Introduction
Check Point Security Gateway Virtual Edition protects dynamic virtual environments and external networks from internal and external threats by securing virtual machines and applications. This solution uses proven Check Point security technologies: Software Blade architecture, Firewall with content inspection, IPS, central management, and more.
Security Gateway Virtual Edition has different operation modes. Find which is best for your environment and plan the installation accordingly.
- Hypervisor Mode enforces VM security in the VMware Hypervisor with inter-VM traffic inspection, without virtual network topology changes.
- The Network Mode is deployed as a virtual network device to protect virtual networks and physical environments. You can configure it as a router or a bridge, with the same procedure as a physical gateway.
Important Notes:
- This release supports only Network Mode on Gaia.
- All references to ESX in the document are also for ESXi unless noted differently.
Key Benefits
- Operates as a layer-2 or layer-3 Security Gateway for virtual network environments.
- Supports ClusterXL for High Availability and Load Sharing.
- Enforces security with no downtime during and after VMware vMotion migration.
- Supports vMotion of the Security Gateway Virtual Edition virtual machine.
- Protects expanding virtual networks while reducing hardware investment, maintenance, energy, and site costs.
- Optimizes performance for virtual environments.
Basic Deployment with Network Mode
In this basic Network Mode deployment, one VM has a standalone Security Management Server with a Security Gateway Virtual Edition to protect three networks. These networks connect using vSwitches.
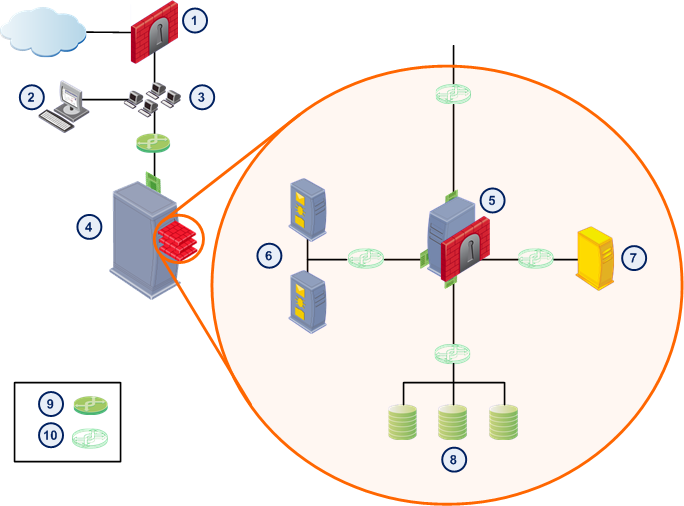
Callout
|
Description
|
|
|
Physical Security Gateway
|
|
|
SmartDashboard and vSphere client
|
|
|
LAN
|
|
|
ESX host
|
|
|
Security Gateway Virtual Edition VM
|
|
|
Web Servers
|
|
|
Email Server
|
|
|
Database Servers
|
|
|
Physical switch
|
|
|
vSwitch
|
The Security Gateway Virtual Edition inspects all traffic between virtual networks. For example, Security Gateway Virtual Edition inspects traffic between the Web server and database server VMs.
Administrators manage network security using SmartDashboard, which connects to the Security Management Server VM.
Network Mode Overview
Secures virtual environments and perimeter networks by deploying the Security Gateway Virtual Edition as a virtual network device (layer 2 or layer 3). To use Network Mode, the network topology must include or .
Licensing Security Gateway Virtual Edition
Each Security Gateway Virtual Edition instance requires its own license. You must purchase a license according to the number of physical cores on the local ESX host. Security Gateway Virtual Edition licenses are assigned to IP addresses.
Each Security Gateway and Security Management Server installed on a VM must have a license.
By default, Security Gateway Virtual Edition installs with a 15-day trial license.
ESX Host Security Considerations
We recommend that you read the VMware Best Practices - Security Hardening document for suggestions on how to secure your ESX host.
Check Point Best Practices:
|


