


In This Section: |
Network Objects, defined in SmartConsole and stored in the proprietary Check Point object database, represent physical and virtual network components (such as gateways, servers, and users), and logical components (such as IP address ranges and Dynamic Objects). Before you create Network Objects, analyze the needs of your organization:
Objects in SmartConsole represent networks, devices, protocols and resources. SmartConsole divides objects into these categories:
Icon |
Object Type |
Examples |
|---|---|---|
|
Network Objects |
Gateways, hosts, networks, address ranges, dynamic objects, security zones |
|
Services |
Services, Service groups |
|
Custom Applications/Sites |
Applications, Categories, Mobile applications |
|
VPN Communities |
Site to Site or Remote Access communities |
|
Users |
Users, user groups, and user templates |
|
Data Types |
International Bank Account Number - IBAN, HIPAA - Medical Record Number - MRN, Source Code. |
|
Servers |
Trusted Certificate Authorities, RADIUS, TACACS |
|
Time Objects |
Time, Time groups |
|
UserCheck Interactions |
Message windows: Ask, Cancel, Certificate Template, Inform, and Drop |
|
Limit |
Download and upload bandwidth |
You can add, edit, delete, and clone objects. A clone is a copy of the original object, with a different name. You can also replace one object in the Policy with another object.
Note - Do not create two objects with the same name. You will see a validation error when you try to publish. To resolve, change one of the object names.
To work with objects, right-click the object in the object tree or in the Object Explorer, and select the action.
You can delete objects that are not used, and you can find out where an object is used.
To clone an object:
The Clone Object window opens.
To find out where an object is used:
In the object tree or in the Object Explorer, right-click the object and select Where Used.
To replace an object with a different object:
To delete all instances of an object:
Object tags are keywords or labels that you can assign to the network objects or groups of objects for search purposes. These are the types of tags you can assign:
Each tag has a name and a value. The value can be static, or dynamically filled by detection engines.
To add a tag to an object:
The new tag shows to the right of the Add Tag field.
In This Section: |
A Network is a group of IP addresses defined by a network address and a net mask. The net mask indicates the size of the network.
A Broadcast IP address is an IP address which is destined for all hosts on the specified network. If this address is included, the Broadcast IP address will be considered as part of the network.
A network group is a collection of hosts, gateways, networks or other groups.
Groups are used where you cannot work with single objects, e.g. when working with VPN domains or with topology definitions.
Groups facilitate and simplify network management. Modifications are applied to the group instead of each member of the group.
To create a group of network objects:
The New Network Group window opens.
A Check Point Host can have multiple interfaces but no routing takes place. It is an endpoint that receives traffic for itself through its interfaces. (In comparison, a Security Gateway routes traffic between its multiple interfaces.) For example, if you have two unconnected networks that share a common Security Management Server and Log Server, configure the common server as a Check Point Host object.
A Check Point Host has one or more Software Blades installed. But if the Firewall blade is installed on the Check Point Host, it cannot function as a firewall. The Host requires SIC and other features provided by the actual firewall.
A Check Point Host has no routing mechanism, is not capable of IP forwarding, and cannot be used to implement Anti-spoofing. If the host must do any of these, convert it to be a Security Gateway.
The Security Management Server object is a Check Point Host.
Note - When you upgrade to R80.20 from R77.30 or earlier versions, Node objects are converted to Host objects.
A gateway cluster is a group of Security Gateways with Cluster software installed: ClusterXL, or another Clustering solution. Clustered gateways add redundancy through High Availability or Load Sharing.
An updatable object is a network object which represents an external service, such as Office 365, AWS, GEO locations and more. External services providers publish lists of IP addresses or Domains or both to allow access to their services. These lists are dynamically updated. Updatable objects derive their contents from these published lists of the providers, which Check Point uploads to the Check Point cloud. The updatable objects are updated automatically on the Security Gateway each time the provider changes a list. There is no need to install policy for the updates to take effect. You can use an updatable object in the Access Control policy as a source or a destination.
Note - This feature is only supported for R80.20 and above gateways.
A customer uses Office365 and wants to allow access to Microsoft Exchange services.
To add the Microsoft Exchange Updatable Object to the Security Gateway:
The Updatable Objects window opens.
Note - You can also add objects to the Source column.
The Exchange Services object is added to the Rule Base.
No |
Name |
Source |
Destination |
VPN |
Services & Applications |
Action |
Track |
1 |
Accept Exchange |
WirelessZone |
Exchange Services |
Any |
Any |
Accept |
Log |
2 |
Accept Exchange |
Exchange Services |
WirelessZone |
Any |
Any |
Accept |
Log |
You can monitor the updates in the Logs & Monitor Logs view.
To monitor the updates:
The Log Details window shows.
