Performing Push Operations (Old User Interface)
|
|
Note - To make the user interface clear and helpful, there is a new interface available. See Push Operations. |
Push operations are operations that the server pushes directly to client computers with no policy installation required.
|
|
Note - If there is no response from the Endpoint Security client, the Push Operation will time out after 24 hours. You must reinitiate the Push Operation. |
To add a Push Operation:
-
Go to the Push Operation view and click Add.
-
Select the push operation and click Next.
Category
Push Operations
Windows
macOS
Linux
Scan for Malware
Yes
Yes
Yes
Update Malware Signature Database
Yes
Yes
Yes
Restore Files from Quarantine
Yes
Yes
Yes
Forensics and Remediation
Analyze by Indicator
Yes
Yes
No
File Remediation
Yes
Yes
Yes
Isolate Computer
Yes
Yes
No
Release Computer
Yes
Yes
No
Agent Settings
Deploy New Endpoints
Yes
No
No
Collect Client Logs
Yes
Yes
No
Repair Client
Yes
No
No
Shutdown Computer
Yes
Yes
No
Restart Computer
Yes
Yes
No
Uninstall Client
Yes
Yes
No
Application Scan
Yes
Yes
No
Kill Process
Yes
Yes
No
Remote Command
Yes
Yes
Yes
Enable / Disable Self Protection
Yes
Yes
No
-
Select the devices on which you want to perform the push operation.

Note - You can perform Run Diagnostics on only one device at a time.
-
Click Next.
-
Configure the operation settings.
-
In the Full Path field, enter the path to file before it was quarantined including the file name. For example,
c:\temp\eicar.txt -
Click OK.
-
Click
and select the organization.
-
Click Update Selection.
-
Select the device and click Next.
-
Add Comment, optional comment about the action.
-
To move the files to quarantine, select Move the following files to quarantine.
-
To restore the files from quarantine, select Restore the following files from quarantine.
-
Click
.
-
From the drop-down:
-
Select Full file path or Incident ID:
-
In the Element field, enter the incident ID from the Endpoint Security client or enter the incident UID for the corresponding incident from the Logs menu in the Endpoint Security Administrator Portal. To obtain the incident UID, open the log entry and expand the More section to view the incident UID.
-
Click OK
-
-
Select MD5 Hash:
-
Enter or upload the Element.
-
Click OK.
-
-
-
Click Finish.
-
For Windows:
-
For Endpoint Security Client
 Application installed on end-user computers to monitor security status and enforce security policies. versions E88.31 and higher, client logs are stored in the directory C:\ProgramData\CheckPoint\Endpoint Security\Temp.
Application installed on end-user computers to monitor security status and enforce security policies. versions E88.31 and higher, client logs are stored in the directory C:\ProgramData\CheckPoint\Endpoint Security\Temp. -
For Endpoint Security Client versions E88.30 and lower, client logs are stored in the directory C:\Windows\SysWOW64\config\systemprofile\CPInfo.
-
-
For macOS, client logs are stored in the directory /Users/Shared/cplogs.
-
Upload CPInfo reports to Check Point servers
-
Upload CPInfo reports to Corporate server - Update the relevant corporate server information.
-
Allows administrators to run both signed (introduced by CP) and unsigned (ones the customer creates) scripts on the Endpoint Security Client devices.
-
Especially useful in a non-AD environment.
-
Supplies tools/fixes to customers without the need to create new EP client/server versions.
-
Saves passwords securely when provided.
-
Enable - Enables the self protection capabilities.
-
Disable - Disables the self protection capabilities.
-
Timeout Command Expiration - Select the expiration time for the command.

Note - After the timeout, the command expires, and the self protection capabilities will be enabled automatically.
-
Process - Captures memory dumps for one or more processes using process name or PID.

Notes:
-
The system generates multiple memory dumps if several processes share the same name.
-
Memory dumps are not supported for Protected Process Light (PPL) processes.
-
-
Kernel - Collects a kernel memory dump without requiring a system reboot.

Note - Kernel memory dump is not supported on Windows 7 devices.
-
Full - Initiates a BSOD to collect a full or active memory dump (requires prior configuration on the target device). For more information, see Dell documentation.

Note - It is optional to reboot the endpoint to collect the Full memory dump.
-
Upload Memory Dump to AWS S3 - After the push operation is successful, the system shows a download option in the Operation output column of the Push Operation Endpoint Details section.
