Configuring UEM to Deploy the Harmony Mobile Protect app
Use Microsoft Intune UEM![]() Unified Endpoint Management. An architecture and approach that controls different types of devices such as computers, smartphones and IoT devices from a centralized command point. to deploy Harmony Mobile Protect app and keep the device protected. If Harmony Mobile Protect app is not installed or removed from device, the device is marked as not protected.
Unified Endpoint Management. An architecture and approach that controls different types of devices such as computers, smartphones and IoT devices from a centralized command point. to deploy Harmony Mobile Protect app and keep the device protected. If Harmony Mobile Protect app is not installed or removed from device, the device is marked as not protected.

|
Notes -
|
General Workflow:
-
If you selected Automatic integration in Configuring UEM Integration Settings, continue with Creating a Compliance Policy for the Organization Devices.
-
If you selected Manual integration in Configuring UEM Integration Settings:
Adding the Harmony Mobile Protect app to your App Catalog
To protect your devices, deploy the Harmony Mobile Protect app from the public stores to your devices.
You must add the Harmony Mobile Protect app for both iOS and Android operating systems.
For more information about adding apps to the Microsoft Intune App Catalog, see the Microsoft Intune online guide.

|
Notes:
|
Import Mobile Security Harmony Mobile Protect to Intune:
-
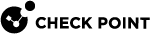
In the Microsoft Intune Admin Center, go to Apps > All Apps and click Create.
-
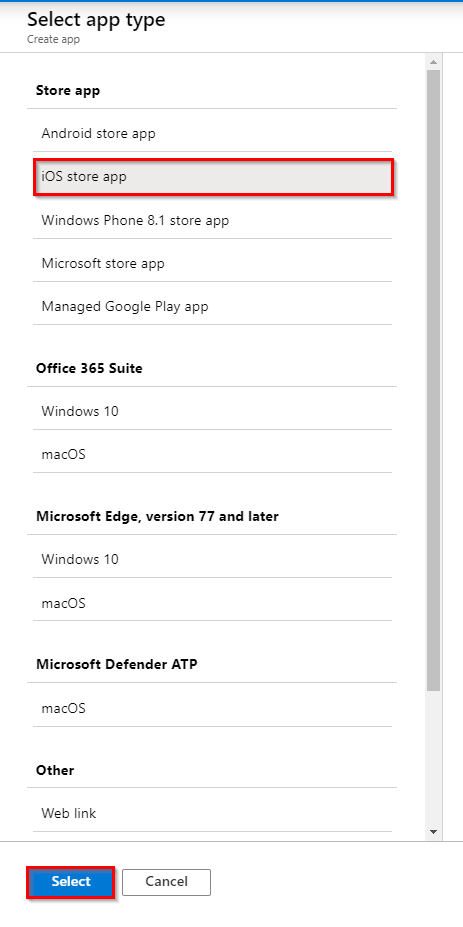
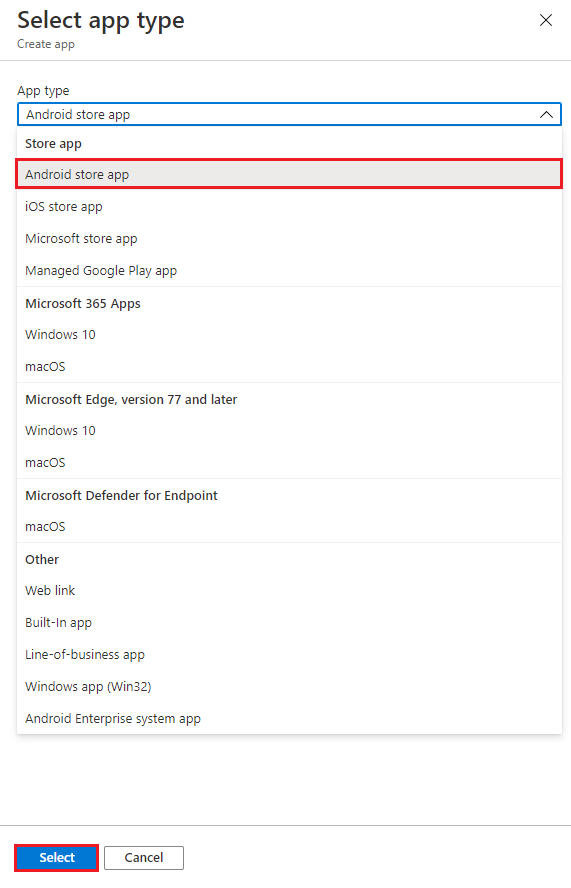
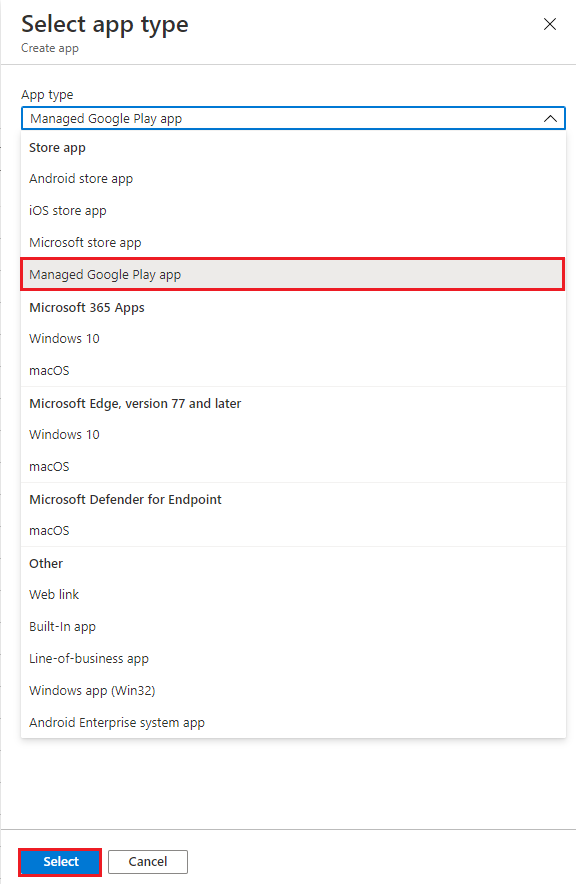
On the right panel, select the App type.
-
Select App type as iOS store app and click Select.
-
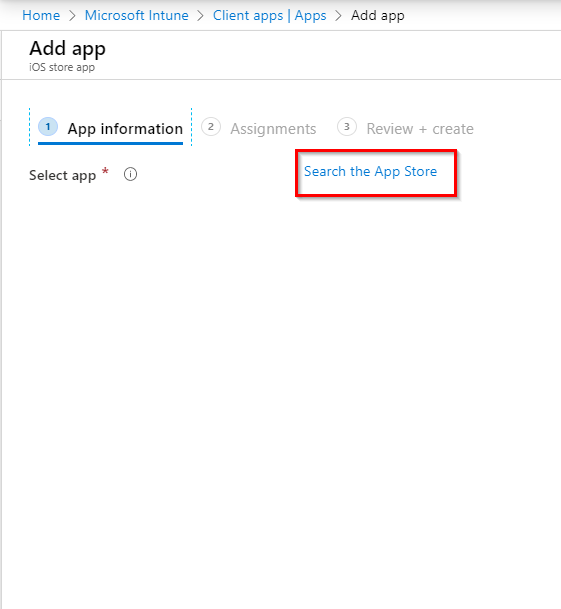
In the App information tab, click Search the App Store.
-
Search for Mobile Security Protect application. Click the application and click Select.
The App information section displays the information about the app.

-
Click Next.