Succeeded shows in the Status field when the update is successful.An address range is a range of IP addresses on the network, defined by the lowest and the highest IP addresses. Use an Address Range object when you cannot define a range of IP addresses by a network IP and a net mask. The Address Range objects are also necessary for the implementation of NAT and VPN.
Wildcard objects let you define IP address objects that share a common pattern that can be permitted or denied access in a security policy.
Note - This feature is only supported for R80.20 and above gateways.
To create a new wildcard object:
The wildcard object contains a wildcard IP address and a wildcard netmask.
The wildcard netmask is the mask of bits that indicate which parts of the IP address must match and which do not have to match. For example:
Wildcard IP: |
194. |
29. |
0. |
1 |
Wildcard Netmask: |
0. |
0. |
3. |
0 |
The third octet represents the mask of bits. If we convert the 3 to binary, we get 00000011. The 0 parts of the mask must match the equivalent bits of the IP address. The 1 parts of the mask do not have to match, and can be any value.
0 |
0 |
0 |
0 |
0 |
0 |
1 |
1 |
Must match the equivalent bits in the IP address |
Do not have to match |
||||||
The binary netmask produces these possible decimal values:
128 |
64 |
32 |
16 |
8 |
4 |
2 |
1 |
|
|
|
|
|
|
|
|
Binary
|
|
Decimal |
|
0 |
0 |
0 |
0 |
0 |
0 |
0 |
0 |
|
0 |
0 |
0 |
0 |
0 |
0 |
0 |
0 |
1 |
|
1 |
0 |
0 |
0 |
0 |
0 |
0 |
1 |
0 |
|
2 |
0 |
0 |
0 |
0 |
0 |
0 |
1 |
1 |
|
3 |
The netmask permits only these IP addresses:
Scenario One
A supermarket chain has all of its cash registers on subnet 194.29.x.1, where x defines the region. In this use case, all the cash registers in this region must have access to the database server at 194.30.1.1.
Instead of defining 256 hosts (194.29.0.1, 194.29.1.1, 194.29.2.1....194.29.255.1), the administrator creates a wildcard object that represents all the cash registers in the region:
Wildcard IP: |
194. |
29. |
0. |
1 |
Wildcard Mask: |
0. |
0. |
255. |
0 |
The wildcard object can now be added to the access control policy.
Source |
Destination |
Action |
Track |
|---|---|---|---|
Wildcard Object |
Database server object |
Accept |
Log |
Scenario Two
In this use case, a supermarket chain has stores in Europe and Asia.
The 192.30.0-255.1 network contains both the Asian and European regions, and the stores within those regions.
Item |
Description |
|---|---|
1 |
Database Server for Europe |
2 |
Database Server for Asia |
3 |
European and Asia network |
The administrator wants stores in the European and Asia regions to access different database servers. In this topology, the third octet of the European and Asia network's IP address will be subject to a wildcard. The first four bits of the wildcard will represent the region and the last four bits will represent the store number.
Bits that represent the region |
Bits that represent the store number |
0000 |
0000 |
In the Wildcard IP:
In binary:
Binary |
Decimal |
|
Region |
Store |
|
0001 |
0000 |
16 - Asia Region |
0010 |
0000 |
32 - European Region |
To include all the stores of a particular region, the last four bits of the wildcard mask must be set to 1 (15 in Decimal):
Binary |
Decimal |
|
Region |
Store |
|
xxxx |
1111 |
15 - all Asian stores |
xxxx |
1111 |
15 - all European stores |
A wildcard object that represents all the Asian stores will look like this:
Wildcard IP address |
192.30.16.1 |
(The region) |
Wildcard netmask |
0.0.15.0 |
(for stores in the region) |
For this range of IP addresses: 192.30.16-31.1
A wildcard object that represents all the European stores will look like this:
Wildcard IP address |
192.30.32.1 |
(the region) |
Wildcard netmask |
0.0.15.0 |
(for stores in the region) |
For this range of IP addresses: 192.30.32-47.1
The administrator can now use these wildcard objects in the access control policy:
Source |
Destination |
Action |
Track |
|---|---|---|---|
Asian Stores Wildcard |
Database Server for Asia |
Accept |
Log |
European Stores Wildcard |
Database Server for Europe |
Accept |
Log |
Scenario Three
In this scenario, the netmask bits are not consecutive.