-
Upload Memory Dump to Check Point servers - After the push operation is successful, the system uploads the memory dump to this location:
-
For Windows Endpoint Security Client versions E88.31 and higher, client logs are stored in the directory C:\ProgramData\CheckPoint\EndpointSecurity\Temp.
-
For Windows Endpoint Security Client versions E88.30 and lower, client logs are stored in the directory C:\Windows\SysWOW64\config\systemprofile\CPInfo.
-
For macOS, client logs are stored in the directory /Users/Shared/cplogs.
-
-
Upload Memory Dump to Corporate server - Enter your corporate server details. After the push operation is successful, the system uploads the memory dump to the configured location in the corporate server.
-
Automated packaging and upload of memory dump - All memory dumps are automatically zipped, segmented if necessary, and uploaded to the designated destination (Check Point FTP, Amazon S3, or custom FTP servers).
-
On 32-bit Windows systems, the ZIP file name is not displayed when uploading full memory dumps to an FTP server.
-
The Memory Dump feature is supported only on Endpoint Security for Windows client version E89.05 and later.
-
Under User Notification:
-
To notify the user about the push operation, select the Inform user with notification checkbox.
-
To allow the user to post pone the push operation, select the Allow user to postpone operation checkbox.
-
-
Under Scheduling:
-
To execute the push operation immediately, click Execute operation immediately.
-
To schedule the push operation, click Schedule operation for and click to select the date.
-
-
Click Finish.
-
View the results of the operations on each endpoint in the Endpoint List section (in the Push Operations menu) at the bottom part of the screen.
|
Push Operations |
Description |
|---|---|
|
Scan for Malware |
Runs an Anti-Malware scan on the computer or computers, based on the configured settings. |
|
Update Malware Signature Database |
Updates malware signatures on the computer or computers, based on the configured settings. |
|
Restore Files from Quarantine |
Restores files from quarantine on the computer or computers, based on the configured settings. To restore files from quarantine: |
|
Push Operations |
Description |
|---|---|
|
Analyze by Indicator |
Manually triggers collection of forensics data for an endpoint device that accesses or executes the indicator. The indicator can be a URL, an IP, a path, a file name or an MD5. |
|
File Remediation |
Quarantines malicious files and remediates them as necessary. To move or restore files from quarantine: |
|
Isolate Computer |
Makes it possible to isolate a specific device that is under malware attack and poses a risk of propagation. This action can be applied on one or more devices. The Firewall component must be installed on the client in order to perform isolation. Only DHCP, DNS and traffic to the management server are allowed. |
|
Release Computer |
Removes device from isolation. This action can be applied on one or more devices. |
|
Push Operations |
Description |
2FA Required |
||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
|
Deploy New Endpoints |
Installs the Initial Client on the target devices remotely using any device as the medium to run the push operation. This is suitable if do not have third party tools such as Microsoft System Center Configuration Manager (SCCM) or Intune to install the client.
|
No | ||||||||||||||||
|
Collect Client Logs |
Collects CPInfo logs from an endpoint based on the configured settings.
|
No | ||||||||||||||||
|
Repair Client |
Repairs the Endpoint Security client installation. This requires a computer restart.
|
No | ||||||||||||||||
|
Shutdown Computer |
Shuts down the computer or computers based on the configured settings. |
No | ||||||||||||||||
|
Restart Computer |
Restarts the computer or computers based on the configured settings. |
No | ||||||||||||||||
|
Uninstall Client |
Uninstalls the Endpoint Security client remotely on the selected devices. This feature is supported for E84.30 client and above. |
Yes | ||||||||||||||||
|
Application Scan |
Collects all available applications in a certain folder on a set of devices and then adds them to the application repository of the "Application Control |
No | ||||||||||||||||
|
Kill Process |
Remotely kills/ terminate the processes. |
No | ||||||||||||||||
|
Remote Command |
|
Yes | ||||||||||||||||
|
Enable / Disable Self Protection |
This Push Operation allows the administrator to enable or disable the self protection capabilities on endpoints.