-
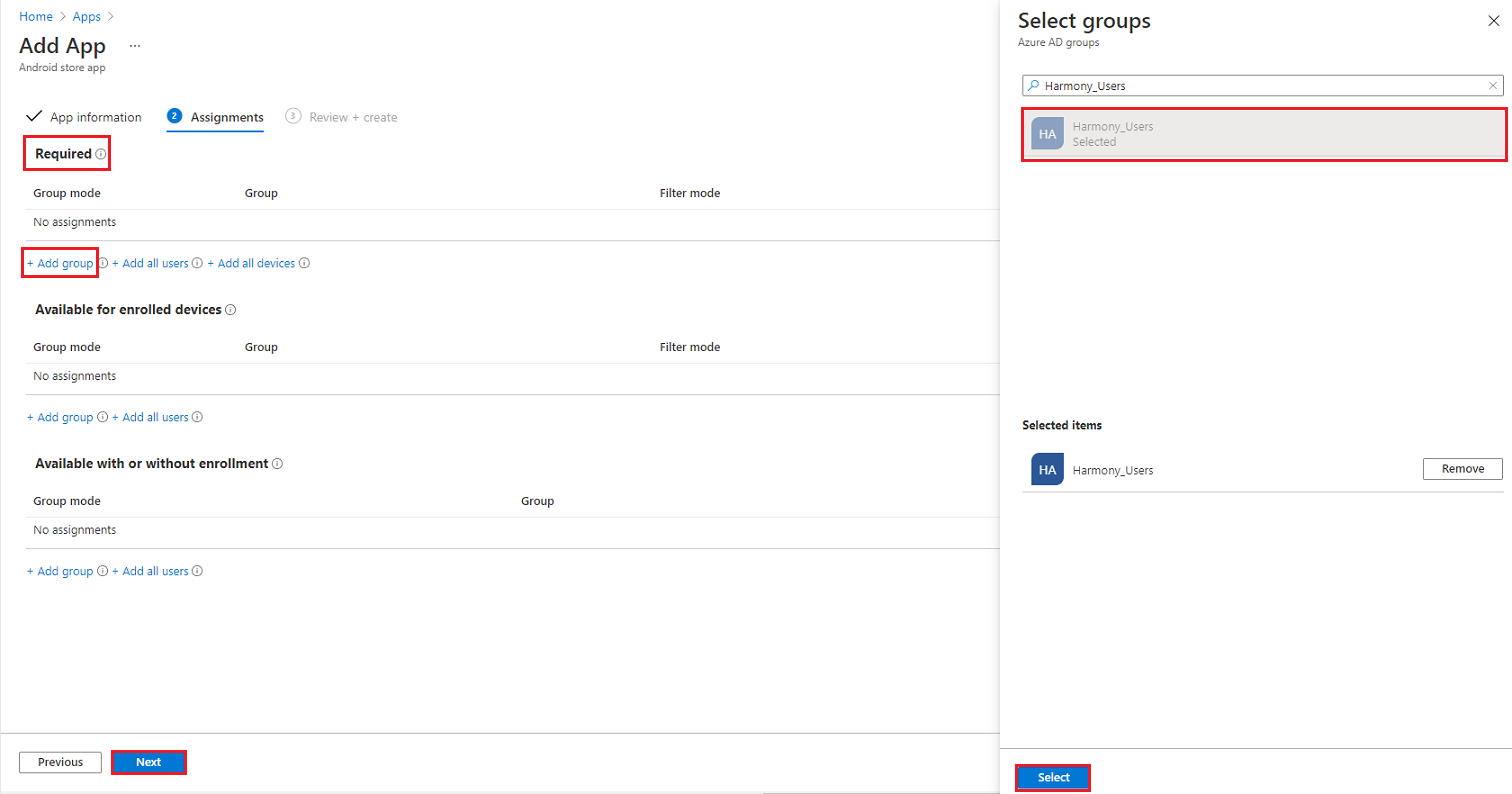
In the Assignments tab, under Required, select +Add group.
-
Search and select the security group you created.
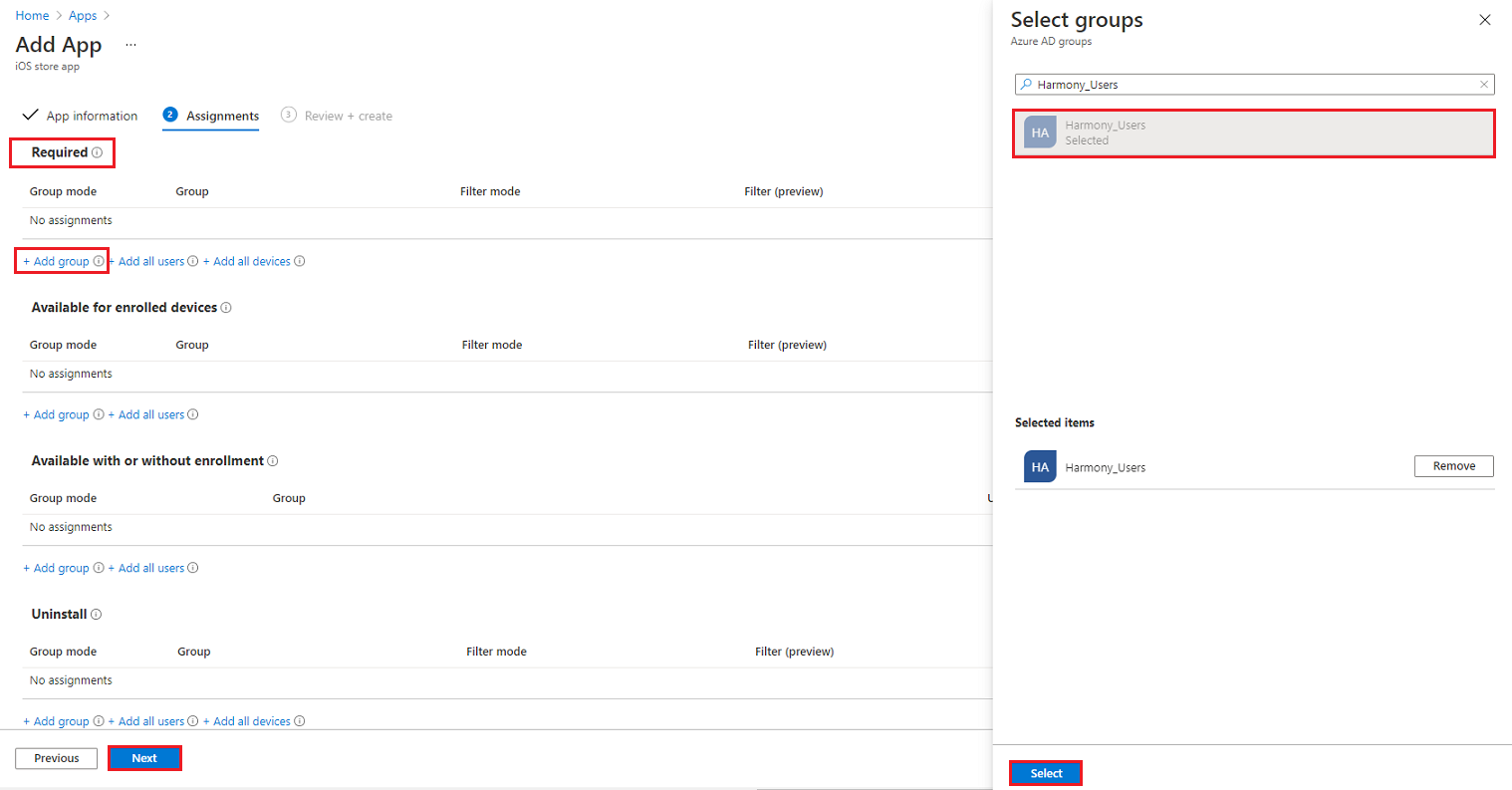
- Click Next.
