNS attacks in real-time.
- Uses millions of zero-day IoC to prevent Command & Control connections and block data theft through DNS tunneling.
- Response time to DNS attacks was decreased from hours to minutes.
- Blocks 4x more attacks with patented in-line Zero Phishing (no software is required on the client side).
Security Gateway blocks phishing attacks to prevent theft of credentials in any web browser.
- Check Point Services for on-premises Management Servers - increase network security with advanced cloud-based security services.
- IoT Network Security - Discover your IoT assets and enforce zero-trust policies.
- SmartWorkflow - Built-in policy supervision over changes in Security Policies and objects.
- Enforce changes in Access Control automatically without installing policy, using Network Feed objects.
- Integrate with SAML 2.0 Identity Providers to allow secure authentication in SmartConsole and for Remote Access users.
- Get the complete event visibility across all Check Point products for efficient monitoring.
Security Performance
- Hyperflow - provides 3x throughput boost for processing large file transfers (elephant flows).
- Maestro Auto-Scaling - dynamically adds and removes Security Group Members based on CPU utilization and traffic.
- Maestro Fastforward - provides ultra-low 1 microsecond latency and 100 Gbps throughput by offloading specific Access Control rules to the Check Point Maestro Orchestrator for hardware acceleration.
- Scalable VPN performance - Security Gateway can process more Remote Access VPN connections at the same time.
For more information, refer to the R81.20 Release Notes
Web SmartConsole now includes Read/Write capabilities for most commonly used functions. More capabilities to be added over time.
SmartConsole is now updated automatically! No need to reinstall the client to get the latest fixes.
Distribute logs between multiple active Log Servers to support higher rate of logs and redundancy of Log Servers.
IPS and Anti-Bot logs now include a MITRE ATT&CK section that details the different techniques for malicious attack attempts.
Faster Management API execution.
REST API commands to simplify the creation of gateways in SmartProvisioning and more.
Enhance security with the new Access Control Rulebase settings and defaults.
Significant Management stability and performance improvements.
IoT support for Multi Domain Management.
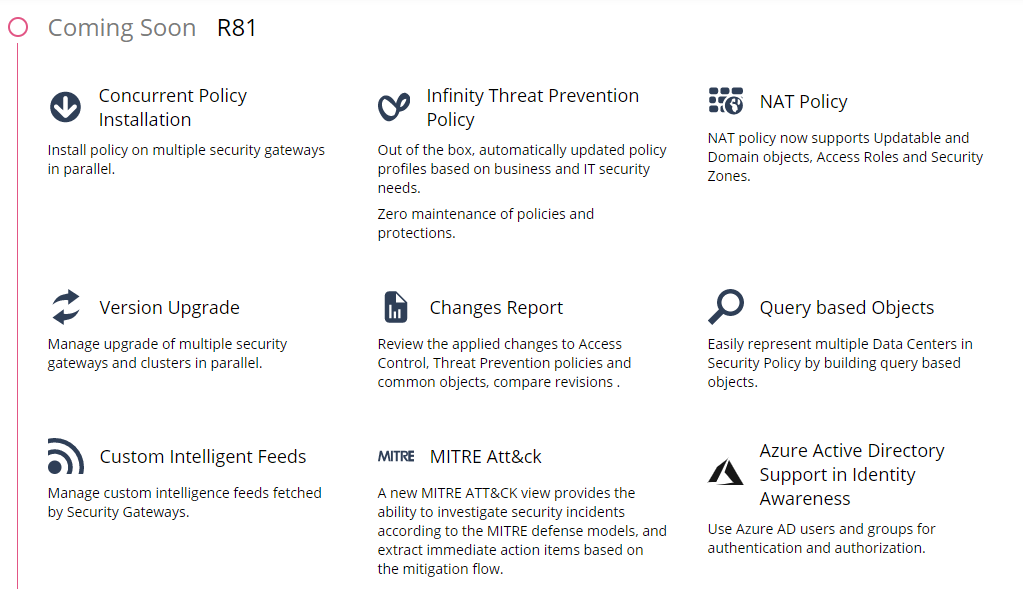
Out of the box, automatically updated policy profiles based on business and IT security needs.
Zero maintenance of policies and protections.
