Multiple Entry Point VPNs
Overview of MEP
Multiple Entry Point (MEP) is a feature that provides a high availability and load sharing solution for VPN connections. A Security Gateway on which the VPN module is installed provides a single point of entry to the internal network. It is the Security Gateway that makes the internal network "available" to remote machines. If a Security Gateway should become unavailable, the internal network too, is no longer available. A MEPed environment has two or more Security Gateways both protecting and enabling access to the same VPN domain, providing peer Security Gateways with uninterrupted access.
VPN High Availability Using MEP or Clustering
Both MEP and Clustering are ways of achieving High Availability and load sharing. However:
- Unlike the members of a ClusterXL Security Gateway Cluster, there is no physical restriction on the location of MEPed Security Gateways. MEPed Security Gateways can be geographically separated machines. In a cluster, the clustered Security Gateways need to be in the same location, directly connected via a sync interface.
- MEPed Security Gateways can be managed by different Security Management servers; cluster members must be managed by the same Security Management server.
- In a MEP configuration there is no "state synchronization" between the MEPed Security Gateways. In a cluster, all of the Security Gateways hold the "state" of all the connections to the internal network. If one of the Security Gateways fails, the connection passes seamlessly over (performs failover) to another Security Gateway, and the connection continues. In a MEPed configuration, if a Security Gateway fails, the current connection is lost and one of the backup Security Gateways picks up the next connection.
- In a MEPed environment, the decision which Security Gateway to use is taken on the remote side; in a cluster, the decision is taken on the Security Gateway side.
Implementation
MEP is implemented via a proprietary Probing Protocol (PP) that sends special UDP RDP packets to port 259 to discover whether an IP is reachable. This protocol is proprietary to Check Point and does not conform to RDP as specified in RFC 908/1151.

|
Note - These UDP RDP packets are not encrypted, and only test the availability of a peer.
|
The peer continuously probes or polls all MEPed Security Gateways in order to discover which of the Security Gateways are "up", and chooses a Security Gateway according to the configured selection mechanism. Since RDP packets are constantly being sent, the status of all Security Gateways is known and updated when changes occur. As a result, all Security Gateways that are "up" are known.
There are two available methods to implement MEP:
- Explicit MEP - Only Star communities with more than one central Security Gateway can enable explicit MEP, providing multiple entry points to the network behind the Security Gateways. When available, Explicit MEP is the recommended method.
- Implicit MEP - Implicit MEP is supported in all scenarios where fully or partially overlapping encryption domains exist or where Primary-Backup Security Gateways are configured. When upgrading from a version prior to NGX (R60) where Implicit MEP was already configured, the settings previously configured will remain.
Explicit MEP
In a site to site Star VPN community, explicit MEP is configured via the community object. When MEP is enabled, the satellites consider the "unified" VPN domain of all the Security Gateways as the VPN domain for each Security Gateway. This unified VPN domain is considered the VPN domain of each Security Gateway:
In the figure, a Star VPN community has two central Security Gateways, M1 and M2 (for which MEP has been enabled) and three satellite Security Gateways — S1, S2, and S3. When S2 opens a connection with host-1 (which is behind M1 and M2), the session will be initiated through either M1 or M2. Priority amongst the MEP Security Gateways is determined by the MEP entry point selection mechanism.
If M2 is the selected entry point and becomes unavailable, the connection to host-1 fails over to M1. Returning packets will be rerouted using RIM or IP Pool NAT. For more information about returning packets, see Routing Return Packets.
There are four methods used to choose which of the Security Gateways will be used as the entry point for any given connection:
- Select the closest Security Gateway to source (First to respond)
- Select the closest Security Gateway to destination (By VPN domain)
- Random Selection (for Load distribution)
- Manually set priority list (MEP rules)
If either "By VPN domain" or "Manually set priority list" is selected, then Advanced options provide additional granularity.
MEP Selection Methods
- First to Respond, in which the first Security Gateway to reply to the peer Security Gateway is chosen. An organization would choose this option if, for example, the organization has two Security Gateways in a MEPed configuration - one in London, the other in New York. It makes sense for peers located in England to try the London Security Gateway first and the NY Security Gateway second. Being geographically closer to the peers in England, the London Security Gateway will be the first to respond, and becomes the entry point to the internal network. See: First to Respond.
