Preventing IP Spoofing
IP spoofing replaces the untrusted source IP address with a fake, trusted one, to hijack connections to your network. Attackers use IP spoofing to send malware and bots to your protected network, to execute DoS attacks, or to gain unauthorized access.
Anti-Spoofing detects if a packet with an IP address that is behind a certain interface, arrives from a different interface. For example, if a packet from an external network has an internal IP address, Anti-Spoofing blocks that packet.
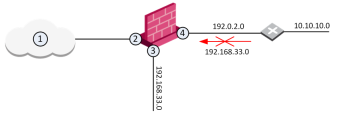
Example:
The diagram shows a Security Gateway![]() Dedicated Check Point server that runs Check Point software to inspect traffic and enforce Security Policies for connected network resources. with interfaces 2 and 3, and 4, and some example networks behind the interfaces.
Dedicated Check Point server that runs Check Point software to inspect traffic and enforce Security Policies for connected network resources. with interfaces 2 and 3, and 4, and some example networks behind the interfaces.
For the Security Gateway, Anti-Spoofing makes sure that:
- All incoming packets to 2 come from the Internet (1)
- All incoming packets to 3 come from
192.168.33.0 - All incoming packets to 4 come from
192.0.2.0or10.10.10.0
If an incoming packet to 2 has a source IP address in network 192.168.33.0, the packet is blocked, because the source address is spoofed.
When you configure Anti-Spoofing protection on a Check Point Security Gateway interface, the Anti-Spoofing is done based on the interface topology. The interface topology defines where the interface Leads To (for example, External (Internet) or Internal), and the Security Zone of interface.
Make sure to configure Anti-Spoofing protection on all the interfaces of the Security Gateway, including internal interfaces.
To configure Anti-Spoofing for an interface:
-
In SmartConsole
 Check Point GUI application used to manage a Check Point environment - configure Security Policies, configure devices, monitor products and events, install updates, and so on., from the left navigation panel, click Gateways & Servers and double-click the Security Gateway object.
Check Point GUI application used to manage a Check Point environment - configure Security Policies, configure devices, monitor products and events, install updates, and so on., from the left navigation panel, click Gateways & Servers and double-click the Security Gateway object.The Gateway Properties window opens.
-
From the navigation tree, select Network Management.
-
Click Get Interfaces.
-
Click Accept.
The Security Gateway network topology shows. If SmartConsole fails to automatically retrieve the topology, make sure that the details in the General Properties section are correct and the Security Gateway, the Security Management Server
 Dedicated Check Point server that runs Check Point software to manage the objects and policies in a Check Point environment within a single management Domain. Synonym: Single-Domain Security Management Server., and the SmartConsole can communicate with each other.
Dedicated Check Point server that runs Check Point software to manage the objects and policies in a Check Point environment within a single management Domain. Synonym: Single-Domain Security Management Server., and the SmartConsole can communicate with each other. -
Select an interface and click Edit.
The interface properties window opens.
-
From the navigation tree, click General.
-
In the Topology section of the page, click Modify.
The Topology Settings window opens.
-
In the Leads To section, select the type of network, to which this interface leads:
- Internet (External) - This is the default setting. It is automatically calculated from the topology of the Security Gateway. To update the topology of an internal network after changes to static routes, click Network Management > Get Interfaces in the Gateway Properties window.
- Override - Override the default setting.
If you Override the default setting:
-
Internet (External) - All external/Internet addresses
-
This Network (Internal) -
- Not Defined - All IP addresses behind this interface are considered a part of the internal network that connects to this interface
- Network defined by the interface IP and Net Mask - Only the network that directly connects to this internal interface
- Network defined by routes - The Security Gateway dynamically calculates the topology behind this interface. If the network of this interface changes, there is no need to click Get Interfaces and install a policy. For more, see Dynamically Updating the Security Gateway Topology.
- Specific - A specific object (a Network, a Host, an Address Range, or a Network Group) behind this internal interface
- Interface leads to DMZ - The DMZ that directly connects to this internal interface
-
Optional: In the Security Zone section, select User defined, check Specify Security Zone and choose the zone of the interface.
-
Configure Anti-Spoofing options (see Anti-Spoofing Options). Make sure that Perform Anti-Spoofing based on interface topology is selected.
-
Select an Anti-Spoofing action:
- Prevent - Drops spoofed packets
- Detect - Allows spoofed packets. To monitor traffic and to learn about the network topology without dropping packets, select this option together with the Spoof Tracking Log option.
-
Configure Anti-Spoofing exceptions (optional). For example, configure addresses, from which packets are not inspected by Anti-Spoofing:
-
Select Don't check packets from.
-
Select an object from the drop-down list, or click New to create a new object.
-
-
Configure Spoof Tracking - select the tracking action that is done when spoofed packets are detected:
- Log - Create a log entry (default)
- Alert - Show an alert
- None - Do not log or alert
-
Click OK twice to save Anti-Spoofing settings for the interface.
For each interface, repeat the configuration steps. When finished, install the Access Control policy.
Anti-Spoofing Options
-
Perform Anti-Spoofing based on interface topology - Select this option to enable spoofing protection on this external interface.
-
Anti-Spoofing action is set to - Select this option to define if packets will be rejected (the Prevent option) or whether the packets will be monitored (the Detect option). The Detect option is used for monitoring purposes and should be used in conjunction with one of the tracking options. It serves as a tool for learning the topology of a network without actually preventing packets from passing.
-
Don't check packets from - Select this option to make sure anti-spoofing does not take place for traffic from internal networks that reaches the external interface. Define a network object that represents those internal networks with valid addresses, and from the drop-down list, select that network object. The anti-spoofing enforcement mechanism disregards objects selected in the Don't check packets from drop-down menu.
-
Spoof Tracking - Select a tracking option.