Wildcard IP |
1 |
1 |
0 |
1 |
Wildcard mask |
0 |
0 |
5 |
0 |
Wildcard IP |
00000001.00000001.00000000.00000001 |
Wildcard Mask |
00000000.00000000.00000101.00000000 |
Mask:
00 |
01 |
02 |
03 |
04 |
05 |
06 |
07 |
08 |
09 |
10 |
11 |
12 |
13 |
14 |
15 |
16 |
17 |
18 |
19 |
20 |
21 |
22 |
23 |
24 |
25 |
26 |
27 |
28 |
29 |
30 |
31 |
0 |
0 |
0 |
0 |
0 |
0 |
0 |
0 |
0 |
0 |
0 |
0 |
0 |
0 |
0 |
0 |
0 |
0 |
0 |
0 |
0 |
1 |
0 |
1 |
0 |
0 |
0 |
0 |
0 |
0 |
0 |
0 |
Which will match only these IP addresses:
IP Address |
Binary |
Comment |
|---|---|---|
1.1.0.1 |
00000001.00000001.00000000.00000001 |
The IP address itself |
1.1.1.1 |
00000001.00000001.00000001.00000001 |
The equivalent bit at position 23 does not matter |
1.1.4.1 |
00000001.00000001.00000100.00000001 |
The equivalent bit at position 21 does not matter |
1.1.5.1 |
00000001.00000001.00000101.00000001 |
The equivalent bits at positions 21 and 23 do not matter |
The same principles apply to IPv6 addresses. For example, if the wildcard object has these values:
IPv6 Address |
2001::1:10:0:1:41 |
Wildcard netmask |
0::ff:0:0 |
The wildcard will match: 2001::1:10:0-255:1:41
A Domain object lets you define a host or DNS domain by its name only. It is not necessary to have the IP address of the site.
You can use the Domain object in the source and destination columns of an Access Control Policy.
You can configure a Domain object in two ways:
In the object name, use the Fully Qualified Domain Name (FQDN). Use the format .x.y.z (with a dot "." before the FQDN). For example, if you use .www.example.com then the Gateway matches www.example.com
This option is supported for R80.10 and higher, and is the default. It is more accurate and faster than the non-FQDN option.
The Security Gateway looks up the FQDN with a direct DNS query, and uses the result in the Rule Base.
This option supports SecureXL Accept templates. Using domain objects with this option in a rule has no effect on the performance of the rule, or of the rules that come after it.
This option enforces the domain and its sub-domains. In the object name, use the format .x.y for the name. For example, use .example.com or .example.co.uk for the name. If you use .example.com, then the Gateway matches www.example.com and support.example.com
The Gateway does the name resolution using DNS reverse lookups, which can be inaccurate. The Gateway uses the result in the Rule Base, and caches the result to use again.
When upgrading from R77, this option is enforced.
A dynamic object is a "logical" object where the IP address is resolved differently for each Security Gateway, using the dynamic_objects command.
For R80.10 Security Gateways and higher, dynamic objects support SecureXL Accept templates. Therefore, there is no performance impact on a rule that uses a dynamic object, or on rules that come after it.
Dynamic Objects are predefined for LocalMachine-all-interfaces. The DAIP computer interfaces (static and dynamic) are resolved into this object.
Security Zones let you to create a strong Access Control Policy that controls the traffic between parts of the network.
A Security Zone object represents a part of the network (for example, the internal network or the external network). You assign a network interface of a Security Gateway to a Security Zone. You can then use the Security Zone objects in the Source and Destination columns of the Rule Base.
Use Security Zones to:
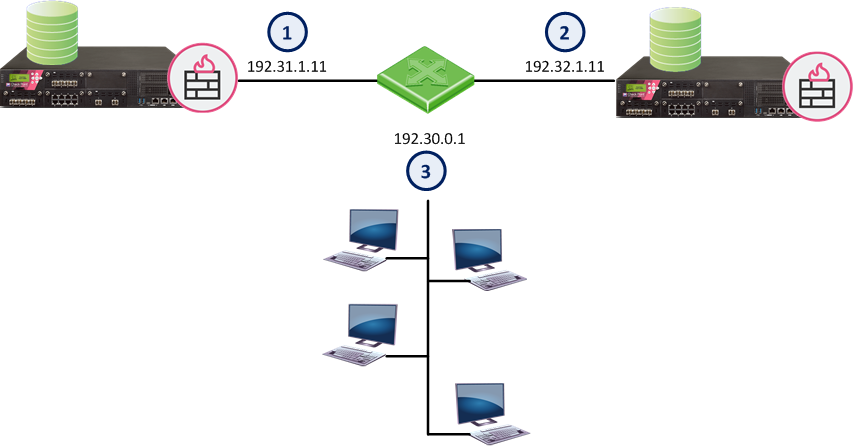
For example, in the diagram, we have three Security Zones for a typical network: ExternalZone (1), DMZZone (2) and InternalZone (3).
A Security Gateway interface can belong to only one Security Zone. Interfaces to different networks can be in the same Security Zone.
Workflow
Source |
Destination |
VPN |
Service |
Action |
|
|---|---|---|---|---|---|
InternalZone |
ExternalZone |
Any Traffic |
Any |
Accept |
|
Before you can use Security Zones in the Rule Base, you must assign Gateway interfaces to Security Zones.