- VPN Domain, is when the destination IP belongs to a particular VPN domain, the Security Gateway of that domain becomes the chosen entry point. This Security Gateway becomes the primary Security Gateway while other Security Gateways in the MEP configuration become its backup Security Gateways. See: By VPN Domain.
- Random Selection, in which the remote peer randomly selects a Security Gateway with which to open a VPN connection. For each IP source/destination address pair, a new Security Gateway is randomly selected. An organization might have a number of machines with equal performance abilities. In this case, it makes sense to enable load distribution. The machines are used in a random and equal way. See: Random Selection.
- Manually set priority list, Security Gateway priorities can be set manually for the entire community or for individual satellite Security Gateways. See: Manually Set Priority List.
First to Respond
When there is no primary Security Gateway, all Security Gateways share "equal priority". When all Security Gateways share equal priority:
- Remote peers send RDP packets to all the Security Gateways in the MEP configuration.
- The first Security Gateway to respond to the probing RDP packets gets chosen as the entry point to network. The idea behind first to respond is proximity. The Security Gateway which is "closer" to the remote peer responds first.
- A VPN tunnel is opened with the first to respond. All subsequent connections pass through the chosen Security Gateway.
- If the Security Gateway ceases to respond, a new Security Gateway is chosen.
By VPN Domain
Prior to enabling MEP, each IP address belonged to a specific VPN domain. Using By VPN Domain, the Security Gateway of that domain becomes the chosen entry point. In the figure, the VPN Star community has two central MEPed Security Gateways (M1 and M2, each of which have their own VPN domains), and remote satellite S1.
Host-2 (in the VPN domain of satellite S1 initiates a connection with host-1. The connection can be directed through either M1 or M2. However, host-1 is within M2's original VPN domain. For this reason, M2 is considered the Security Gateway "closest" to the destination IP Address. M2 is therefore considered the primary Security Gateway and M1 the backup Security Gateway for Host-1. If there were additional Security Gateways in the center, these Security Gateways would also be considered as backup Security Gateways for M2.
If the VPN domains have fully or partially overlapping encryption domains, then more than one Security Gateway will be chosen as the "closest" entry point to the network. As a result, more than one Security Gateway will be considered as "primary." When there are more than one primary or backup Security Gateways available, the Security Gateway is selected using an additional selection mechanism. This advanced selection mechanism can be either (See Advanced Settings):
- First to Respond
- Random Selection (for load distribution)
For return packets you can use RIM on the center Security Gateways. If RIM is also enabled, set a metric with a lower priority value for the leased line than the VPN tunnel. The satellite S1 might simultaneously have more than one VPN tunnel open with the MEPed Security Gateways, for example M2 as the chosen entry point for host-1 and M1 as the chosen entry point for host-3. While both M1 and M2 will publish routes to host-1 and host-3, the lower priority metric will ensure the leased line is used only when one of the Security Gateways goes down.
Random Selection
Using this method, a different Security Gateway is randomly selected as an entry point for incoming traffic. Evenly distributing the incoming traffic through all the available Security Gateways can help prevent one Security Gateway from becoming overwhelmed with too much incoming traffic.
The Security Gateways are probed with RDP packets, as in all other MEP configurations, to create a list of responding Security Gateways. A Security Gateway is randomly chosen from the list of responding Security Gateways. If a Security Gateway stops responding, another Security Gateway is (randomly) chosen.
A new Security Gateway is randomly selected for every source/destination IP pair. While the source and destination IP's remain the same, the connection continues through the chosen Security Gateway.
In such a configuration, RIM is not supported. IP Pool NAT must be enabled to ensure return packets are correctly routed through the chosen Security Gateway.
