


In This Section: |
Data is more accessible and transferable today than ever before, and the vast majority of data is sensitive at various levels. Some is confidential simply because it is part of an internal organization and was not meant to be available to the public. Some data is sensitive because of corporate requirements, national laws, and international regulations. Often the value of data is dependent upon its remaining confidential - consider intellectual property and competition.
Leakage of your data could be embarrassing or worse, cost you industrial edge or loss of accounts. Allowing your organization to act in non-compliance with privacy acts and other laws could be worse than embarrassing - the integrity of your organization may be at stake.
You want to protect the privacy of your organization, but with all the tools making information sharing easier, it is easier to make an irrecoverable mistake. To make the matter more complex, along with the severity of data leakage, we now have tools which inherently make it easier to happen: cloud servers, Google docs, and simple unintentional abuse of company procedures - such as an employee taking work home. In fact, most cases of data leakage occur because of unintentional leaks.
The best solution to prevent unintentional data leaks is to implement an automated corporate policy that will catch protected data before it leaves your organization. Such a solution is known as Data Loss Prevention (DLP).
Data Loss Prevention identifies, monitors, and protects data transfer through deep content inspection and analysis of transaction parameters (such as source, destination, data object, and protocol), with a centralized management framework. In short, DLP detects and prevents the unauthorized transmission of confidential information.
|
Note - Data Loss Prevention is also known as Data Leak Prevention, Information Leak Detection and Prevention, Information Leak Prevention, Content Monitoring and Filtering, and Extrusion Prevention. |
DLP captures original data that caused a rule match, including the body of the transmission and attached files. We recommend that you disclose to your users how your DLP deployment works. Tell users that transmissions that violate the data security guidelines of your organization will be stored and may be read by security personnel.
Information disclosure recommendations:
DLP incident notifications can be sent by email (for SMTP traffic) or shown in a system tray popup from the UserCheck client (for SMTP, HTTP, FTP, etc).
If the incident of the notification is in Ask User mode, the user can click the Send or Discard link in the popup of UserCheck client: to handle the incident in real-time.
|
Important - Make your users are aware of the purpose of the UserCheck client: handle the DLP options directly from the popup. If the user exits the client, the alternative web page that provides the Ask User options may not function. |
The Check Point Data Loss Prevention Software Blade provides the ability for you to quickly deploy realistic out-of-the-box detection capabilities based on expert heuristics.
However, optimal DLP must take time. To define data that should be prevented from transmission, you must take into account many variables, each changing in the context of the particular transmission: What type of data is it? Who owns it? Who is sending it? Who is the intended receiver? When is it being sent? What is the cost if tasks are disrupted because the policy is stricter than needed?
Data Loss Prevention Features
Check Point solves the complexity of Data Loss Prevention with unique features.
Without UserCheck, a security administrator, or even a security team, would have to check every email and data transfer in real time and approve or reject each. For this reason, other products offer only detection of suspicious incidents. With UserCheck, the decision-making is distributed to the users. They are presented with the reason for the data capture and must provide a reason for letting it pass (if the notification did not change their minds about sending it on). User decisions (send or discard) and reasons for sending are logged. With the original message and user decisions and reasons, you can develop an effective prevention policy based on actual use.
Data Loss Prevention Benefits
Check Point DLP saves time and significantly improves ROI. Its innovative technologies provide automation that negates the need for long and costly analysis and a team for incident handling. You can now move from a detection-only policy to an accurate and effective prevention policy without bringing in outside consultants or hiring a security team.
All of this functionality is easy to manage through the SmartDashboard, in an interface similar to other Software Blades. You are not expected to be a DLP expert from the day of deployment. Check Point Data Loss Prevention guides you on how to customize and improve your DLP policy - with the Improve Accuracy flag, for example. The DLP Software Blade comes with a large number of built-in Data Types that can be quickly applied as a default policy. You can fine-tune the out-of-the-box policy to easily convert the confidentiality and integrity guidelines of your organization into automated rules. And later, you can create your own Data Types. This cycle of updating the policy, moving from a detection policy to a preventative policy, is close with strong monitoring tools - Check Point SmartEvent.
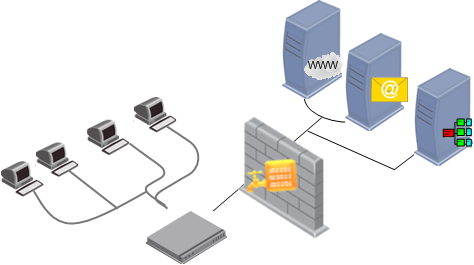
It catches all traffic containing data and being sent through supported protocols. Thus, when users send data that goes to an HTTP proxy (4) or a mail server (5), for example, the DLP gateway catches the data before it leaves the organization.
