Check Point VPN
IPsec VPN
The IPsec VPN solution lets the Security Gateway encrypt and decrypt traffic to and from other gateways and clients. Use SmartConsole to easily configure VPN connections between Security Gateways and remote devices.
For Site to Site Communities, you can configure Star and Mesh topologies for VPN networks, and include third-party gateways.
The VPN tunnel guarantees:
- Authenticity - Uses standard authentication methods
- Privacy - All VPN data is encrypted
- Integrity - Uses industry-standard integrity assurance methods
IKE and IPsec
The Check Point VPN solution uses these secure VPN protocols to manage encryption keys, and send encrypted packets. IKE (Internet Key Exchange) is a standard key management protocol that is used to create the VPN tunnels. IPsec is protocol that supports secure IP communications that are authenticated and encrypted on private or public networks.
VPN Components
VPN is composed of:
- VPN endpoints, such as Security Gateways, Security Gateway clusters, or remote clients (such as laptop computers or mobile phones) that communicate using a VPN.
- VPN trust entities, such as a Check Point Internal Certificate Authority (ICA). The ICA is part of the Check Point suite used for creating SIC trusted connection between Security Gateways, authenticating administrators and third party servers. The ICA provides certificates for internal Security Gateways and remote access clients which negotiate the VPN link.
- VPN Management tools, such as Security Management Server and SmartConsole. SmartConsole is the SmartConsole used to access the Security Management Server. The VPN Manager is part of SmartConsole. SmartConsole enables organizations to define and deploy Intranet, and remote Access VPNs.
Understanding the Terminology
- VPN - Virtual Private Network. A secure, encrypted connection between networks and remote clients on a public infrastructure, to give authenticated remote users and sites secured access to an organization's network and resources.
- Virtual Tunnel Interface - Virtual Tunnel Interface. A virtual interface that is a member of an existing, Route Based, VPN tunnel.
- VPN Peer - A gateway that connects to a different gateway using a Virtual Tunnel Interface.
- VPN Domain - A group of computers and networks connected to a VPN tunnel by one VPN gateway that handles encryption and protects the VPN Domain members.
- VPN Community - A named collection of VPN domains, each protected by a VPN gateway.
- VPN Security Gateway - The gateway that manages encryption and decryption of traffic between members of a VPN Domain, typically located at one (Remote Access VPN) or both (Site to Site VPN) ends of a VPN tunnel.
- Site to Site VPN - An encrypted tunnel between two gateways, typically of different geographical sites.
- Remote Access VPN - An encryption tunnel between a Security Gateway and remote access clients, such as Endpoint Security VPN, and communities.
- Remote Access Community - A group of computers, appliances, and devices that access, with authentication and encryption, the internal protected network from physically remote sites.
- Star Topology - A "hub and spoke" virtual private network community, with gateways defined as Satellites (spokes) that create tunnels only with the central gateway ("hub").
- Meshed topology - A VPN community with a VPN Domain that creates a tunnel to other VPN Domains.
- Domain-based VPN - A method to route encrypted traffic with parameters defined by Security Gateways.
- Route-Based VPN - A routing method for participants in a VPN community, defined by the Virtual Tunnel Interfaces (VTI).
- IKE (Internet Key Exchange) - An Encryption key management protocol that enhances IPSec by providing additional features, flexibility, and ease of configuration.
- IPSec - A set of secure VPN protocols that manage encryption keys and encrypted packet traffic, to create a standard for authentication and encryption services.
Site-to-Site VPN
The basis of Site-to-Site VPN is the encrypted VPN tunnel. Two Security Gateways negotiate a link and create a VPN tunnel and each tunnel can contain more than one VPN connection. One Security Gateway can maintain more than one VPN tunnel at the same time.
Sample Site-to-Site VPN Deployment
Item
|
Description
|
A, B
|
Security Gateways
|
2
|
VPN tunnel
|
3
|
Internal network in VPN domain
|
4
|
Host 4
|
5
|
Host 5
|
In this sample VPN deployment, Host 4 and Host 5 securely send data to each other. The Security Gateways do IKE negotiation and create a VPN tunnel. They use the IPsec protocol to encrypt and decrypt data that is sent between Host 4 and Host 5.
VPN Workflow
Host 4 sends packet
to Host 5
|