Manually Set Priority List
The Security Gateway that will be chosen (from the central Security Gateways in the star community) as the entry point to the core network can be controlled by manually setting a priority per source Security Gateway. Each priority constitutes a MEP Rule:
In the figure, three MEP members (M1, M2, M3) provide entry points to the network for three satellite Security Gateways (S1, S2, S3). Satellite S1 can be configured to try the Security Gateways in the following order: M1, M2, M3, giving the highest priority to M1, and the lowest priority to M3. Satellite S2 can be configured to try the Security Gateways in the following order: M2, M3 (but not to try M1).
Each of these priorities constitutes a MEP rule in the MEP manual priority list window:
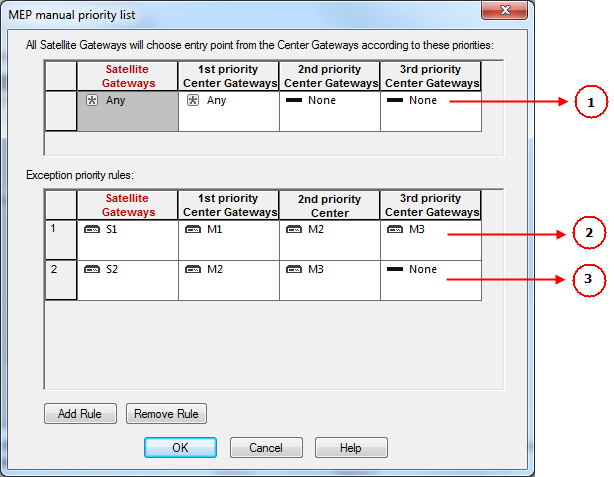
Item
|
Description
|
1
|
Default MEP Rule
|
2
|
First MEP Rule
|
3
|
Second MEP Rule
|
The MEP manual priority list window is divided into the default rule, and rules which provide exceptions to the default rule. The default MEP rule takes effect when:
- No MEP rules are defined
- When the source of the connection cannot be found in the Exception priority rules
The Exception priority rules section contains three priority levels: primary, secondary, and tertiary. While there are only three priority levels,
- The same priority can be assigned to several central Security Gateways
- The same rule can be assigned to several satellite Security Gateways
- A priority level can be left blank
In the second MEP rule below:
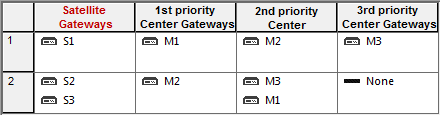
Central Security Gateways M3 and M1 have equal priority. The same rule is being applied to satellites S2 and S3.
When more than one Security Gateway is assigned the same priority level, which Security Gateway will be chosen is resolved according to the Advanced settings. See Advanced Settings.
Advanced Settings
In some instances, more than one Security Gateway is available in the center with no obvious priority between them. For example — as shown in Figure 12‑6 — more than one Security Gateway is assigned "second" priority. In this scenario, Advanced options are used to decide which Security Gateway is chosen: First to Respond, or Random Selection. (Choose Random selection to enable load balancing between the Security Gateways.)
When "manually set priority list" is the MEP selection mechanism, RIM is supported. RIM can be configured with "manually set priority list" because the "random selection" mechanism available on the Advanced button is different from the random selection mechanism used for MEP.
For the "random selection" mechanism employed for MEP, a different Security Gateway is selected for each IP source/destination pair. For the random selection mechanism available from the Advanced button, a single MEP entry point is randomly selected and then used for all connections, and does not change according to source/destination pair. Load distribution is therefore achieved since every satellite Security Gateway is randomly assigned a Security Gateway as its entry point. This makes it possible to enable RIM at the same time.
Tracking
If the tracking option is enabled for MEP, the following information is logged by each satellite Security Gateway:
- The resolved peer Security Gateway (a Security Gateway in the MEP)
- The priority of the resolved Security Gateway (primary, secondary, tertiary)
- Whether the resolved Security Gateway is responding
For example, in the scenario shown in the Manually Set Priority List section, satellite S1 opens a connection to the VPN domain that includes Security Gateways M1, M2, and M3. M1 is the resolved peer. If tracking is enabled, the log reads:
Resolved peer for tunnel from S1 to the MEP that contains M1, M2, and M3,
is: M1 (Primary Security Gateway, responding).
|
Implicit MEP
There are three methods to implement implicit MEP:
- First to Respond, in which the first Security Gateway to reply to the peer Security Gateway is chosen. An organization would choose this option if, for example, the organization has two Security Gateways in a MEPed configuration - one in London, the other in New York. It makes sense for VPN-1 peers located in England to try the London Security Gateway first and the NY Security Gateway second. Being geographically closer to VPN peers in England, the London Security Gateway is the first to respond, and becomes the entry point to the internal network. See: First to Respond.