Supported fields: |
|
||||||||||||||||
|
Collect Memory Dump |
Collects Memory Dump from an endpoint based on the configured settings. Memory dump is a snapshot of system memory at specific instance of the active process and the operating system.
|
|
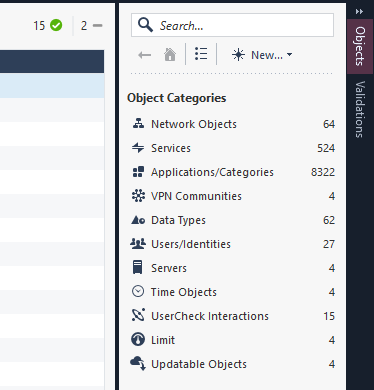
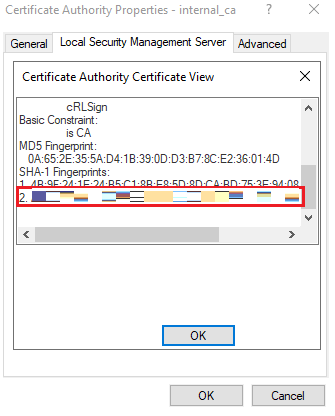
Collecting Fingerprint details for a VPN Site:
-
In SmartConsole
 Check Point GUI application used to manage a Check Point environment - configure Security Policies, configure devices, monitor products and events, install updates, and so on., in the right pane, under Object Categories, click Servers > Trusted CA > internal ca.
Check Point GUI application used to manage a Check Point environment - configure Security Policies, configure devices, monitor products and events, install updates, and so on., in the right pane, under Object Categories, click Servers > Trusted CA > internal ca.The Certificate Authority Properties window appears.
-
Click the Local Security Management tab.
-
Under Certificate, click View.
The Certificate Authority Certificate View window appears.
-
Scroll down to SHA-1 Fingerprints. The fingerprint is on line number 2.
-
Manually add the VPN site in the client. For more information, see Endpoint Security Clients User Guide.
-
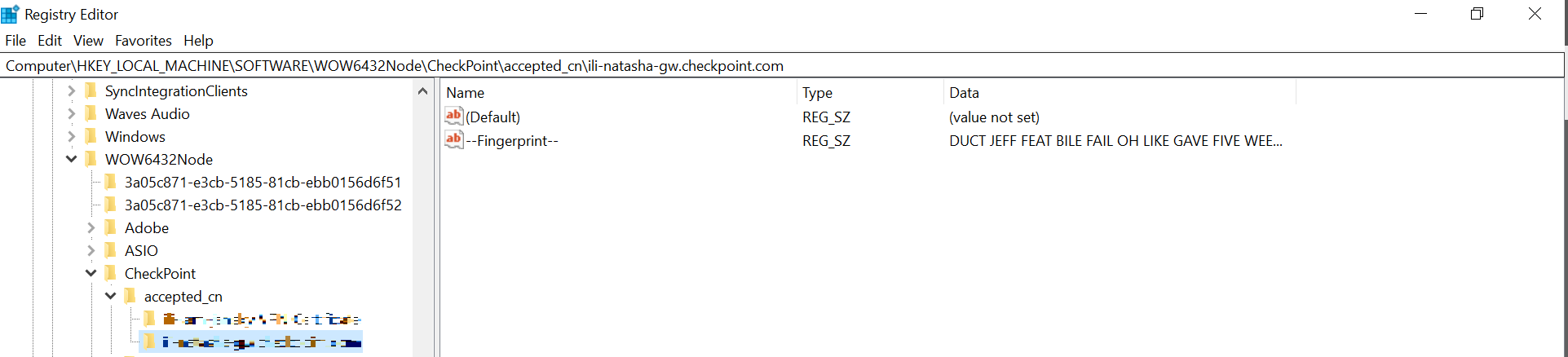
After you add and connect to the VPN site successfully, In Registry Editor, go to Computer\HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\CheckPoint\accepted_cn.
-
It displays a folder with the display name of your VPN site.
