Barracuda Firewall
To configuring the tunnel in the Barracuda Management Portal:
-
Log in to the Barracuda Management Portal with the Administrator account.
-
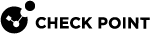
From the top menu, click Configuration > Virtual Servers > Your virtual server > Assigned Services > VPN (VPN-Service) > Site to Site.
-
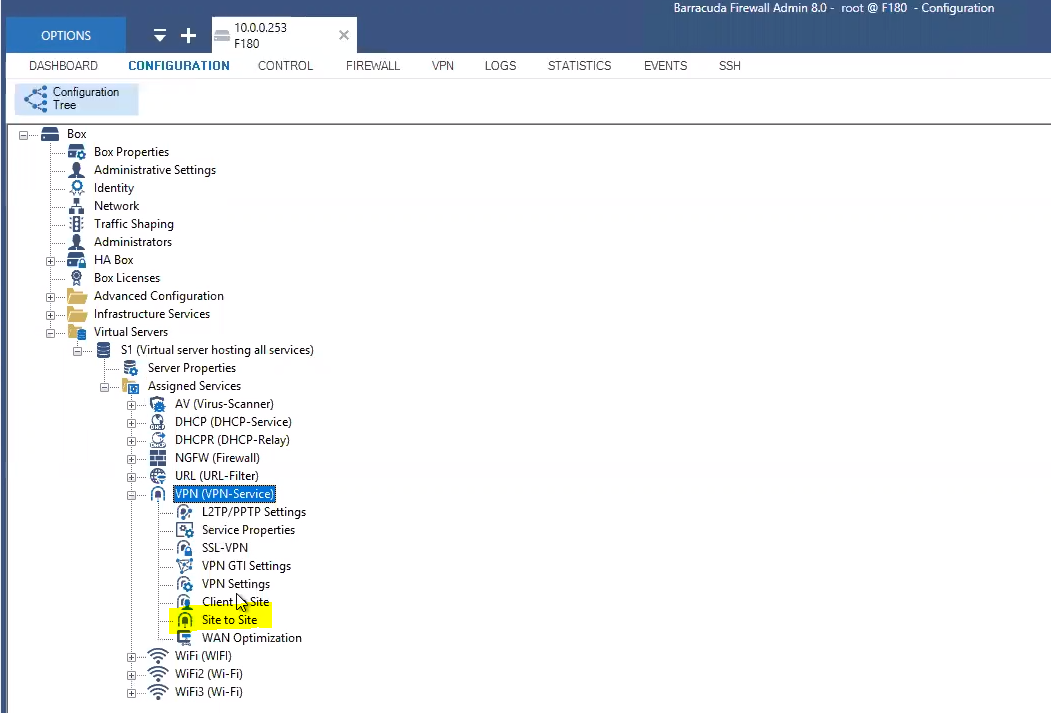
In the IPsec IKEv2 Tunnels tab, create a new tunnel:
-
In the General section:
-
In the Tunnel Name field, enter a tunnel name.
-
Leave the rest of fields to default settings.
-
-
In the Authentication section:
-
From the Authentication Method list, select Pre-shared key.
-
In the Shared Secret field, enter the same secret key that you specified in step 6 in Configuring the Tunnel in the Check Point SASE Administrator Portal.
-
Leave the rest of fields to default settings.
-
-
In the Phase 1 section:
Field
Enter
Encryption AES256 Hash
SHA Diffie-Hellman Group 2 Proposal Handling Strict Lifetime 28800
-
In the Phase 2 section:
Field
Enter
Encryption AES256 Hash
SHA DH-Group 2 Proposal Handling Strict Lifetime 3600
Traffic Volume (KB)
Unlimited
-
-
Click Configuration > Site to Site VPN (vpn):
-
Create a new site-to-site VPN or edit an existing one.