- Primary-Backup, in which one or multiple backup Security Gateways provide "high availability" for a primary Security Gateway. The remote peer is configured to work with the primary Security Gateway, but switches to the backup Security Gateway if the primary goes down. An organization might decide to use this configuration if it has two machines in a MEP environment, one of which is stronger than the other. It makes sense to configure the stronger machine as the primary. Or perhaps both machines are the same in terms of strength of performance, but one has a cheaper or faster connection to the Internet. In this case, the machine with the better Internet connection should be configured as the primary. See: Primary-Backup Security Gateways.
- Load Distribution, in which the remote VPN peer randomly selects a Security Gateway with which to open a connection. For each IP source/destination address pair, a new Security Gateway is randomly selected. An organization might have a number of machines with equal performance abilities. In this case, it makes sense to enable load distribution. The machines are used in a random and equal way. See: Random Selection.
Implicit MEP is supported if the Security Gateways with overlapping encryption domains are in the same community. If they are located in different communities, only one of the Security Gateways will be used for this encryption domain.

|
Note - When upgrading from a version prior to NGX R60 where Implicit MEP was already configured, the settings previously configured will remain.
|
First to Respond
When there is no primary Security Gateway, all Security Gateways share "equal priority." When all Security Gateway's share "equal priority":
- Remote VPN peers send RDP packets to all the Security Gateways in the MEP configuration.
- The first Security Gateway to respond to the probing RDP packets gets chosen as the entry point to network. The idea behind first to respond is "proximity". The Security Gateway which is "closer" to the remote VPN peer responds first.
- A VPN tunnel is opened with the first to respond. All subsequent connections pass through the chosen Security Gateway.
- If the Security Gateway ceases to respond, a new Security Gateway is chosen.
In a star community, RDP packets are sent to the Security Gateways and the first to respond is used for routing only when:
There is more than one center Security Gateway, and
One of the following VPN routing options was selected:
In this scenario:
- MEP is not enabled on the community
- First to respond method is used
- Security Gateway X accesses VPN domain A through Security Gateway A
- Security Gateway X accesses VPN domain B through Security Gateway B
- Security Gateway X accesses VPN domain C through Security Gateway A or B
In a star community, RDP packets are sent to the Security Gateways and the first to respond is used for routing when:
There is more than one center Security Gateway, and
One of the following VPN routing options was selected:
Primary-Backup Security Gateways
Backup Security Gateways provide redundancy for primary Security Gateways. If the primary Security Gateway fails, connections go through the backup.
In this scenario:
The first Security Gateway is configured as the "primary," and the second Security Gateway as the "backup." If the primary Security Gateway fails, for whatever reason, the remote VPN peer detects that the link has gone down and works through the backup Security Gateway. The backup gateway inherits the complete VPN domain of the primary. Failover within an existing connection is not supported; the current connection is lost.
When the primary Security Gateway is restored, new connections go through the primary Security Gateway while connections that already exist will continue to work through the backup Security Gateway.

|
Note - When using the Primary-Backup Security Gateways method, the encryption domains should not overlap
|
Load Distribution
To prevent any one Security Gateway from being flooded with connections, the connections can be evenly shared amongst all the Security Gateways to distribute the load. When all Security Gateways share equal priority (no primary) and are MEPed to the same VPN domain, it is possible to enable load distribution between the Security Gateways. The Security Gateways are probed with RDP packets, as in all other MEP configurations, to create a list of responding Security Gateways. A Security Gateway is randomly chosen from the list of responding Security Gateways. If a Security Gateways stops responding, a new Security Gateway is (randomly) chosen.
A new Security Gateway is randomly selected for every source/destination IP pair. While the source and destination IP's remain the same, the connection continues through the chosen Security Gateway.
