Appendix A
Integration Information
|
Information Name |
Description |
||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
|
|
|||||||||||||||
|
UEM Web Services URL |
|
||||||||||||||
|
UEM API Account Username |
|
||||||||||||||
|
UEM API Account Password |
|
||||||||||||||
|
UEM Organization Group(s) |
|
||||||||||||||
|
UEM Mitigation Group |
|
||||||||||||||
|
Tag Device Status (Boolean tags) |
CHKP_Status_Provisioned CHKP_Status_Active CHKP_Status_Inactive |
||||||||||||||
|
Tag Device Risk (Boolean tags) |
CHKP_Risk_None CHKP_Risk_Low CHKP_Risk_Medium CHKP_Risk_High |
||||||||||||||
|
Mobile Security Gateway |
Security gateway servers: Enter the Security Gateway
|
||||||||||||||
|
Mobile Security App Name (iOS / Android) |
Mobile Security Protect |
||||||||||||||
|
Mobile Security App ID (iOS) |
com.checkpoint.capsuleprotect |
||||||||||||||
|
Mobile Security App ID (Android) |
com.lacoon.security.fox |
Deploying a CA certificate using Zero-Touch for HTTPS Traffic Inspection
-
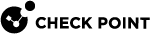
In your Mobile Security dashboard, go to Policy and expand your policy profile (example, Global).
-
Click any one of these:
-
Device
-
Application
-
File
-
Network
-
-
Click Network Protection.
-
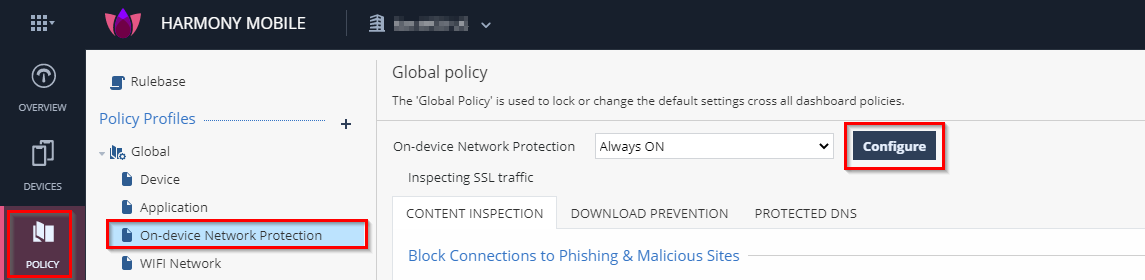
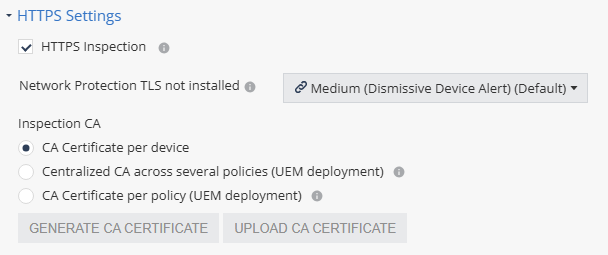
Go to HTTPS Settings and select the HTTPS Inspection checkbox.
The Enable SSL Inspection window appears.
-
Click Continue.
-
In the Inspection CA section, select the CA certificate that ONP will use to inspect HTTPS traffic on the end-user device.
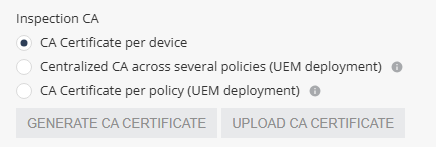
Select one of these:
-
Centralized CA across several policies - Allows you to use the centralized CA certificate across several policies. To generate the centralized CA certificate, go to Settings > Central HTTPS Inspection Root CA.

Note - If you initially chose to use a centralized CA certificate but later changed to a different CA certificate option:
-
The current policy will no longer use the centralized certificate.
-
The centralized CA certificate remains active and continues to be associated with all other policies in your account.
-
-
CA Certificate per policy - If your organization uses a UEM, you can generate a new CA certificate for each policy, download and deploy it on the end-user device through UEM.
-
To generate a CA certificate issued by Check Point, click Generate CA Certificate. The new certificate is valid for one year from the current date, as shown in Expiration date.
-
To use a self-signed or a third-party CA certificate, click Upload CA Certificate.
For the Transport Layer Security (TLS
 Transport Layer Security. A security protocol designed to facilitate privacy and data security for communications over the Internet.) certificate to be valid:
Transport Layer Security. A security protocol designed to facilitate privacy and data security for communications over the Internet.) certificate to be valid:-
The certificate must have a lifecycle of at least 30 days and not longer than 390 days.
-
The certificate must be valid for more than 30 days from the time it is uploaded to the Mobile Security Administrator Portal.
-

Note - Check Point recommends you renew the CA certificate at least two weeks before the expiration date. To renew the CA certificate, see sk181288.
-
-
|
|
Note - When using different policies for device groups, the enforcement of the certificate pushed by UEM Name may take up to 24 hours on iOS devices. This limitation is not relevant if you use the Global policy for the entire fleet of devices. |