-
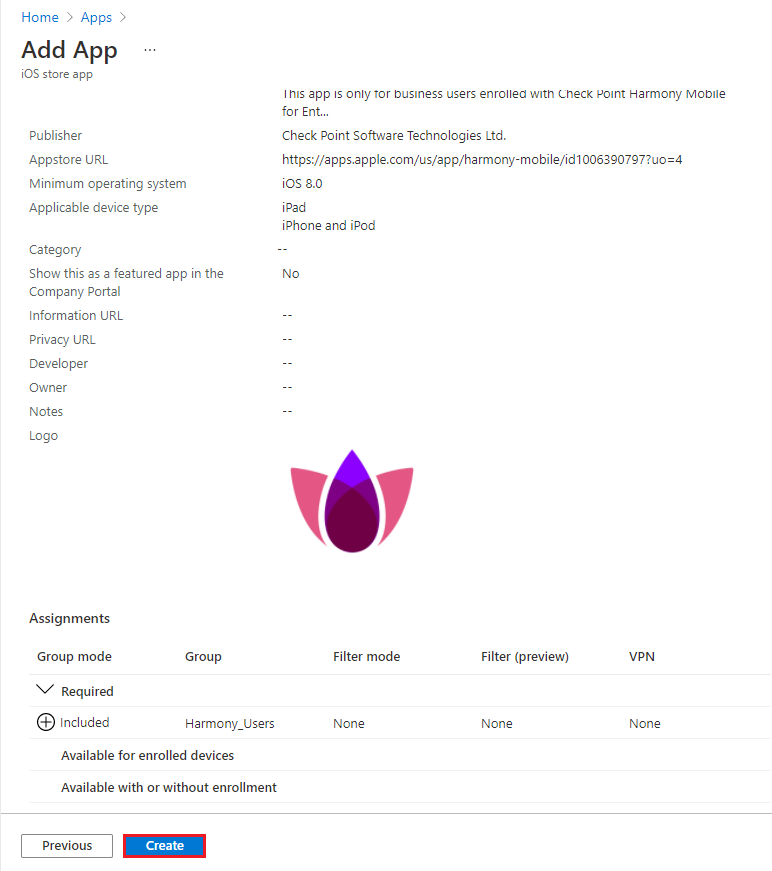
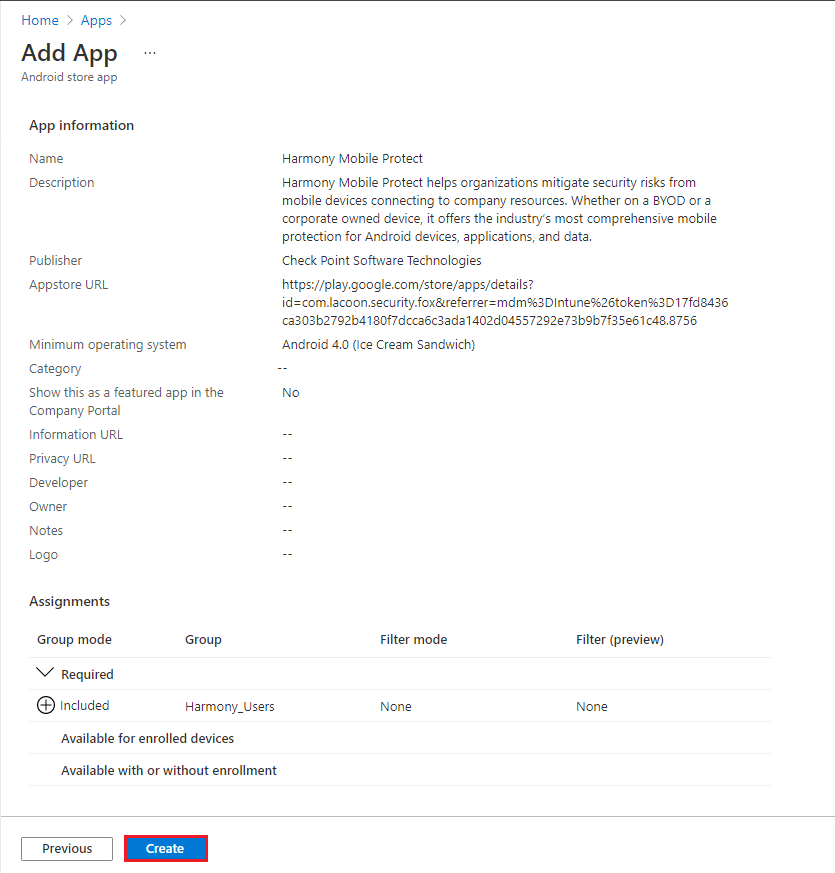
In the Review + create section, review the details and click Create.
-
Select App type as Android store app and click Select.
-
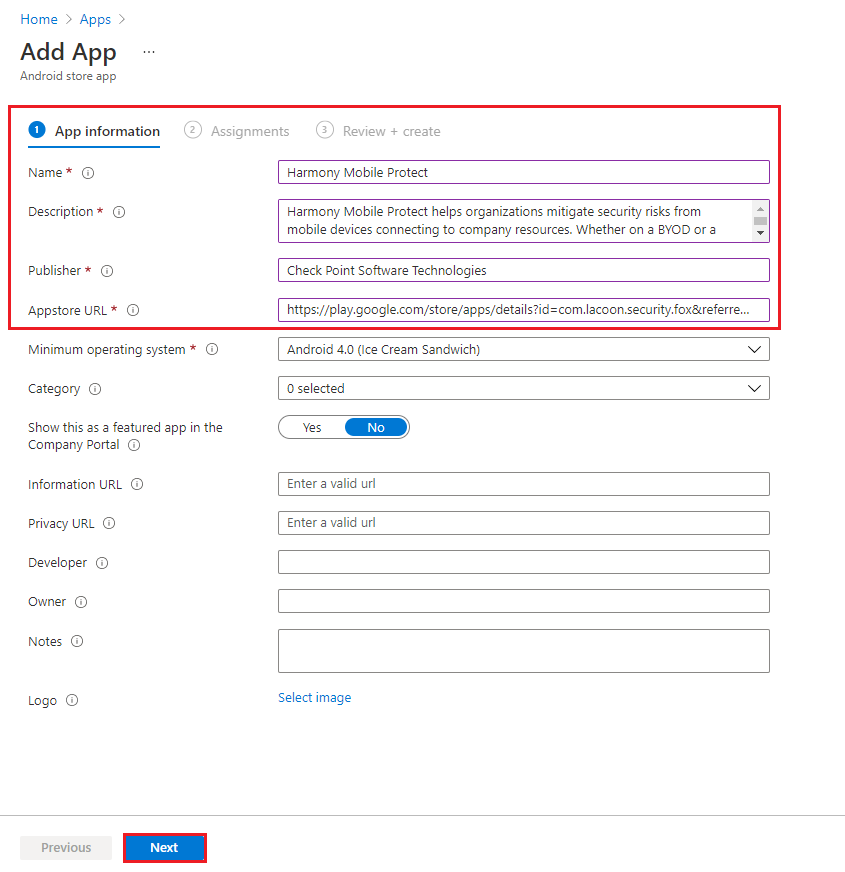
In the App information tab:
-
In the Name field, enter Mobile Security Protect.
-
Enter a description, as listed in the app store description.
-
In the Publisher field, enter Check Point Software Technologies.
-
For the Appstore URL, build the URL for Mobile Security Protect Android:
-
In the Mobile Security dashboard, go to Settings > Integrations.
In the Deployment section, copy the token of your dashboard. See Configuring UEM Integration Settings > Deployment configuration.
-
Concatenate the above Token to the end string of this URL that points to Mobile Security Protect Android Google Play store:
"https://play.google.com/store/apps/details?id=com.lacoon.security.fox&referrer=UEM%3DIntune%26token%3D{Token}"Enter this as the Appstore URL.
