Hardware Security Module (HSM)
Why Use an HSM?
Hardware Security Module (HSM) is a device that stores cryptographic keys.
HSM adds an additional layer of security to the network. HSM is designed to provide dedicated cryptographic functionality.
When Check Point Security Gateway![]() Dedicated Check Point server that runs Check Point software to inspect traffic and enforce Security Policies for connected network resources. uses an HSM, the HSM holds these objects for Outbound HTTPS Inspection
Dedicated Check Point server that runs Check Point software to inspect traffic and enforce Security Policies for connected network resources. uses an HSM, the HSM holds these objects for Outbound HTTPS Inspection![]() Feature on a Security Gateway that inspects traffic encrypted by the Secure Sockets Layer (SSL) protocol for malware or suspicious patterns. Synonym: SSL Inspection. Acronyms: HTTPSI, HTTPSi.:
Feature on a Security Gateway that inspects traffic encrypted by the Secure Sockets Layer (SSL) protocol for malware or suspicious patterns. Synonym: SSL Inspection. Acronyms: HTTPSI, HTTPSi.:
-
The Certificate Authority (CA) certificate (the certificate buffer and the key pair).
The administrator creates the CA certificate and the key pair before you configure the Security Gateway to work with an HSM.
-
The administrator creates at least one RSA key pair for fake certificates, with 1024-bit, 2048-bit, or 4096-bit length.
-
The administrator can create ECDSA key pairs for fake certificates, ECDSA 256, ECDSA 384 or ECDSA 521.
Check Point Security Gateway supports Thales Luna HSM. See Working with Thales Luna HSM.
|
|
Note - For other HSM vendors that use PKCS#11 API, contact Check Point Solution Center through a local Check Point Office. |
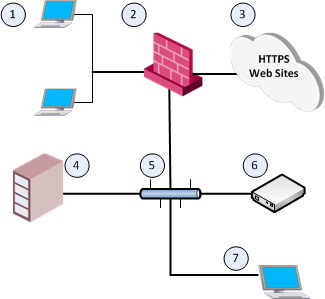
The Check Point Environment with an HSM
|
Item |
Description |
|---|---|
|
1 |
Internal computers that connect to HTTPS web sites through the Check Point Security Gateway. |
|
2 |
Check Point Security Gateway with HTTPS Inspection enabled. |
|
3 |
HTTPS web sites on the Internet. |
|
4 |
Check Point Security Management Server |
|
5 |
Interconnecting Network. |
|
6 |
HSM Server that stores and serves the SSL keys and certificates to the Check Point Security Gateway. |
|
7 |
HSM Client workstation used to create a Certificate Authority (CA) certificate on the HSM Server. |
|
|
Note - Check Point Security Gateway uses the HSM Server only for Outbound HTTPS Inspection. |