-
In the IPSec IKEv2 Tunnel selection:
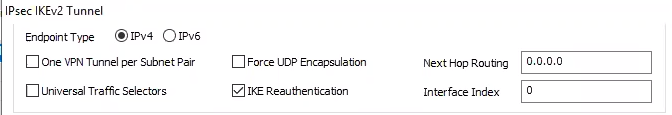
Field
Enter
Endpoint Type IPv4 One VPN Tunnel per Subnet Pair Clear Universal Traffic Selectors Clear Force UDP Encapsulation Clear IKE Reauthentication Select Next Hop Routing 0.0.0.0 Interface Index
0
-
In the Network Local selection:
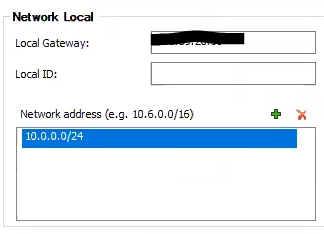
Field
Enter
Local Gateway Barracuda Firewall Public IP address Local ID Barracuda Firewall Public IP address Network address Internal network subnets -
In the Network Remote selection:
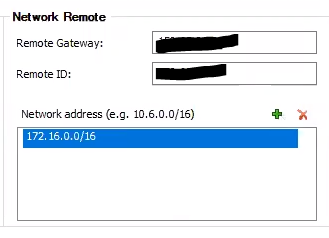
Field
Enter
Remote Gateway Check Point SASE Public IP address Remote ID Check Point SASE Public IP address Network address Check Point SASE network subnets -
In the Dead Peer Detection selection:
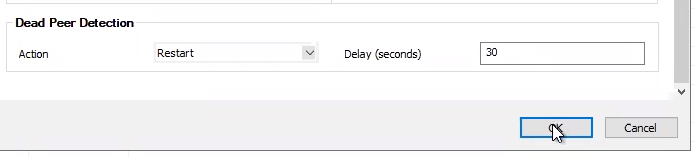
Field
Enter
Action Restart Delay (seconds) 30 -
Click OK.
-
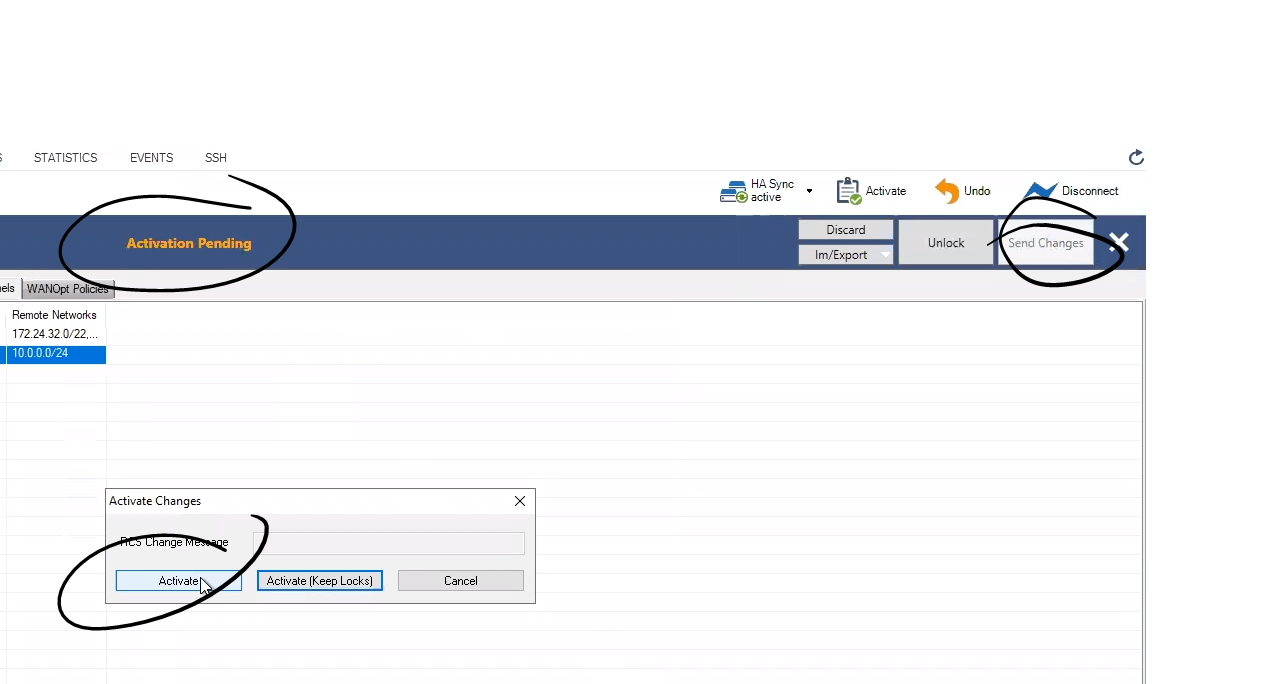
Click Send Changes.
-
Click Activate.