-
-
-
Click Next.
-
In the Assignments tab, under Required, select +Add group.
Select the security group created before and click Select.
-
Click Next.
-
Review and click Create.
-
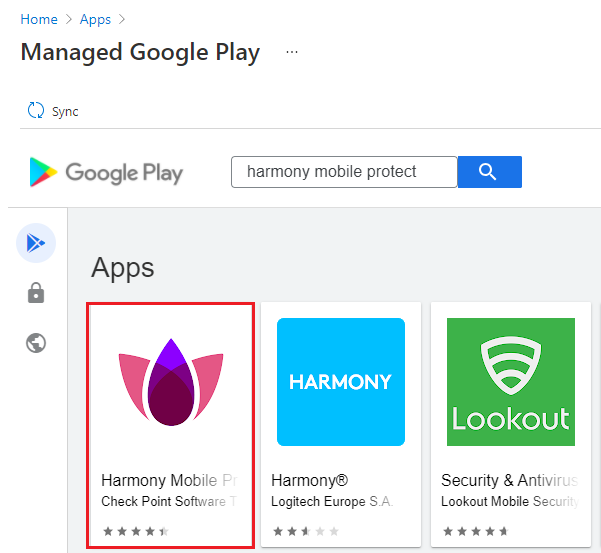
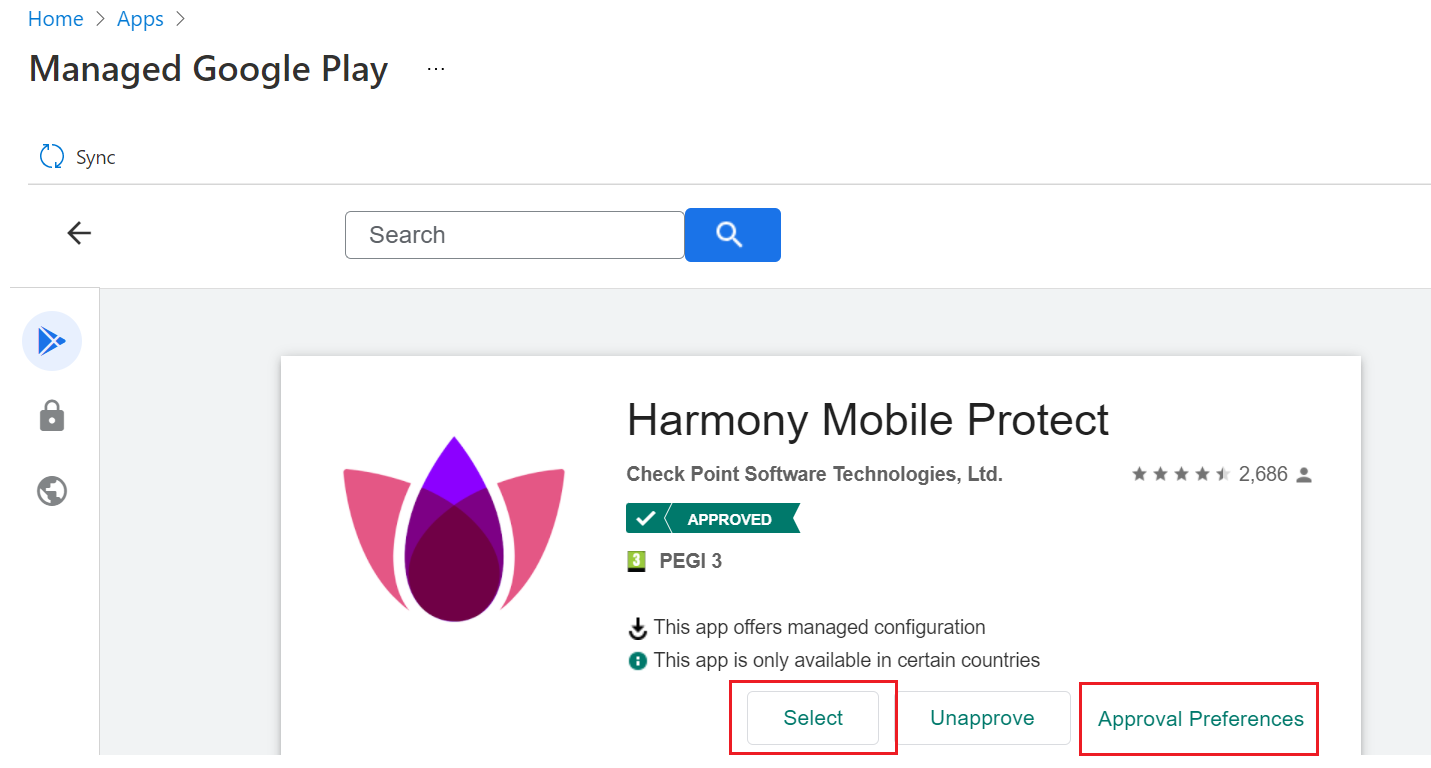
Select App type as Managed Google Play app and click Select.
-
Search and select Mobile Security Protect.
-
Click Select.
-
Click Sync.
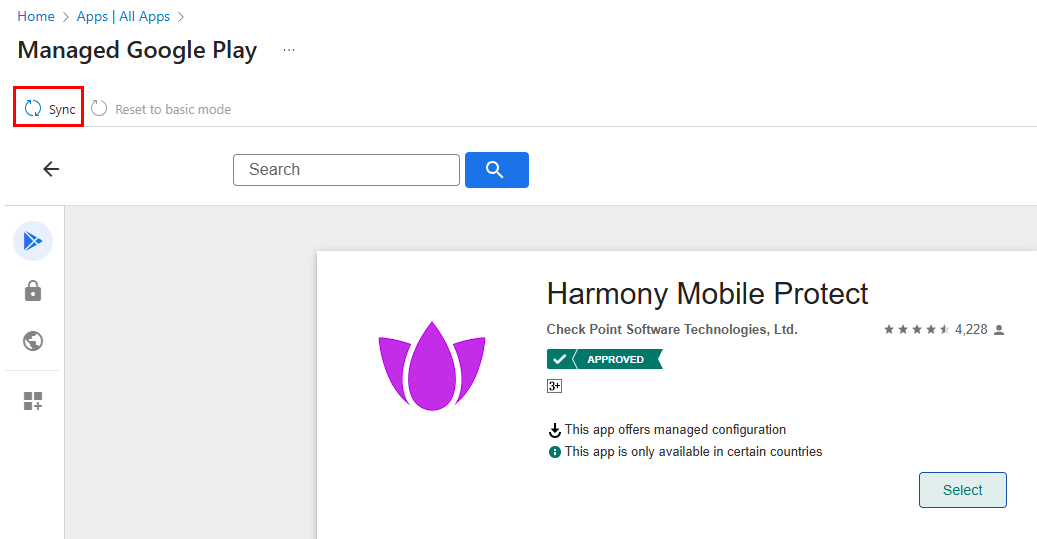
After successful sync, the system adds the Harmony Mobile Protect app in Managed Google Play to the All Apps page.
-
Review the changes and click Save.
Configuring the Application Configuration Settings
To auto-register the Harmony Mobile Protect app on devices to the Mobile Security dashboard, we use App Configuration Policy to send registration parameters to the device and to the Mobile Security gateway.