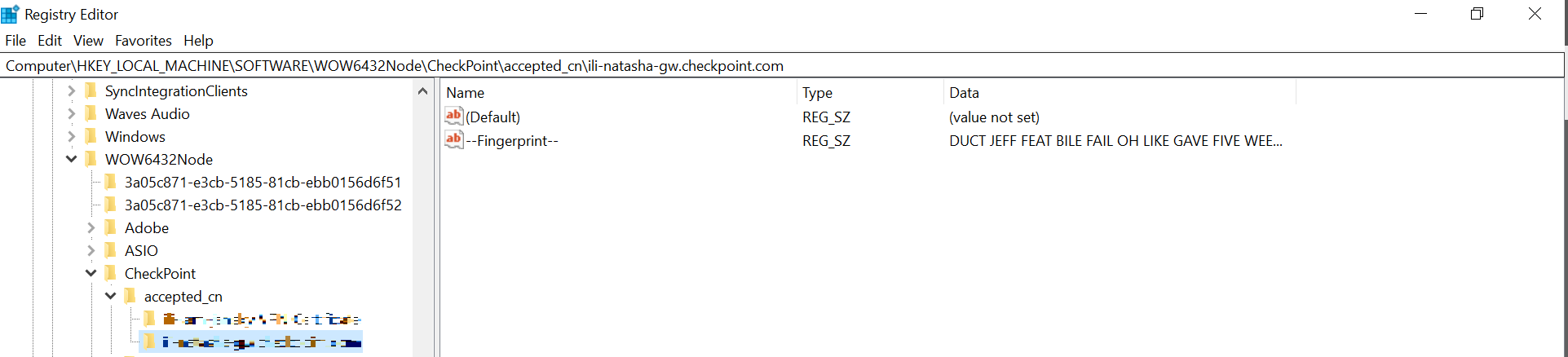
-
Double-click the folder.
-
In the right pane, under Name, double-click -- Fingerprint--.
The Edit String window appears.
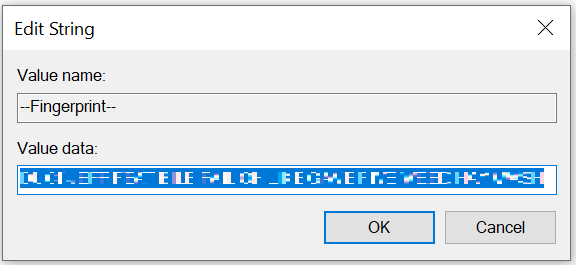
-
Copy the fingerprint key from the Value data field.
-
Click Cancel to close the window.
-
Paste the fingerprint key in the Fingerprint field.
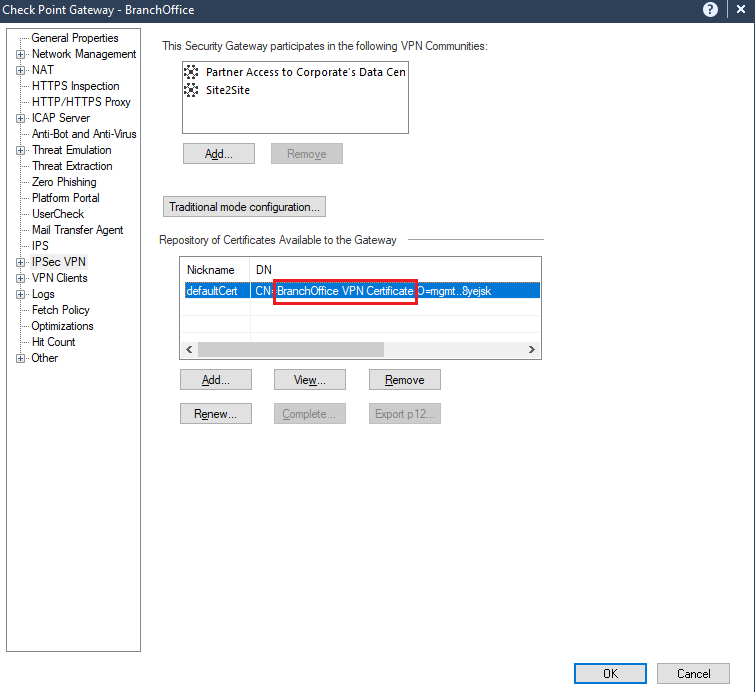
Collecting Remote Access Gateway Name
To get the Remote Access Gateway name from SmartConsole:
-
In SmartConsole, go to Gateways and Servers.
-
Double-click the gateway.
The Check Point Gateway window appears.
-
Double-click IPSec VPN.
-
Under Repository of Certificates Available to the Gateway, in the table, expand the DN column. The value after CN= indicates the remote access gateway name.
To get the remote access gateway name from the device:
-
In Registry Editor, go to Computer\HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\CheckPoint\accepted_cn.
-
It shows a folder with the display name of your VPN site. Copy the folder name and paste it in the Remote Access Gateway Name field.