To create a Security Zone:
The Security Zone window opens.
To assign an interface to a Security Zone
The Gateway Properties window opens.
The Interface window opens. The Topology area of the General pane shows the Security Zone to which the interface is already bound. By default, the Security Zone is calculated according to where the interface Leads To.
The Topology Settings window opens.
Or click New to create a new one.
These are the predefined security zones, and their intended purposes:
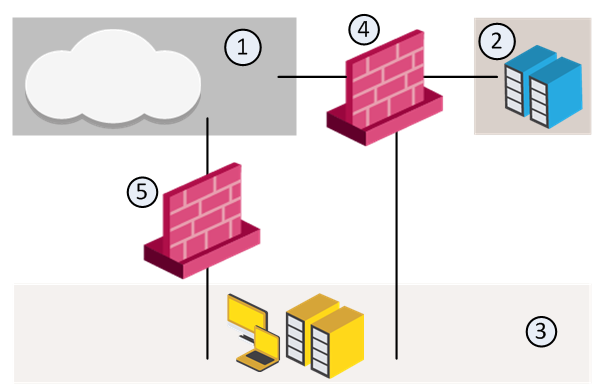
A DMZ lets external users and applications access specific internal servers, but prevents the external users accessing secure company networks. Add rules to the firewall Rule Base that allow traffic to the company DMZ. For example, a rule that allows HTTP and HTTPs traffic to your web server in the DMZ.
An Externally Managed Security Gateway or a Host is a gateway or a Host which has Check Point software installed on it. This Externally Managed gateway is managed by an external Security Management Server. While it does not receive the Check Point Security Policy, it can participate in Check Point VPN communities and solutions.
An Interoperable Device is a device that has no Check Point Software Blades installed. The Interoperable Device:
There are five types of VoIP Domain objects:
In many VoIP networks, the control signals follow a different route through the network than the media. This is the case when the call is managed by a signal routing device. Signal routing is done in SIP by the Redirect Server, Registrar, and/or Proxy. In SIP, signal routing is done by the Gatekeeper and/or gateway.
Enforcing signal routing locations is an important aspect of VoIP security. It is possible to specify the endpoints that the signal routing device is allowed to manage. This set of locations is called a VoIP Domain. For more information refer to the R80.20 VoIP Administration Guide.
A Logical Server is a group of machines that provides the same services. The workload of this group is distributed between all its members.
When a Server group is stipulated in the Servers group field, the client is bound to this physical server. In Persistent server mode the client and the physical server are bound for the duration of the session.
The load balancing algorithm stipulates how the traffic is balanced between the servers. There are several types of balancing methods:
The Open Security Extension features let you manage third-party devices with the Check Point SmartConsole. The number of managed devices, both hardware and software packets, depends on your license. OSE devices commonly include hardware security devices for routing or dedicated Network Address Translation and Authentication appliances. Security devices are managed in the Security Policy as Embedded Devices.
The Security Management Server generates Access Lists from the Security Policy and downloads them to selected routers and open security device. Check Point supports these devices:
OSE Device |
Supported Versions |
|---|---|
Cisco Systems |
9.x, 10.x, 11.x, 12.x |
The Check Point Rule Base must not have these objects. If it does, the Security Management Server will not generate Access Lists.
OSE devices report their network interfaces and setup at boot time. Each OSE device has a different command to list its configuration. You must define at least one interface for each device, or Install Policy will fail.
To define an OSE Device:
We recommend that you also add the OSE device to the host lists on other servers: hosts (Linus) and lmhosts (Windows).
You can enable Anti-Spoofing on the external interfaces of the device. Double-click the interface. In the Interface Properties window > Topology tab, select External and Perform Anti-Spoofing.
For Cisco (Version 10.x and higher) devices, you must specify the direction of the filter rules generated from anti-spoofing parameters. The direction of enforcement is specified in the Setup tab of each router.
For Cisco routers, the direction of enforcement is defined by the Spoof Rules Interface Direction property.
Access List No — The number of Cisco access lists enforced. Cisco routers Version 12x and below support an ACL number range from 101-200. Cisco routers Version 12x and above support an ACL range number from 101-200 and also an ACL number range from 2000-2699. Inputting this ACL number range enables the support of more interfaces.
For each credential, select an option:
Username — The name required to logon to the OSE device.
Password — The Administrator password (Read only) as defined on the router.
Enable Username — The user name required to install Access Lists.
Enable Password — The password required to install Access Lists.
Version — The Cisco OSE device version (9.x, 10.x, 11.x, 12.x).
OSE Device Interface Direction — Installed rules are enforced on data packets traveling in this direction on all interfaces.
Spoof Rules Interface Direction — The spoof tracking rules are enforced on data packets traveling in this direction on all interfaces.