-
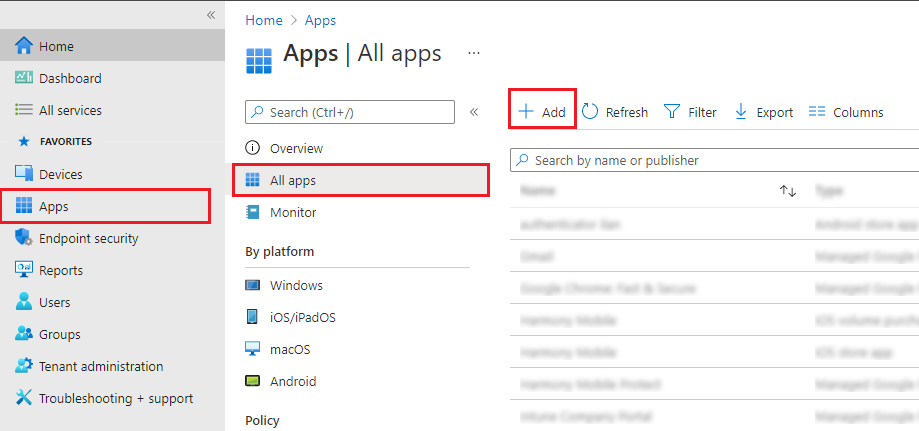
In the Microsoft Intune Admin Center, go to Apps > All Apps > Manage apps > Configuration.
-
Click Create and select Managed devices.
-
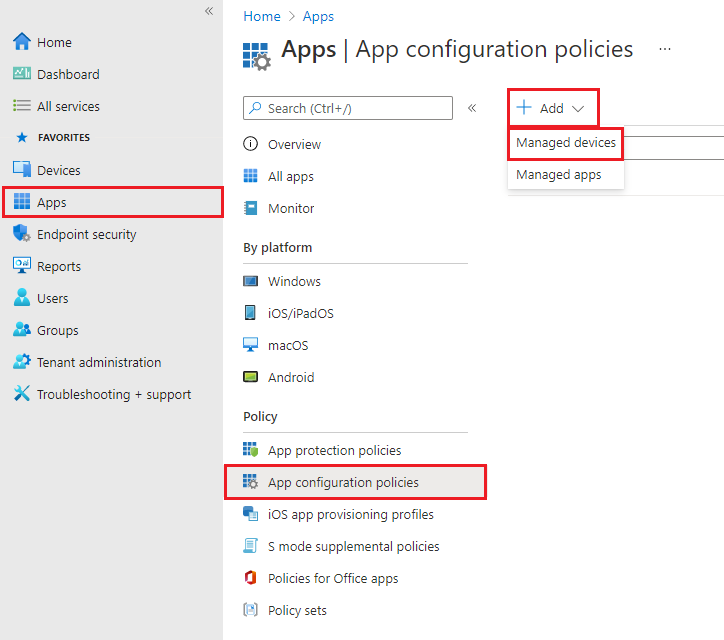
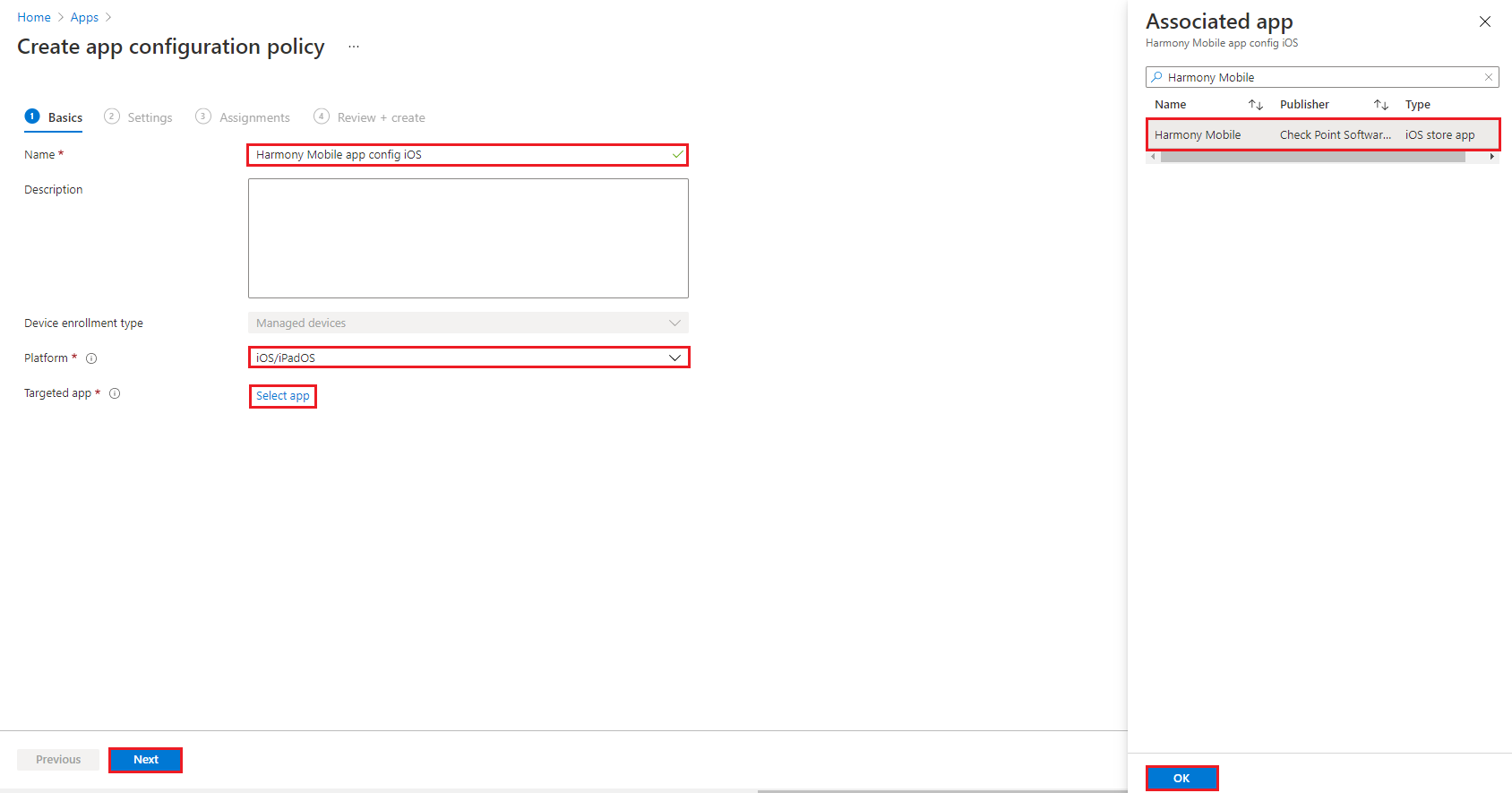
 For iOS App
For iOS App
-
In the Name field, enter a name for your app configuration (example, Harmony Mobile app Config iOS).
-
From the Platform list, select iOS/iPadOS.
-
In Targeted app, click Select app.
-
On the side panel, search and select Mobile Security Protect.
-
Click OK.
-
Click Next.
