UniFi USG Firewall
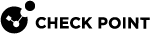
To configure the tunnel in the UniFi USG Management Portal:
-
Log in to the UniFi USG Management Portal with the Administrator account.
-
Click VPN, and then click the Site-to-Site VPN tab.
-
Specify these:
Field
Enter
VPN Type
IPsec
Name Name for the network. Pre-shared key
Secret key specified in Configuring the Tunnel in the Check Point SASE Administrator Portal.
Local IP
Public IP address of the UniFi USG firewall.
Remote IP / Hostname
Check Point SASE gateway IP.
VPN Method Route Based Remote Network(s)
Static
-
Click Add.
-
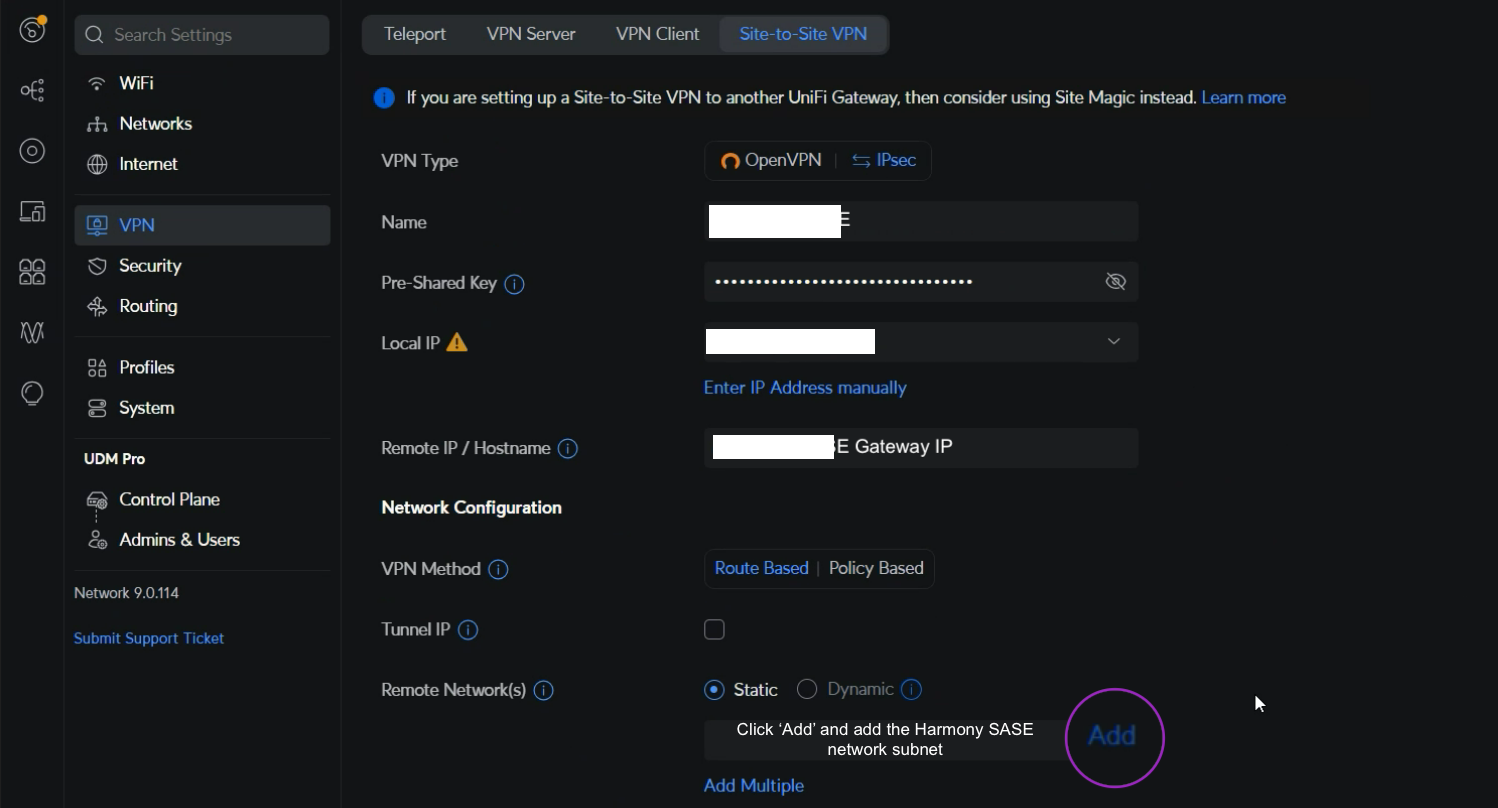
In the Subnet field, click Edit to enter the Check Point SASE network subnet. The default value is
10.255.0.0/16. -
In the Advanced section, select Manual and specify these:
Field
Enter
Key Exchange version IKEv2 IKE
Encryption AES-256 Hash SHA1 DH Group 21 Lifetime
28800
ESP
Encryption AES-256 Hash SHA1 DH Group 21 Lifetime
3600
Perfect Forward Secrecy (PFS)
Enable
Local Authentication ID
Select Auto
Remote Authentication ID
Select Auto
Maximum Transmission Unit
Select Auto
Route Distance
Set a distance
-
Click Add.

To create a Route-Based IPSEC Site-to-Site connection between Check Point SASE and your Ubiquiti network:
-
Set Dynamic Routing to Enable .
-
Add any other subnet specified in Remote Subnets and make sure that a reverse traffic route is created under Static Routes in the UniFi USG firewall for each connected subnet to route through the Check Point SASE Interface.