-
-
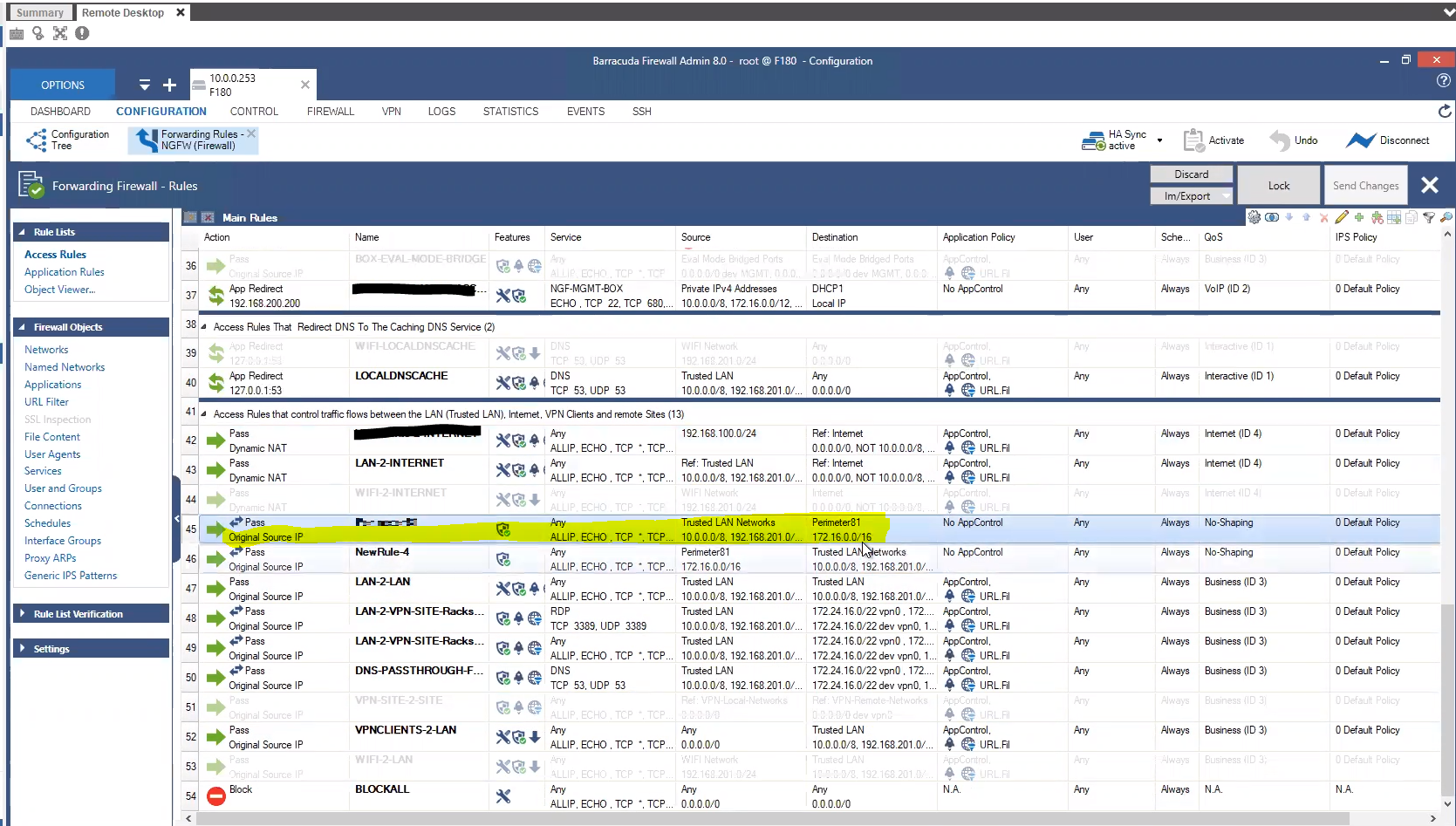
Click Firewall > Forwarding Rules:
-
Add Check Point SASE gateway public IP address to the allow-list.
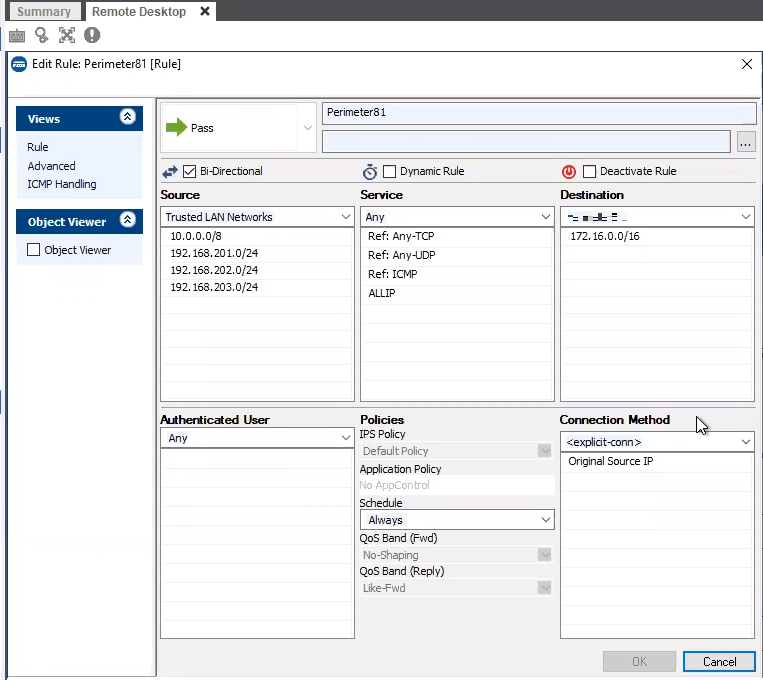
-
Ensure that the Check Point SASE gateway public IP address is listed under the firewall rules.