|
Firewalls A & B create VPN tunnel
|

|
Firewall A encrypts data
|
|
|
|
|

|
Host 5 receives unencrypted data
|

|
Firewall B decrypts data
|

|
Encrypted data is sent through VPN tunnel
|
VPN Communities
A VPN Domain is a collection of internal networks that use Security Gateways to send and receive VPN traffic. Define the resources that are included in the VPN Domain for each Security Gateway. Then join the Security Gateways into a VPN community - collection of VPN tunnels and their attributes. Network resources of different VPN Domains can securely communicate with each other through VPN tunnels that terminate at the Security Gateways in the VPN communities.
VPN communities are based on Star and Mesh topologies. In a Mesh community, there are VPN tunnels between each pair of Security Gateway. In a Star community, each satellite Security Gateway has a VPN tunnel to the central Security Gateway, but not to other Security Gateways in the community.
Note - Global VPN Communities are not supported in this release.
Item
|
Description
|
1
|
Security Gateway
|
2
|
Satellite Security Gateways
|
3
|
Central Security Gateway
|
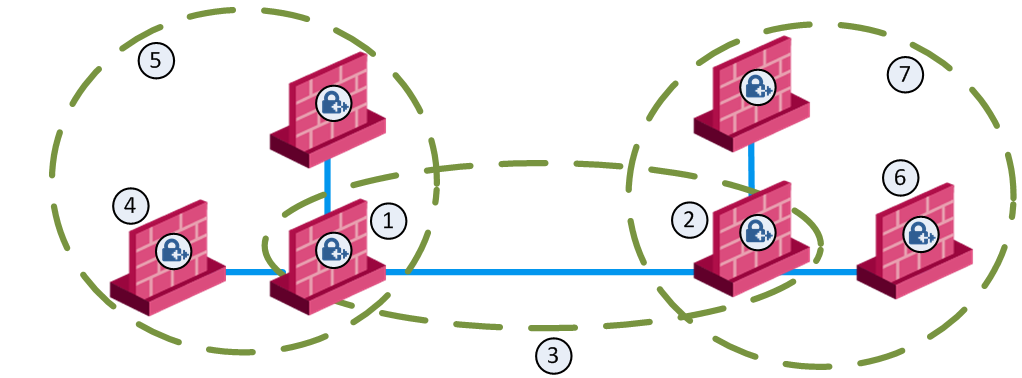
Sample Combination VPN Community
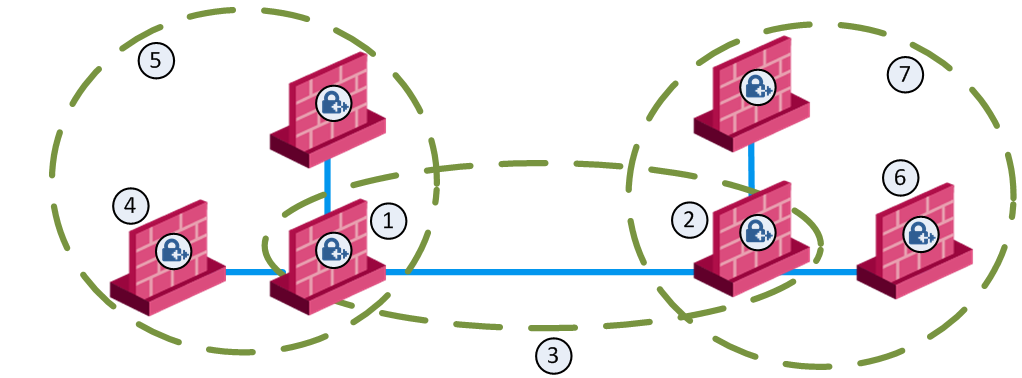
Item
|
Description
|
1
|
London Security Gateway
|
2
|
New York Security Gateway
|
3
|
London - New York Mesh community
|
4
|
London company partner (external network)
|
5
|
London Star community
|
6
|
New York company partner (external network)
|
7
|
New York Star community
|
This deployment is composed of a Mesh community for London and New York Security Gateways that share internal networks. The Security Gateways for external networks of company partners do not have access to the London and New York internal networks. However, the Star VPN communities let the company partners access the internal networks of the sites that they work with.
Routing VPN Traffic
Configure the Security Gateway to route VPN traffic based on VPN Domains or based on the routing settings of the operating system.
Note - For each VPN gateway, you must configure an existing gateway as a default gateway.
Domain Based VPN
The VPN traffic is routed according to the VPN Domains that are defined in SmartConsole. Use domain based routing to let satellite Security Gateways in a star-based topology send VPN traffic to each other. The central Security Gateway creates a VPN tunnel to each satellite gateway and the traffic is routed to the correct VPN domain.
Route Based VPN
VPN traffic is routed according to the routing settings (static or dynamic) of the Security Gateway operating system. The Security Gateway uses a VTI (VPN Tunnel Interface) to send the VPN traffic as if it were a physical interface. The VTIs of Security Gateways in a VPN community connect and can support dynamic routing protocols.
Granular Routing Control
The Link Selection feature gives you granular control of the VPN traffic in the network. Use this feature to enable the Security Gateway to:
- Find the best possible route for VPN traffic
- Select the interfaces that are used for VPN traffic to internal and external networks
- Configure the IP addresses that are used for VPN traffic
- Use route probing to select available VPN tunnels
- Use Load Sharing for Link Selection to equally distribute VPN traffic to VPN tunnels
IPv6 Support and Limitations
This release includes limited IPv6 support for IPsec VPN communities:
- IPv6 is supported for Site to Site VPN only (Main IP to Main IP). The Main IP address for both Security Gateways must be defined as an IPv6 Address. You can define other IP addresses that are IPv4 or IPv6.
- IPv6 supports IKEv2 encryption only. IKEv2 is automatically always used for IPv6 traffic. The encryption method configuration applies to IPv4 traffic only.
- VPN tunneling only supports IPv4 inside an IPv4 tunnel, and IPv6 inside an IPv6 tunnel. IPv4 traffic inside an IPv6 tunnel is not supported.
These VPN features are not supported for IPv6:
- Remote Access VPN
- CRL fetch for the internal Certificate Authority
- Multiple Entry Points (MEP)
- Route-based VPN (VTI)
- Wire Mode VPN
- Gateways with a dynamic IP address.
- Route Injection Mechanism (RIM)
- Traditional mode Firewall Policies
- IKE Denial of Service protection
- IKE Aggressive Mode
- Gateways with Dynamic IP addresses
- Traditional Mode VPN
- Migration from Traditional mode to Simplified mode
- Tunnel Management (permanent tunnels)
- Directional VPN Enforcement
- Link Selection
- GRE Tunnels
- Tunnel View in SmartView Monitor
- VPN Overview page
- vpn_route.conf configuration file