


In This Section: |
The IPsec VPN solution lets the Security Gateway encrypt and decrypt traffic to and from other gateways and clients. Use SmartConsole to easily configure VPN connections between Security Gateways and remote devices.
For Site-to-Site Communities, you can configure Star and Mesh topologies for VPN networks, and include third-party gateways.
The VPN tunnel guarantees:
IKE and IPsec
The Check Point VPN solution uses these secure VPN protocols to manage encryption keys, and send encrypted packets. IKE (Internet Key Exchange) is a standard key management protocol that is used to create the VPN tunnels. IPsec is protocol that supports secure IP communications that are authenticated and encrypted on private or public networks.
If employees remotely access sensitive information from different locations and devices, system administrators must make sure that this access does not become a security vulnerability. Check Point's Remote Access VPN solutions let you create a VPN tunnel between a remote user and the internal network. The Mobile Access Software Blade extends the functionality of Remote Access solutions to include many clients and deployments.
When securely connecting remote clients with the internal resources, organizations face connectivity challenges, such as these:
The Check Point IPsec VPN Software Blade provides these VPN connectivity modes to help organizations resolve those challenges:
Remote users can be assigned the same or non-routable IP addresses from the local ISP. Office Mode solves these routing problems and encapsulates the IP packets with an available IP address from the internal network. Remote users can send traffic as if they are in the office and avoid VPN routing problems.
Remote users can be restricted to using only HTTP and HTTPS protocols. Visitor Mode lets these users tunnel all protocols through regular TCP connections on port 443.
Here is an example of a Remote Access VPN workflow:
Optional - Configure the gateway for remote user authentication (optional).
|
|
Enable remote access VPN |
|
|
|
|
|
|
|
Configure LDAP |
LDAP
|
Manage Users? |
R80 Smart |
Configure users |
|
|
|
|
|
Configure user authentication |
|
|
|
Configure user authentication |
|
|
|
|
|
Create LDAP user |
|
Create VPN Community |
|
Create user |
|
|
|
|
|
|
|
Configure rules for VPN access in Access Control Rule Base |
|
|
|
|
|
|
|
|
|
Install policy |
|
|
VPN is composed of:
Term |
Description |
|---|---|
VPN |
Virtual Private Network. A secure, encrypted connection between networks and remote clients on a public infrastructure. A VPN gives authenticated remote users and sites secured access to an organization's network and resources. |
VPN Doman |
A group of computers and networks connected to a VPN tunnel by one VPN gateway that handles encryption and protects the VPN Domain members. |
VPN Community |
A named collection of VPN domains, each protected by a VPN gateway. |
VPN Security Gateway |
The gateway that manages encryption and decryption of traffic between members of a VPN Domain, typically located at one (Remote Access VPN) or both (Site to Site VPN) ends of a VPN tunnel. |
Site-to-Site VPN |
An encrypted tunnel between two gateways, typically of different geographical sites. |
Remote Access VPN |
An encryption tunnel between a Security Gateway and remote access clients, such as Endpoint Security VPN, and communities. |
Remote Access Community |
A group of computers, appliances, and devices that access with authentication and encryption, the internal protected network from physically remote sites. |
IKE |
Internet Key Exchange. An encryption key management protocol that enhances IPSec by providing additional features, flexibility, and ease of configuration. |
IPSec |
A set of secure VPN protocols that manage encryption keys and encrypted packet traffic, to create a standard for authentication and encryption services. |
A VPN tunnel establishment process is initiated to allow the user to access a network resource protected by a Security Gateway. An IKE negotiation takes place between the peers.
During IKE negotiation, the peers' identities are authenticated. The Security Gateway verifies the user's identity and the client verifies that of the Security Gateway. The authentication can be performed using several methods, including digital certificates issued by the Internal Certificate Authority (ICA). It is also possible to authenticate using third-party PKI solutions and pre-shared secrets.
After the IKE negotiation ends successfully, a secure connection (a VPN tunnel) is established between the client and the Security Gateway. All connections between the client and the Security Gateway VPN domain (the LAN behind the Security Gateway) are encrypted inside this VPN tunnel, using the IPsec standard. Except for when the user is asked to authenticate in some manner, the VPN establishment process is transparent.
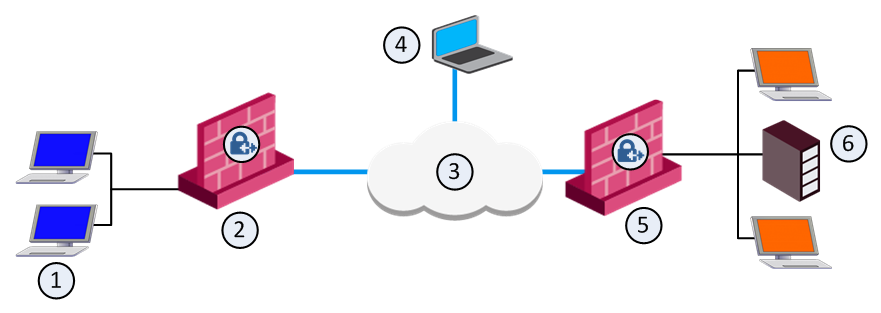
Item |
Description |
|---|---|
1 |
Host1. Part of VPN Site 1. |
2 |
Gateway 1. Part of VPN Site 1. |
3 |
Internet |
4 |
Remote Client |
5 |
Gateway 2. Part of VPN Site 2. |
6 |
LDAP Server. Part of VPN Site 2. |
In the figure, the remote user initiates a connection to Security Gateway 1. User management is not performed via the VPN database, but by LDAP server belonging to VPN Site 2. Authentication takes place during the IKE negotiation. Security Gateway 1 verifies that the user exists by querying the LDAP server behind Security Gateway 2. After the user's existence is verified, the Security Gateway authenticates the user, for example by validating the user's certificate. After IKE is successfully completed, a tunnel is created and the remote client connects to Host 1.
If the client is behind the Security Gateway (for example, if the user accesses the corporate LAN from a company office), connections from the client to destinations that are also behind the LAN Security Gateway are not encrypted.