Routing Return Packets
To make sure return packets are routed correctly, the MEPed Security Gateway can make use of either:
- IP pool NAT (static NAT) or
- Route Injection Mechanism
IP Pool Network Address Translation (NAT)
IP pool NAT is a type of NAT in which source IP addresses from remote VPN domains are mapped to an IP address drawing from a pool of registered IP addresses. In order to maintain symmetric sessions using MEPed Security Gateways, the MEPed Security Gateway performs NAT using a range of IP addresses dedicated to that specific Security Gateway and should be routed within the internal network to the originating Security Gateway. When the returning packets reach the Security Gateway, the Security Gateway restores the original source IP address and forwards the packets to the source.
RIM
Route Injection Mechanism (RIM) enables a Security Gateway to use a dynamic routing protocol to propagate the encryption domain of a VPN peer Security Gateway to the internal network. When a VPN tunnel is created, RIM updates the local routing table of the Security Gateway to include the encryption domain of the VPN peer.
When a tunnel to a MEPed Security Gateway goes down, the Security Gateway removes the appropriate "return route" from its own local routing table. This change is then distributed backwards to the routers behind the Security Gateway.
RIM is based both on the ability of the Security Gateway to update its local routing table, and the presence of the a dynamic routing protocol to distribute the change to the network behind the Security Gateway. There is little sense in enabling RIM on the Security Gateway if a dynamic routing protocol is not available to distribute changes.
When MEP is enabled, RIM can be enabled only if permanent tunnels are enabled for the whole community. In a MEP configuration RIM is available when using the First to Respond, Manual set priority list, and VPN Domain mechanisms. In the first two options, satellite Security Gateways "see" the center Security Gateways as unified as if one tunnel is connecting them. As a result, only the chosen MEP Security Gateway will inject the routes. In VPN Domain MEP, it could be that all MEP Security Gateways will inject the routes, which requires configuring the routers behind the MEP Security Gateways to return packets to the correct Security Gateway.
RIM is not available when Random Selection is the selected entry point mechanism.
For more information on RIM, see Route Injection Mechanism.
Special Considerations
- If one of the central Security Gateways is an externally managed Security Gateway:
- The VPN domain of the central Security Gateways will not be automatically inherited by an externally managed Security Gateway
- The RIM configuration will not be automatically downloaded
- UTM-1 Edge Security Gateways cannot be configured as a MEP Security Gateway but can connect to MEPed Security Gateways.
- DAIP Security Gateways require DNS resolving in order to be configured as MEP Security Gateways.
Configuring MEP
To configure MEP, decide on:
- The MEP method
- If required, method for returning reply packets:
Configuring Explicit MEP
Explicit MEP is only available in Site-to-Site Star VPN communities where multiple central Security Gateways are defined.
To configure MEP:
- Open the Star Community properties page > Advanced Settings > MEP (Multiple Entry Point): Select Enable center Security Gateways as MEP.
- Select an entry point mechanism:
- First to respond
- By VPN domain
- Random selection
- Manual priority list
If "By VPN domain" or "Manually set priority list" is selected, click Advanced to resolve how more than one Security Gateway with equal priority should be selected.
If "Manually set priority list" is selected, click Set to create a series of MEP rules.
- Select a tracking option, if required.
Configuring Implicit MEP
Configuring Implicit First to Respond
When more than one Security Gateway leads to the same (overlapping) VPN domain, they are in a MEP configuration. The first Security Gateway to respond is chosen. To configure first to respond, define that part of the network that is shared by all the Security Gateways into a single group and assign that group as the VPN domain.
Before you start, make sure that is not enabled:
- In SmartDashboard, go to > > > .
- Clear the option.
To configure First to Respond MEP:
- For each Security Gateway in the VPN domain, run
vpn overlap_encdom - In SmartDashboard, create a host group and assign all these Security Gateways to it.
- In the window for each Security Gateway object go to the Topology page.
- In the section, select .
- Select the host group of MEP gateways that you defined in step 2.
- Click .
- Install policy on all Security Gateways.