-
Add the static routes from the Check Point SASE subnet (10.XXX.0.0/16) to the local network and from the local network to the Check Point SASE subnet (10.XXX.0.0/16) through the VPN tunnel gateway.
-
-
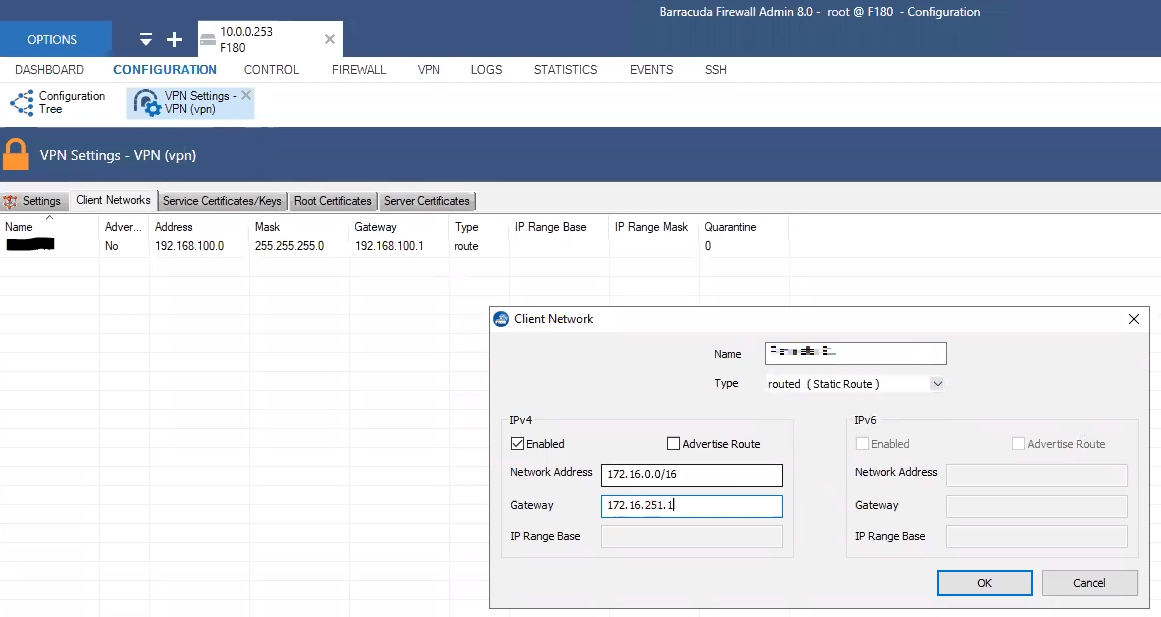
Click Configuration > Site to Site VPN (vpn):
-
In the Client Networks tab:
Field
Enter
Network Address 172.xxx.0.0/16 (or relevant subnet0 Gateway Local Barracuda IP address Name Tunnel name. -
Click OK.
-
-
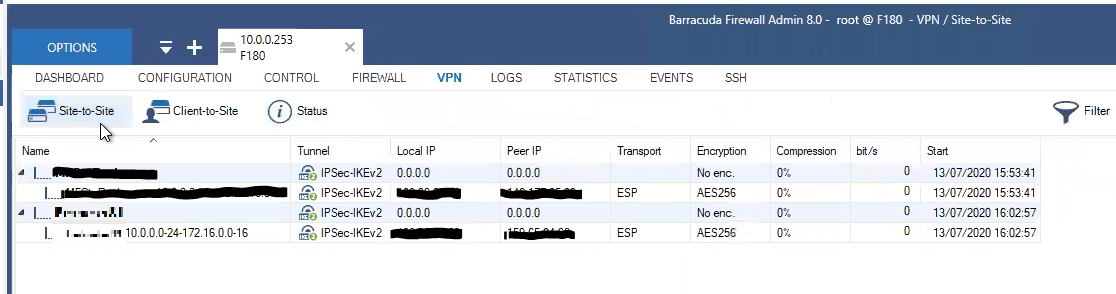
To verify that the tunnel is up, go to VPN > Site-to-Site. If the tunnel is listed in the table, then the tunnel is up.