-
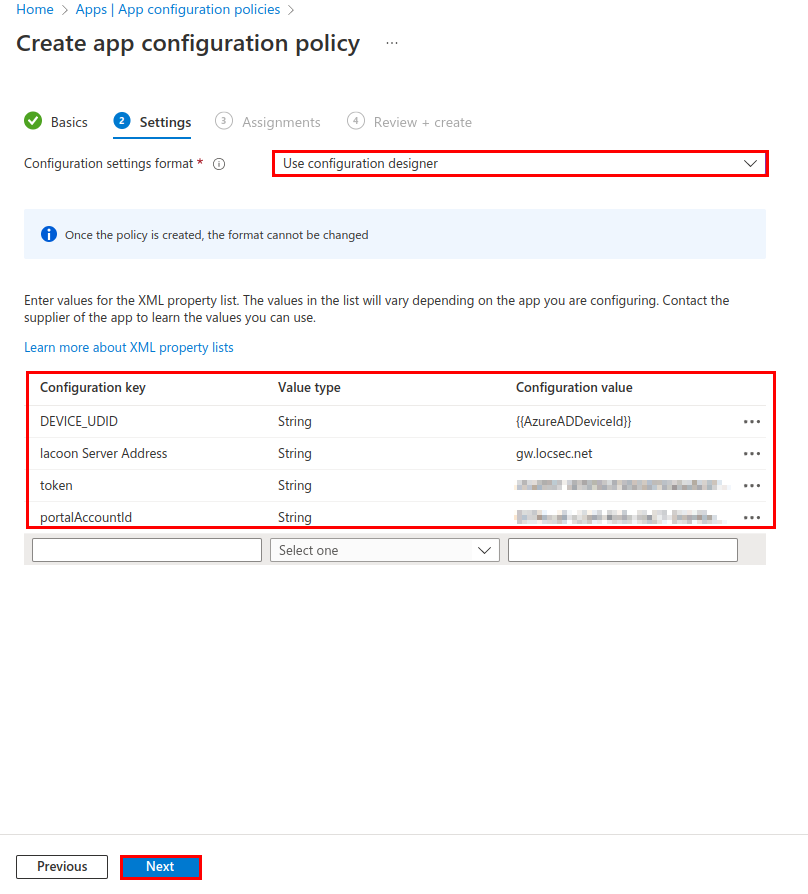
In Configuration Settings format, select Use configuration designer.
-
Add the configuration values from the table below:

Note - It is highly recommended to copy and paste the Configuration Key and Configuration Value directly from the table where applicable.
Configuration Key
Value Type
Configuration Value
DEVICE_UDID
String
{{AzureADDeviceId}}
token
String
Dashboard ID Hash *
Lacoon Server Address
String
Enter the Security Gateway
 Dedicated Check Point server that runs Check Point software to inspect traffic and enforce Security Policies for connected network resources. server for your region:
Dedicated Check Point server that runs Check Point software to inspect traffic and enforce Security Policies for connected network resources. server for your region:Region
Server
US
gw.locsec.net
Ireland (EU region)
eu-gw.locsec.net
Australia (Asia region)
au-gw.locsec.net
Canada (Canada)
ca-gw.locsec.net
UK region (UK)
uk-gw.locsec.net
India
in-gw.locsec.net
portalAccountId
String
Account ID of the application in the Check Point Portal.
ios_dep_notification_permission
(Enable this key to grant Zero Touch notification permissions for iOS)
Boolean
true
* For the token key , in the Mobile Security dashboard:
-
Go to Settings > Integrations.
-
In the Deployment section, click Edit
 .
. -
Copy the token of your dashboard. See Configuring Deployment.
-
-
After entering the values, click Next.
-
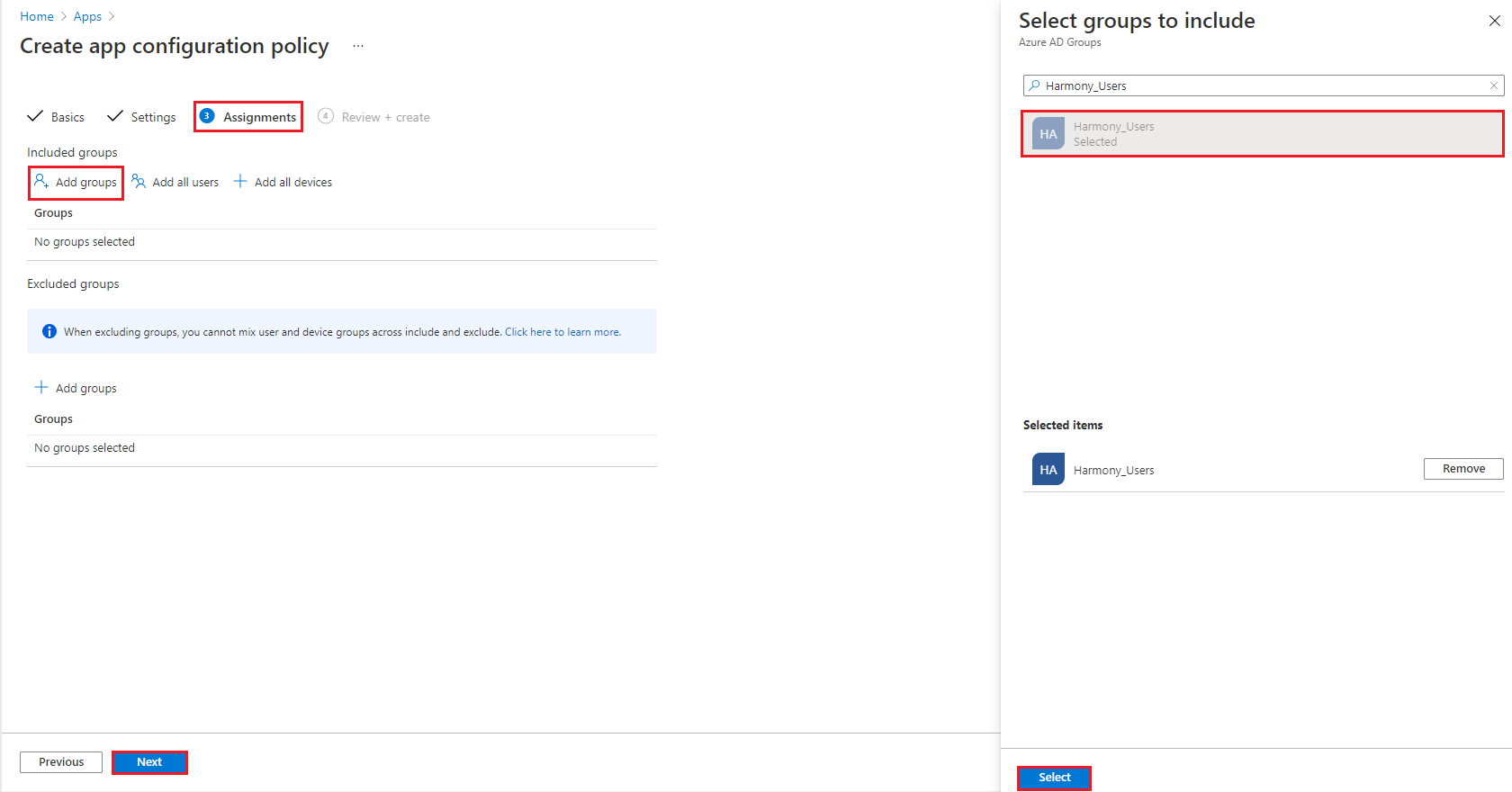
In the Assignments tab, under Included groups, click Add groups.
-
Search and select the security group you want to associate the app configuration with.
-
Click Next.
-
Review the policy configuration and click Create.
