Auth0
Prerequisites
-
Administrator access to the Check Point SASE Administrator Portal.
-
Administrator account with the Identity Provider Management Portal.
High-Level Procedure
Step 1 - Configure the Auth0 Management Portal
-
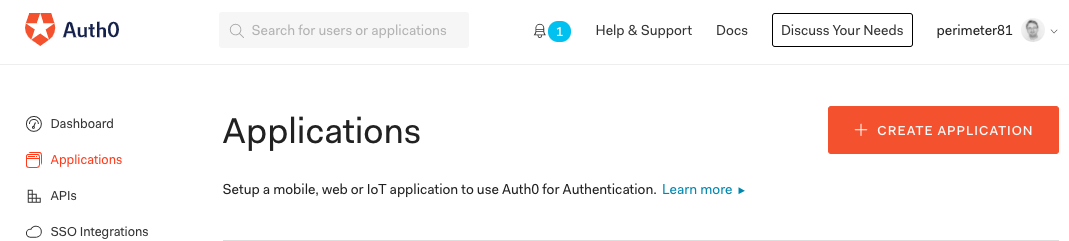
Log in to Auth0 Management Portal.
-
From the left navigation pane, click Applications.
-
Click Create Application.
-
In the Name field, enter a name for the application.
-
Select Regular Web Application and click Create.
-
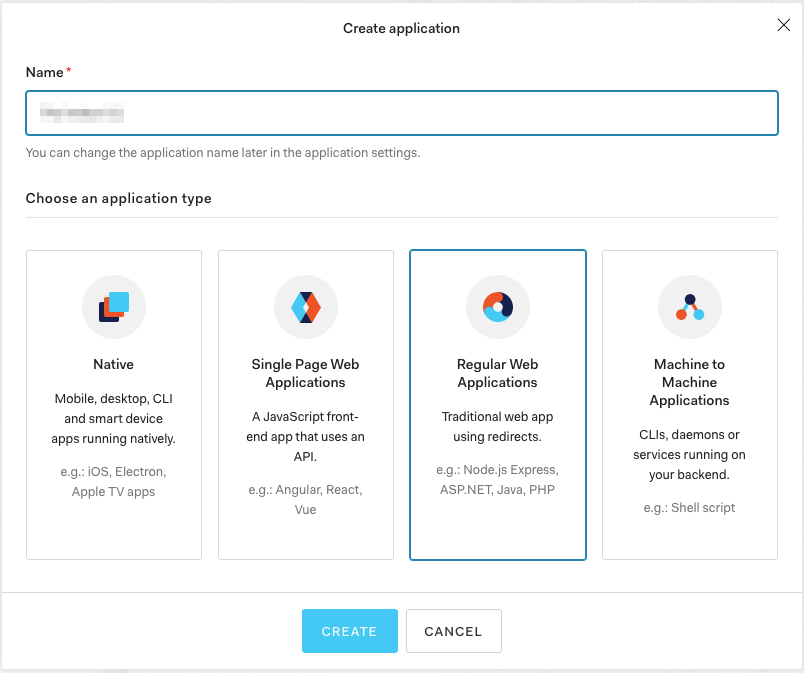
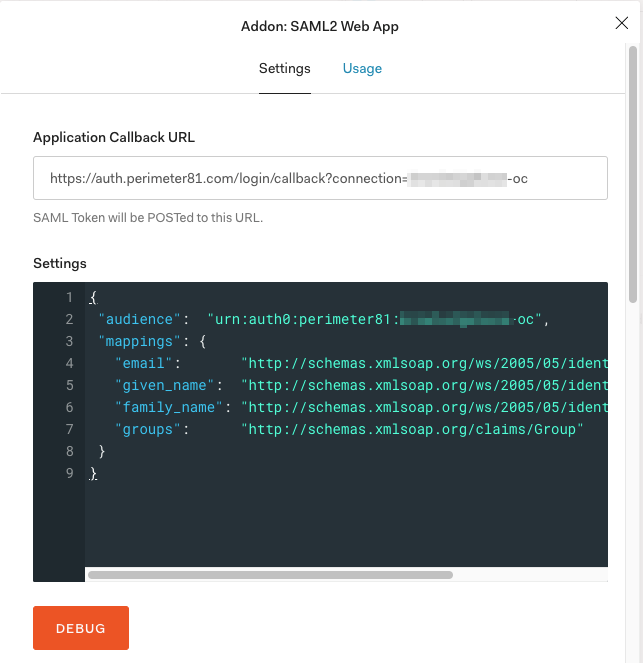
Go to Addons tab and toggle SAML2 Web App to ON.