Configuring Implicit Primary-Backup
Configure the VPN Domain that includes the Primary gateway and another domain that includes only the backup gateway. Configure each gateway as either the Primary gateway or a backup gateway.
To configure the primary gateway:
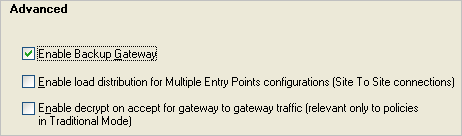
- Open Global Properties window > VPN > Advanced, select Enable Backup Gateway.
- In the network objects tree, Groups section, create a group of gateways to act as backup gateways.
- Open the VPN properties of the Primary gateway:
- NGX R65 and R70: Gateway properties > VPN
- R71 and higher: Gateway properties >IPSec VPN
- Select Use Backup Gateways, and select the group of backup gateways.
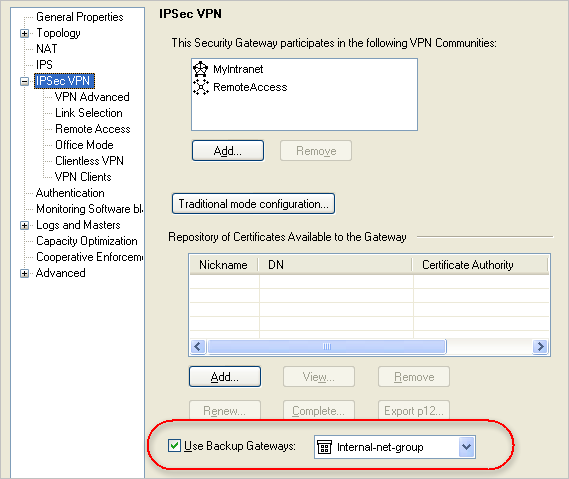
This gateway is the primary gateway for this VPN domain.
- For each backup gateway, make a VPN domain that does not include IP addresses that are in the Primary VPN domain or the other backup domains.
If the backup gateway already has a VPN domain, you must make sure that its IP addresses do not overlap with the other VPN domains.
- Create a group of IP addresses not in the other domains, or a group that consists of only the backup gateway.
- On the Properties window of the backup network object > Topology > VPN Domain section, select Manually defined.
- Select the group.
- Click OK.
- Install the policy.
Configuring Implicit Load Distribution
To configure implicit MEP for random gateway selection:
- Open Global Properties.
- Open IPSec VPN > Advanced (or VPN > Advanced).
- Select Enable load distribution for Multiple Entry Point configurations (Site to Site connections).
- Define the same VPN domain for all the gateways:
- Create a group of the gateways.
- On the Properties window of each gateway network object > Topology > VPN Domain section, select Manually defined.
- Select the group.
- Click OK.
- Install the policy.
Configuring IP Pool NAT
To configure IP pool NAT:
- In Global Properties > NAT page, select Enable IP Pool NAT.
- Set tracking options for address exhaustion and for address allocation and release. Then:
- For each Security Gateway, create a network object that represents the IP pool NAT addresses for that Security Gateway. The IP pool can be a network, group, or address range. For example:
- On the network objects tree, right-click Network Objects branch > New > Address Range... The Address Range Properties window opens.
- On the General tab, enter the first IP and last IP of the address range.
- Click OK. In the network objects tree, Address Ranges branch, the new address range appears.
- On the Security Gateway object where IP pool NAT translation is performed, Security Gateway Properties window, NAT > IP Pool NAT page, select either
- Allocate IP Addresses from, and select the address range you created, OR
- Define IP Pool addresses on Security Gateway interfaces. If you choose this option, you need to define the IP Pool on each required interface, in the Interface Properties window, IP Pool NAT tab.
- In the IP Pool NAT page, select either (or all):
- Use IP Pool NAT for VPN clients connections
- Use IP Pool NAT for Security Gateway to Security Gateway connections
- Prefer IP Pool NAT over Hide NAT
- Click Advanced...
- Decide after how many minutes unused addressees are returned to the IP pool.
- Click OK twice.
- Edit the routing table for each internal router, so that packets with an IP address assigned from the NAT pool are routed to the appropriate Security Gateway.
|
|