New acceleration mechanism drastically speeds up the Access Control policy installation time.
Install different policies on multiple Security Gateways in parallel.
NAT policy now supports Updatable and Domain objects, Access Roles and Security Zones.
Manage upgrade of multiple security gateways and clusters in parallel.
Review the applied changes to Access Control, Threat Prevention policies and common objects and compare revisions.
Easily represent multiple Data Centers in Security Policy by building query based objects.
Manage custom intelligence feeds fetched by Security Gateways.
A new MITRE ATT&CK view provides the ability to investigate security incidents according to the MITRE defense models, and extract immediate action items based on the mitigation flow.
Use Azure AD users and groups for authentication and authorization.
Backup and restore a domain, migrate Security Management Server to a domain, migrate a domain to a Security Management Server.
Manage HTTPS Inspection Policy in a new dedicated layer within SmartConsole and share across multiple policy packages.
Manage multiple user defined encryption domains per community.
Manage large scale VPN environment using LSV profiles.
Automate and customize actions based on predefined Management operation triggers.
Centrally deploy Hotfixes and Jumbo Hotfixes on multiple Security Gateways and Clusters in parallel.
Revert to a previous management revision and continue working from that point.
Discover every IoT device in the network and turn its data into actionable security intelligence.
Automatically generate security policy based on customer’s profile, connected devices and IoT network status.
Expose advance forensics per SandBlast log focusing on Mitre Att&ck Techniques and Tactics.
CloudGuard Controller enhancements,
Captive Portal integration with SAML 2.0 and third party, Partial Search, and more...
Add third-party tools as panels and views inside SmartConsole.
Use vCenter Tags and
NSX Universal Security Groups
in your security policy.
Since R80.20.M2
Exporting your logs to Splunk Enterprise Security is now simpler.
Check Point's Splunk Add-On contains new dashboards for Check Point logs and events.
Since R80.20.M2
New Consolidated threat prevention dashboard providing full threat visibility across Networks, Mobile and Endpoints.
Since R80.20.M2
Threat Extraction now proactively protects against threats contained in Web downloaded documents.
Threat Prevention logs contain new fields for forensics.
One administrator can publish or discard several SmartConsole sessions, independently of the other sessions.
Since R80.20.M1
Use improved log viewer with cards, profiles, statistics and filters to analyze events.
Create a secure log exporting channel using just 1 line of configuration.
Since R80.20.M1
Configure malicious email policy with Threat Profiles in SmartConsole.
Mark IPS Protections to follow-up on them later.
User experience enhancements when monitoring and configuring policies for virtual environments.
New data center objects for: Google Cloud Platform, Cisco ISE and Nuage.
Since R80.20.M1
Create presets for cross-domain
policy installations.
Run policy installation presets with a single click or schedule to run them automatically.
Endpoint Security Server updates, SmartProvisioning, Compliance, GDPR,
Global VPN Communities, Rule-base performance improvements, and more...
Since R80.20.M1
Security policy is enhanced to accept or block traffic according to application & data.
One log entry shows network, application and data information.
Policies can be segmented into layers, allowing simplicity and delegation.
IPS and the SandBlast family can be unified as one policy and installed separately from Access Control changes.
The new rule matching algorithm, improvements in acceleration templates and new FQDN-based domain objects increase your gateways' performance.
Packet-mode search, rule navigation shortcuts and a session pane for change history increase your operational efficiency.
New Management API commands for show-changes, verify-policy and more.
Visit Check Point's Github account for open-source tools based on the R80.10 Management API.
Several administrators can work together using different sessions.
During a session, all modified objects are being locked.
Objects and rules can be modified using CLI and web service API.
All management operations (e.g. policy installation) are supported.
Unified threat management for correlated events based on the Check Point logs.
Customized overviews and reports to show real-time events. Drill-down from a chart to see the actual logs.
Highlight a rule to view its logs.
All monitor views are integrated into the console.
Detailed monitor view of all gateways in the system. Embedded commands of backup, scripts and more.
Revert to previous policy, object tags, tabbed policy view, exporting to CSV files and more manageability enhancements.
 Watch on YouTube
Watch on YouTube Discuss on CheckMates
Discuss on CheckMates Watch webinar
Watch webinar Get the tools from Github
Get the tools from Github