It scans the traffic, including email attachments, for data that should be protected from being sent outside the organization. This data is recognized by protocol, source, destination, and complex Data Type representations.
It can also scan internal traffic between Microsoft Exchange clients within the organization. This requires installation of the Exchange Security Agent on the Microsoft Exchange server. The agent forwards internal emails to the DLP gateway which then scans them. If the organization only uses Exchange servers for managing emails (internal and external), you can use this setup to also scan emails that are sent outside of the organization.
If the data does not match any of the rules of the DLP policy, the traffic is allowed to pass.
In an Integrated DLP Security Gateway deployment, the Data Loss Prevention Software Blade is enabled on a Security Gateway (or a ClusterXL Security Cluster). This makes it the DLP gateway (or DLP Security Cluster). The firewall Software Blade, and optionally, other Network Security Software Blades, are also enabled on the gateway.
If the DLP gateway is on the perimeter, the SMTP server forwards only transmissions with destinations outside of the organization to DLP. Internal and external transmissions can be inspected by DLP if they are forwarded to DLP by the Exchange Security Agent on the Exchange Server. For external transmissions through the Exchange Security Agent the Exchange Server must have an accessible IP address to the DLP gateway.
This deployment is supported on one of these:
In a Dedicated DLP gateway, the Data Loss Prevention Software Blade is enabled on a gateway (1) (or a ClusterXL Security Cluster). This makes it a DLP gateway (or DLP Security Cluster). No other Network Security Software Blade, is enabled. For example, the firewall Software Blade is not enabled on the gateway, so the gateway does not enforce the Security Policy. The DLP gateway can sit behind a protecting Security Gateway (2).
When setting up a dedicated DLP gateway (1), Check Point recommends that you configure the DLP gateway as a bridge. The bridge is transparent to network routing.
A dedicated DLP gateway deployment is supported on:
As an alternative to putting the DLP gateway on the network perimeter, you can put the DLP gateway between the user networks and the servers, to allow DLP to inspect traffic before it goes to the servers. This deployment is the necessary configuration if you want to use a DLP rule that inspects data transmissions between departments.
For example, you can create a DLP rule that checks emails between internal groups: Source is a specific network, Destination is Outside Source (anything outside of this Source). Such a rule would be applied only if this deployment was used.
You can put the DLP gateway between the users and the switch, to directly protect a subnet.

The DLP gateway captures traffic and scans it against the Data Loss Prevention policy. If the data in the traffic matches a rule in the policy:
DLP provides various auditing tools: automatic notifications to data owners when transmission of protected data has been attempted; user notifications and self-handling portal; tracking and logging with SmartView Tracker; event details, charts, graphs, filtered lists from SmartEvent; and reports from SmartReporter.
Before you begin auditing, configure your DLP policy. First, define Data Types.
To create and refine the DLP policy:
Become familiar with the wide range of provided Data Types. Enable and disable the rules in the DLP policy that suit your needs.
Enforce confidentiality guidelines of your organization. Ensure that information belonging to Data Owners stays within their control. Enforce data protection by using your Data Types in DLP rules.
The DLP gateway catches attempted transmissions of protected data and logs incidents in SmartView Tracker. You will decide, with the Data Owners, what incidents also require notification to the Data Owners. As you monitor the incidents, create guidelines to fine tune the DLP policy.
When an email or FTP upload is held because it matches a rule in the Data Loss Prevention policy, it disrupts users. Sometimes this is the best preventative action, but in other situations it is unnecessary. Monitor user actions to see whether users agree that the data should not have been sent or that users have reasons for the transmissions.
Generate Data Owner reports and audit user actions. Look at the logs that SmartView Tracker provides and make sure the DLP policy works smoothly and prevents transmission of protected data.
You can assign a DLP administrator full DLP permissions or a subset of permissions.
With full permissions, a DLP administrator can:
An alternative to assigning a full set of permissions is to configure a subset. This gives you the flexibility to assign only some of the permissions. For example, permissions to only see the fields of the logs but not to see the captured data or send/discard quarantined emails.
To configure full permissions:
The Administrator Properties window opens, displaying General Properties.
The Permissions Profile Properties window opens.
To configure a subset of permissions:
The Administrator Properties window opens, displaying General Properties.
The Permissions Profile Properties window opens.
The Administrator Permission Configuration window opens.
Note - If you select both checkboxes, you are giving full DLP permissions.