-
In the Check Point SASEAdministrator Portal, change Check Point SASE Gateway Proposal Subnets and Remote Gateway Proposal Subnets to Any (0.0.0.0/0).
-
Create separate static routing in Check Point SASE.
-
-
Add static routes from Check Point SASE subnet (10.255.0.0/16) to the local network and vice versa through the VPN gateway:
-
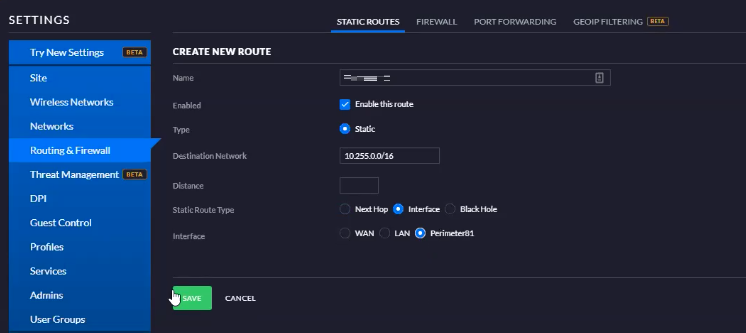
Go to Routing & Firewall > Static Routes > Create New Route.
-
Enter these:
Field
Enter
Name
Name for the static route.
Enabled
Select the Enable this route checkbox.
Type Static Destination Network Check Point SASE subnet. The default is 10.255.0.0/16. Static Route Type Interface Interface Select the interface created in the previous procedure. -
Click Save.
-
-
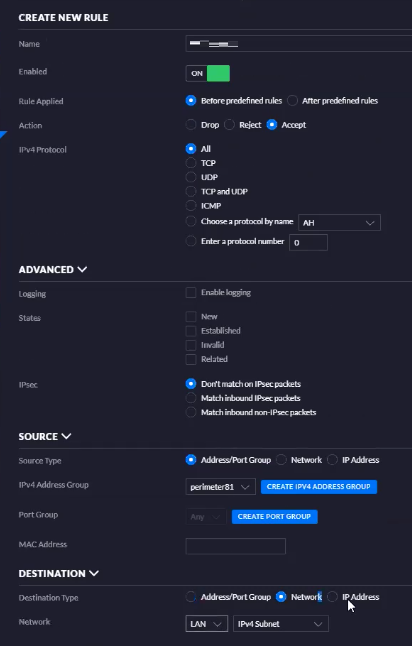
Create a firewall rule to allow traffic from Check Point SASE subnet to the LAN network.
-
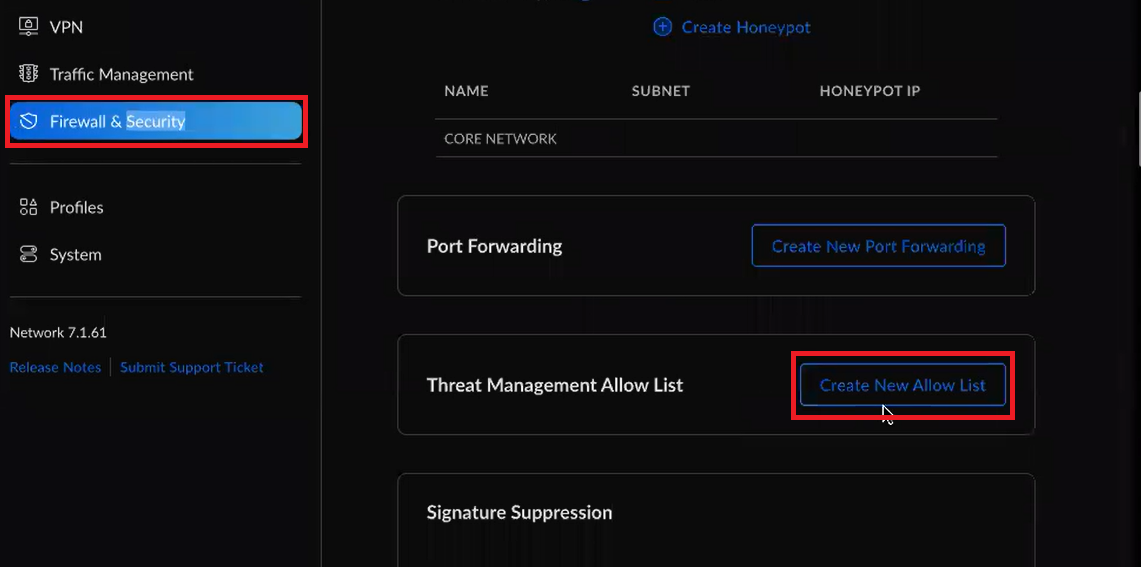
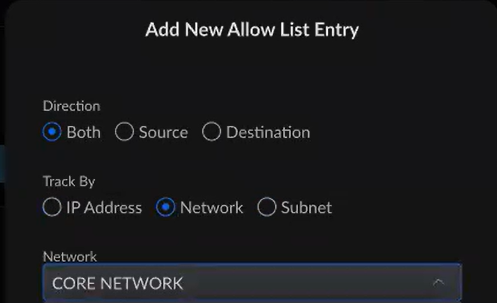
If you have enabled IPS/IDS on the UniFi USG firewall, then to establish a tunnel between the Check Point SASE network and UniFi USG firewall version 7 and later, create an exception in your Threat detection system:
-
Click the Firewall & Security tab.
-
Click Create New Allow List.
-
Select the site-to-site network that you created for this setup.
-
Save your changes.
-