


In This Section: |
When a VPN community is selected in the VPN column of the Security Policy Rule Base, the source and destination IP addresses can belong to any of the Security Gateways in the community. In other words, the traffic is bidirectional; any of the Security Gateways can be the source of a connection, any of the Security Gateways can be the destination endpoint. But what if the administrator (in line with the company's security policy) wished to enforce traffic in one direction only? Or to allow encrypted traffic to or from Security Gateways not included in the VPN community? To enable enforcement within VPN communities, VPN implements Directional VPN.
Directional VPN specifies where the source address must be, and where the destination address must be. In this way, enforcement can take place:
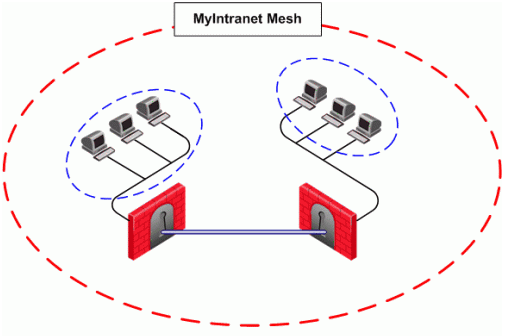
The figure shows a simple meshed VPN community called MyIntranet. VPN traffic within the MyIntranet Mesh is bidirectional; that is, either of the Security Gateways (or the hosts behind the Security Gateways in the VPN domains) can be the source or destination address for a connection.
Source |
Destination |
VPN |
Service |
Action |
Track |
|---|---|---|---|---|---|
Any |
Any |
MyIntranet => MyIntranet |
telnet |
accept |
log |
Any |
Any |
MyIntranet |
telnet |
accept |
log |
The match conditions are represented by a series of compound objects. The match conditions enforce traffic in the following directions:
The table shows all the objects that can be configured in a direction, including three new objects created for Directional VPN:
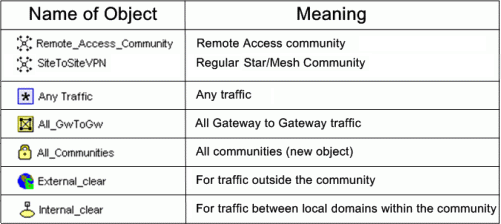
|
Note - Clear text connections originating from the following objects are not subject to enforcement:
|
There is no limit to the number of VPN directions that can be configured on a single rule. In general, if you have many directional enforcements, consider replacing them with a standard bidirectional condition.
VPN Directional Enforcement can take place between two VPN communities. In this case, one gateway must be configured as a member of both communities and the enforcement point between them. Every other peer gateway in both communities must have a route entry to the enforcement point gateway in its vpn_route.conf file.
To add a route entry to the enforcement point gateway:
On the management module of each gateway in the community (except for the enforcement point gateway), add an entry in the $FWDIR/conf/vpn_route.conf file:
Destination |
Next hop router interface |
Install on |
|---|---|---|
< |
< |
< |
These are the variable in the entry:
destination_community_obj - a network object for the combined encryption domain of the communityenforcement_point_gw - the gateway that is a member of both communities and transfers the encrypted traffic between themmanaged_FW_object - all community members that are managed by the management moduleIn the example below, Washington is a Mesh community, and London is a VPN Star.
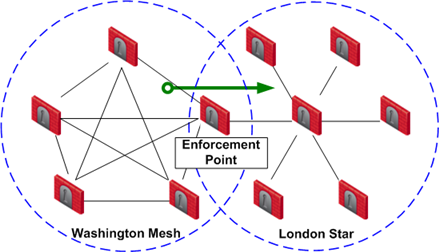
The directional VPN rule below must be configured for the enforcement point gateway in the Security Policy Rule Base:
Source |
Destination |
VPN |
Service |
Action |
|---|---|---|---|---|
Any |
Any |
Washington => London |
Any |
accept |
The rule is applied to all VPN traffic that passes through the enforcement point gateway between the Washington and London communities. If a connection is opened from a source in the Washington Mesh, and the destination is in the London Star, the connection is allowed. Otherwise, the connection is denied.
|
Note - The Directional Enforcement applies only to the first packet of a connection. If the connection is permitted, the following packets of this connection are also permitted, including the packets in the opposite direction. |
To configure Directional VPN within a community:
The VPN Match Conditions window opens.
The Directional VPN Match Condition window opens.
This allows traffic from the local domain to the community, and within the community.
To configure Directional VPN between communities:
The VPN Match Conditions window opens.
The Directional VPN Match Conditions window opens: