Introduction to Endpoint Security
Check Point endpoint security includes data security, network security, advanced threat prevention, forensics, and remote access VPN solutions. It offers simple and flexible security administration: The entire endpoint security suite can be managed centrally using a single management console.
Managing the Security of Users, Not Just Machines
One user may have multiple computers and some computers may have multiple users. Therefore, the Security Policies for some Endpoint Security components are enforced for each user, and some are enforced on computers.
Organization-Centric model
You can import users and computers to the Endpoint Security Management Server, which uses your organization's existing hierarchy to provide a graphical tree of endpoints computers. You then define software deployment and security policies centrally for all nodes and entities, making the assignments as global or as granular as you need.
Policy-centric Model
You can predefine security policies before setting up the organization. The Endpoint Security Management Server interface provides a granular view of all the Endpoint Security policies, grouped by the components they configure.
You create and assign policies to the root node of the organizational tree as a property of each Endpoint Security component. Policies can be deployed one by one or all together. Because different groups, networks, OUs, computers, and users have different security needs, you can configure different components accordingly.
Endpoint Security Client
You can define policies in SmartEndpoint for the Endpoint Security client components. The Endpoint Security client is available on Windows OS and macOS.
These are the Endpoint Security components that are available on Windows:
|
Component |
Description |
|---|---|
|
Compliance
|
Allows you to enforce endpoint compliance on multiple checks before users log into the network. You can check that the:
|
|
Anti-Malware
|
Protects clients from known and unknown viruses, worms, Trojan horses, adware, and keystroke loggers. |
|
Media Encryption and Media Encryption & Port Protection |
Protects data stored on the computers by encrypting removable media devices and allowing tight control over computers' ports (USB, Bluetooth, and so on). |
|
Firewall and Application Control |
Defines the topology of the organizational network, separating it into Trusted and Internet domains. Blocks or allows network traffic based on attributes of network connections. Controls network access on a per-application basis, letting you restrict application access by zone and direction. |
|
Full Disk Encryption
|
Combines Pre-boot protection, boot authentication, and strong encryption to make sure that only authorized users are given access to information stored on desktops and laptops. Manages:
|
|
Remote Access VPN
|
Provide secure, seamless access to corporate networks remotely, over IPsec VPN. |
|
URL Filtering
|
Lets organizations control access to web sites by category, user or group. |
|
Endpoint Security Anti-Bot |
Detects bot-infected machines and blocks bot C&C communication to prevent bot damage. Provides detailed information about the device affected by the bot activity, about the bot process itself, and other relevant information. |
|
Endpoint Security Anti-Ransomware, Behavioral Guard and Forensics |
Prevents ransomware attacks. Monitors files and the registry for suspicious processes and network activity. Analyzes incidents reported by other components. |
|
Endpoint Security Threat Extraction, Emulation and Anti-Exploit |
Threat Extraction quickly delivers safe files while the original files are inspected for potential threats. Threat Emulation sends files on the endpoint computer to a sandbox for emulation to detect evasive zero-day attacks. |
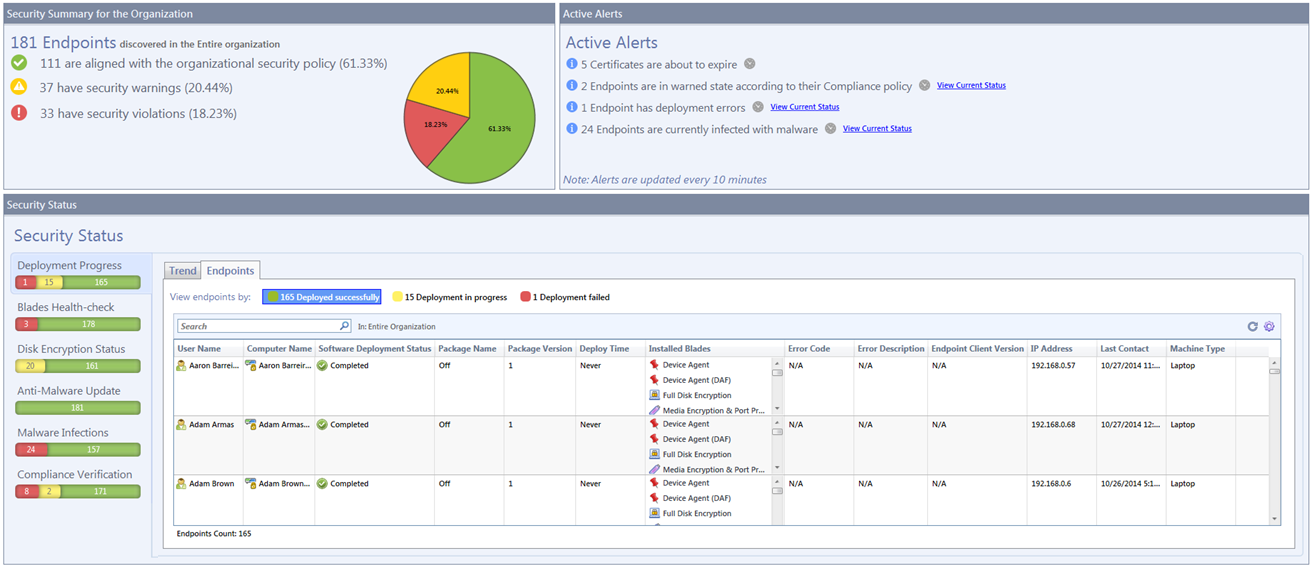
Centralized Monitoring
The Endpoint Security Management Server provides reports for the whole system as well as individual users and computers.
-
General status reports can be viewed in the SmartEndpoint GUI client. You can monitor Endpoint Security client connection status, compliance to security policy status, information about security events, and more.
-
Historical data for clients and servers can be viewed in the Logs tab of the SmartConsole Logs & Monitor view.
Centralized Deployment
Deployment in the Endpoint Security Management Server lets you control specific components and Endpoint Security versions installed on the protected end-user computers.