The SAML2 Web App window appears.
-
In the Settings tab, enter these values:
-
Application Callback URL: US-based platform:
https://auth.perimeter81.com/login/callback?connection={{WORKSPACE}}-ocEU-based platform:https://auth.eu.sase.checkpoint.com/login/callback?connection={{WORKSPACE}}-ocAU-based platform:https://auth.au.sase.checkpoint.com/login/callback?connection={{WORKSPACE}}-ocIN-based platform:https://auth.in.sase.checkpoint.com/login/callback?connection={{WORKSPACE}}-oc -
Settings: Copy the code, replace
{{WORKSPACE}}with your Check Point SASE workspace name and paste it in Settings.Copy{
"audience": "urn:auth0:perimeter81:{{WORKSPACE}}-oc",
"mappings": {
"email": "http://schemas.xmlsoap.org/ws/2005/05/identity/claims/emailaddress",
"given_name": "http://schemas.xmlsoap.org/ws/2005/05/identity/claims/givenname",
"family_name": "http://schemas.xmlsoap.org/ws/2005/05/identity/claims/surname",
"groups": "http://schemas.xmlsoap.org/claims/Group"
}
}
-
-
Click Enable to save and activate the application.
-
Click Debug and verify your configuration.
-
Go to the Usage tab.
-
Click Download Auth0 certificate.
-
Copy the Identity Provider Login URL.
Step 2 - Configure the Check Point SASE Administrator Portal
-
Log in to the SASE Administrator Portal with a administrator account.
-
Go to Settings > Identity Providers.
-
Click Add Provider.
The Add identity provider pop-up appears.
-
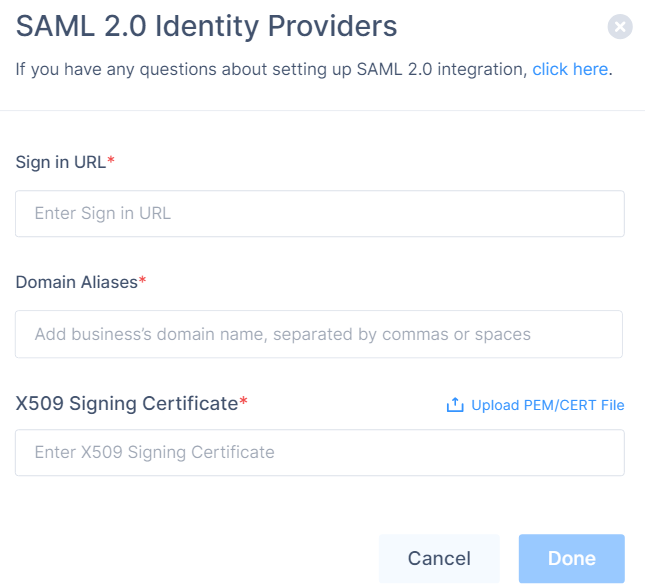
Select SAML 2.0 Identity Providers and click Continue.
-
In the Sign in URL field, enter the Identity Provider Sign-in URL from your SAML Identity Provider.
Identity Provider
Sign in URL
Generic SAML
Identity Provider Sign in URL
Active Directory Federation Services (AD FS)
https://{{Your ADFS Domain}}/adfs/lsAuth0
Auth0 login URL
OneLogin
SAML 2.0 Endpoint (HTTP) value
PingOne
https://sso.connect.pingidentity.com/sso/idp/SSO.saml2?idpid={{idpid}}PingFederate
https://sso.{{Your PingFederate Domain}}.com/idp/SSO.saml2Rippling
Rippling IdP Sign-in URL.
JumpCloud
JumpCloud IDP URL
Okta
Okta Sign on URL
Google Applications
SSO URL
-
In the Domain Aliases field, enter the business domain names separated by commas or space.
-
In the X509 Signing Certificate field, enter the X.509 signing certificate for the application from the SAML Identity Provider.
If you have the signing certificate as PEM/CERT file, click Upload PEM/CERT File and select the file.
-
Click Done.
|
|
Note - After the first successful authentication of a member with SAML, Check Point SASE does this:
|