-
-
 For Android Enterprise App
For Android Enterprise App
-
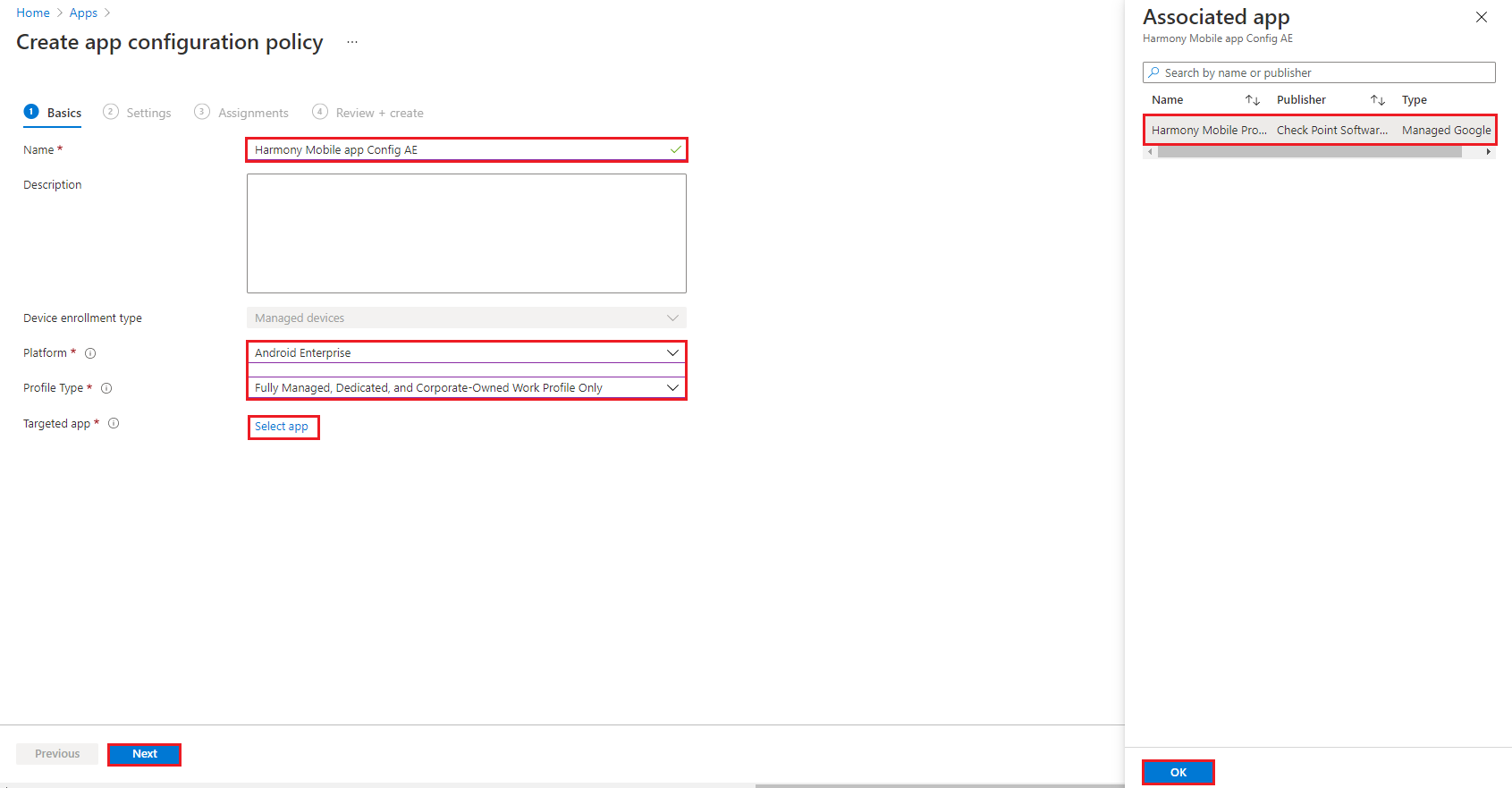
In the Name field, enter a name for your app configuration (example, Harmony Mobile app Config AE).
-
From the Platform list, select Android Enterprise.
-
From the Profile Type list, select one of these:
-
Fully Managed, Dedicated, and Corporate-Owned Work Profile Only
-
Personally-Owned Work Profile Only

Note - It is important to select the correct profile type to ensure it is pushed to the device and allow the automatic activation of Mobile Security.
-
-
In Targeted app, click Select app.
-
On the side panel, search and select Mobile SecurityProtect.
-
Click OK.
-
Click Next.
-
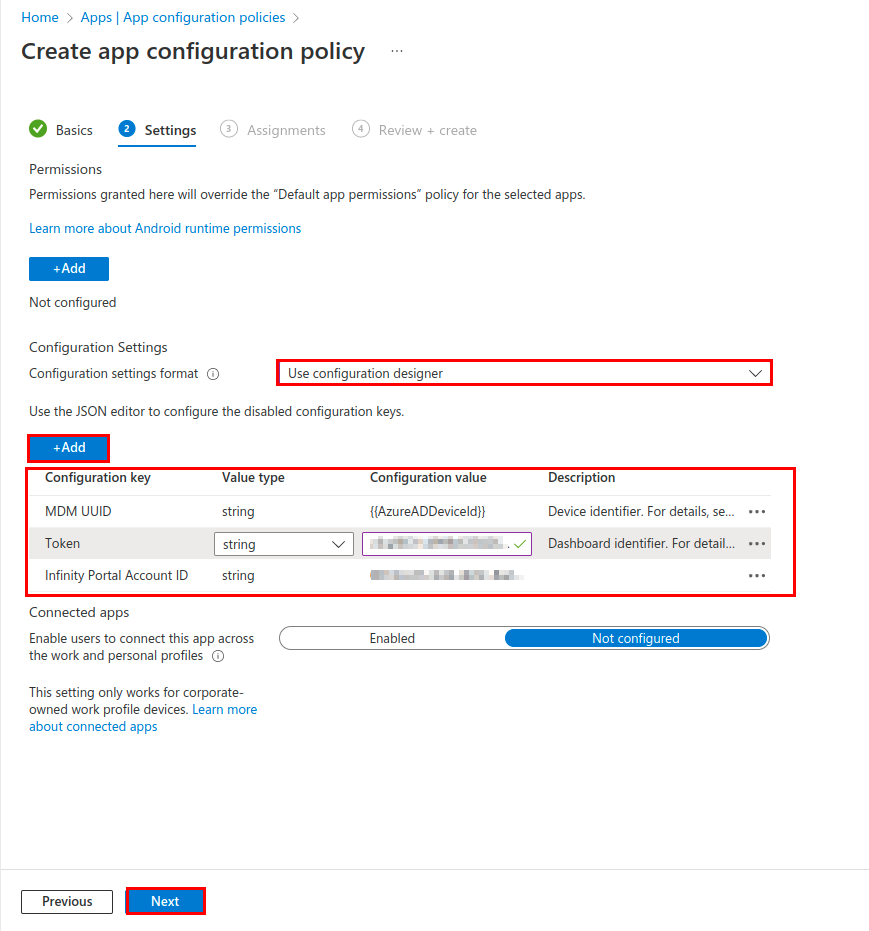
In the Settings tab, under Configuration Settings, select Configuration settings format as Use configuration designer.

Note - It is highly recommended to copy and paste the Configuration Value directly from the table where applicable.
-
Click +Add.
-
Add the configuration keys according to this table:
Configuration Key
Value Type
Configuration Value
MDM
 Mobile Device Manager. A security software that enable organizations to implement policies that secure, monitor, and manage end-user mobile devices. UUID
Mobile Device Manager. A security software that enable organizations to implement policies that secure, monitor, and manage end-user mobile devices. UUID Universal Unique Identifier. A UUID is a 128-bit value used to uniquely identify an object or entity on the internet.
Universal Unique Identifier. A UUID is a 128-bit value used to uniquely identify an object or entity on the internet.String
{{AzureADDeviceId}}
GW Address
String
Enter the Security Gateway server for your region:
Region
Server
US
gw.locsec.net
Ireland (EU region)
eu-gw.locsec.net
Australia (Asia region)
au-gw.locsec.net
Canada (Canada)
ca-gw.locsec.net
UK region (UK)
uk-gw.locsec.net
India
in-gw.locsec.net
Token
String
Dashboard ID Hash *
portalAccountId
String
Account ID of the application in the Check Point Portal.
* For the token key , in the Mobile Security dashboard:
-
Go to Settings > Integrations.
-
In the Deployment section, click Edit
 .
. -
Copy the token of your dashboard. See Configuring Deployment.
-
-
After entering the values, click Next.
-
In the Assignments tab, under Included groups, click Add groups.
-
Search and select the security group you want to associate the app configuration with.
-
Click Next.
-
Review the policy configuration and click Create.
-
Creating a Compliance Policy for the Organization Devices
Compliance![]() Check Point Software Blade on a Management Server to view and apply the Security Best Practices to the managed Security Gateways. This Software Blade includes a library of Check Point-defined Security Best Practices to use as a baseline for good Security Gateway and Policy configuration. Policies are activated on devices that did not install the required apps. The Harmony Mobile Protect app defines the security levels for the devices. You select the security level that marks the device as Not Compliant with company policy.
Check Point Software Blade on a Management Server to view and apply the Security Best Practices to the managed Security Gateways. This Software Blade includes a library of Check Point-defined Security Best Practices to use as a baseline for good Security Gateway and Policy configuration. Policies are activated on devices that did not install the required apps. The Harmony Mobile Protect app defines the security levels for the devices. You select the security level that marks the device as Not Compliant with company policy.
You must create separate compliance policies for specific OS types, such as iOS and Android.

|
Note - In every organization, the customer configures the compliance policies according to the production environment, needs, and the internal security policy |
For more information about Intune compliance policy, see the Microsoft Intune online guide.
To create a Compliance Policy:
-
In the Microsoft Intune Admin Center, go to Devices > Manage devices > Compliance > Policies.
-
Click Create policy.
-
In the Create a Policy panel, select a platform.

Note - The data fields are similar for both iOS and Android platforms.
-
Click Create.
-
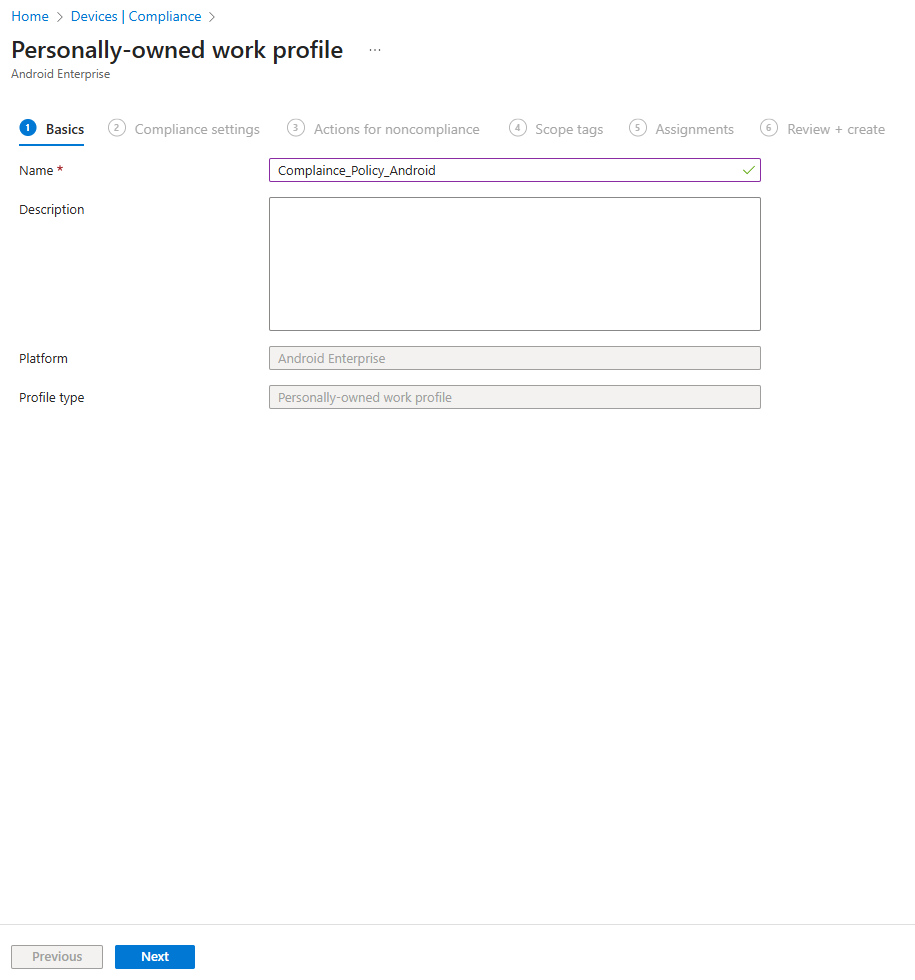
In the Basics tab, enter a name for your policy.
-
Click Next.
-
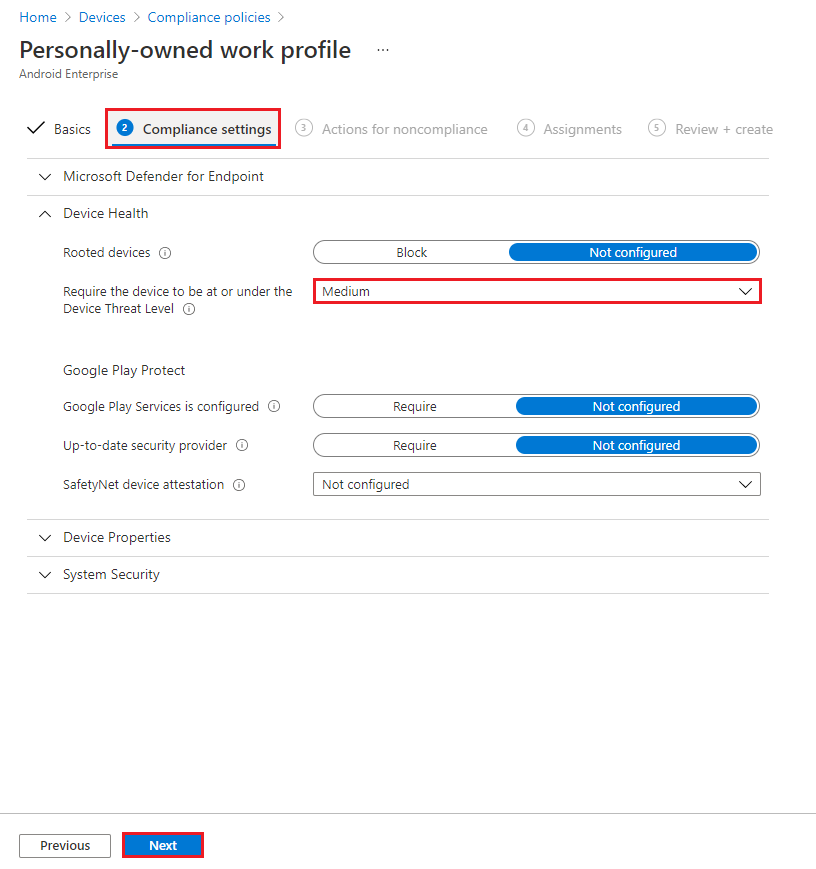
In the Compliance settings tab, go to Device Health and select Require the device to be at or under the Device Threat Level as Medium (recommended).
This setting makes your device as non-compliant if its risk level detected by the MTD app (Check Point Mobile Security) is High. The table below lists the different device threat levels:
Device Health Level
Description
Secured
This is the most secure. The device cannot have any threats present and still access company resources. If any threats are found, the device is evaluated as non-compliant.
Low
The device is compliant only if Low level threats are present. Anything higher puts the device in a non-compliant status.
Medium
The device is compliant if the threats found on the device are Low or Medium level. If High level threats are detected, the device is determined as non-compliant.
High
This is the least secure. This allows all threat levels, and uses Mobile Threat Defense for reporting purposes only. Devices are required to have the MTD app activated with this setting.
-
Click Next.
-
In the Assignments tab, under Included groups, click Add groups.
-
Search and select the relevant security group to apply this policy.
-
Review and create the policy.