Mobile Application Management (MAM) & Mobile Threat Defense (MTD) Integration
This section is relevant if you use Microsoft Intune Mobile Application Management (MAM) to manage the use of mobile applications in your organization. For more information, see Microsoft Intune App Management.
When you integrate MAM with Mobile Security:
-
For devices managed by Microsoft Intune UEM
 Unified Endpoint Management. An architecture and approach that controls different types of devices such as computers, smartphones and IoT devices from a centralized command point., it blocks access to Microsoft Office 365 applications if Mobile Security detects a device threat above a specific risk level.
Unified Endpoint Management. An architecture and approach that controls different types of devices such as computers, smartphones and IoT devices from a centralized command point., it blocks access to Microsoft Office 365 applications if Mobile Security detects a device threat above a specific risk level. 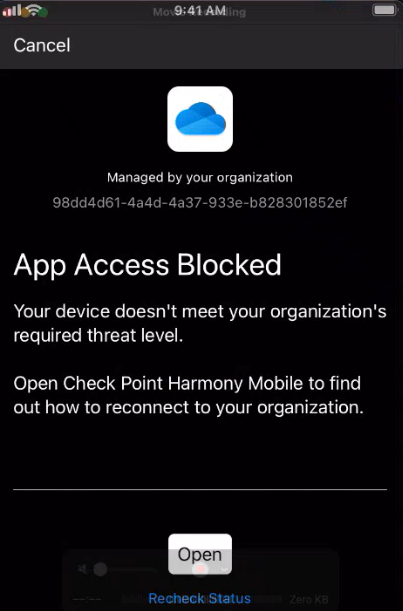
-
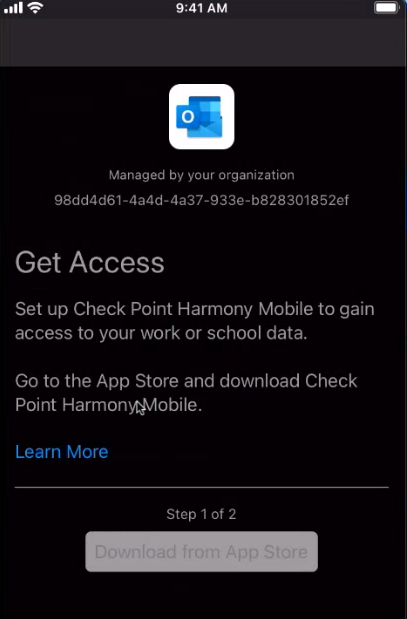
For Bring Your Own Device (BYOD), MAM blocks access to Microsoft Office 365 apps unless the Harmony Mobile Protect app is installed on the BYOD device. It automatically prompts the user to download and install the Harmony Mobile Protect app.
Applying the Mobile Application Management (MAM) Policy
|
|
Note - To manage the mobile applications, it is mandatory to enforce the MAM policy on the end-user device. |
-
Configure the MTD connector in Microsoft Intune. See Enabling the MTD Connector in Microsoft Intune Portal.
-
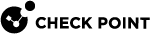
In the Microsoft Intune Admin Center, go to Tenant administration > Connectors and tokens.
-
Go to Mobile Threat Defense and click Create.
-
In the MTD Connector section, click Check Point Mobile Security.
-
Configure the Compliance policy evaluation and App protection policy evaluation settings for Android and iOS devices as shown in this screen.
-
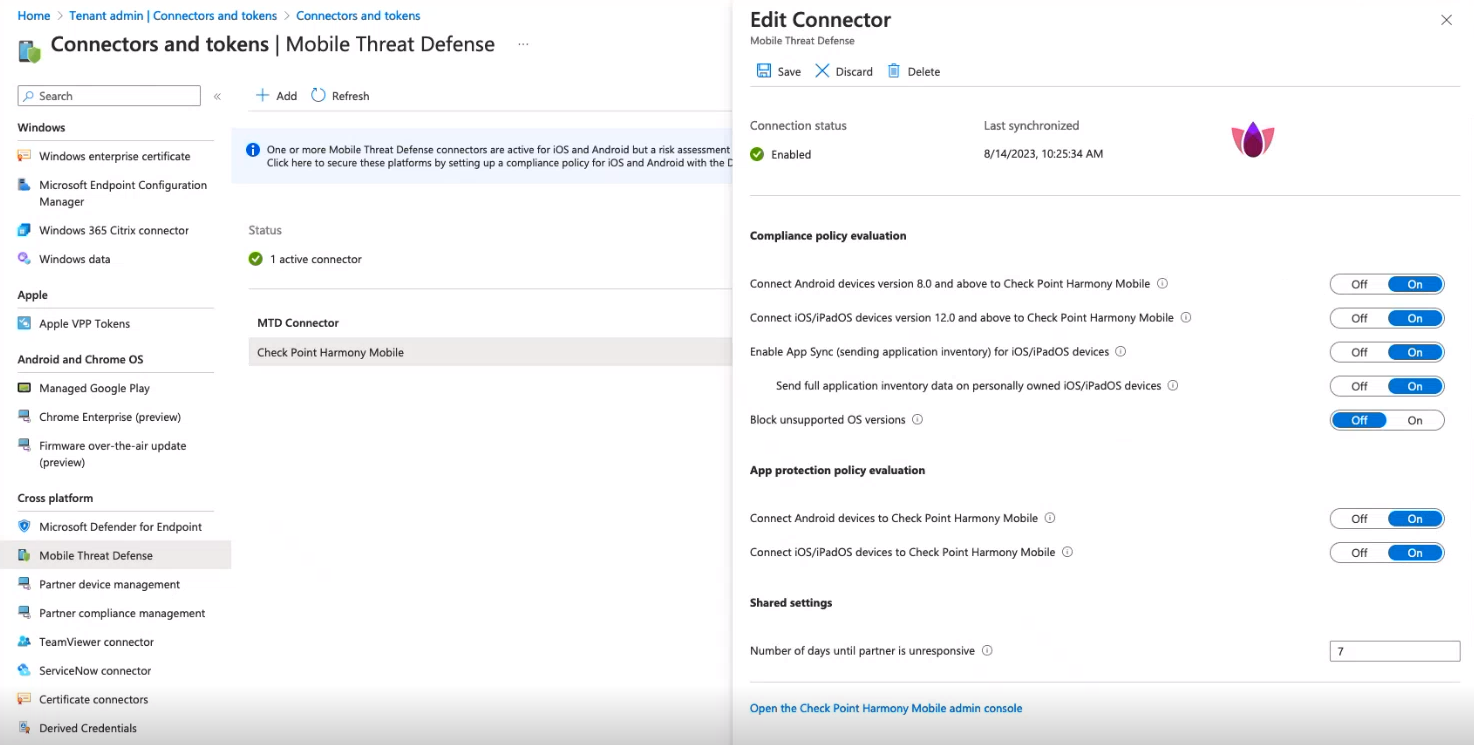
Go to Devices > Manage devices > Conditional access > Policies.
-
Click New policy.
-
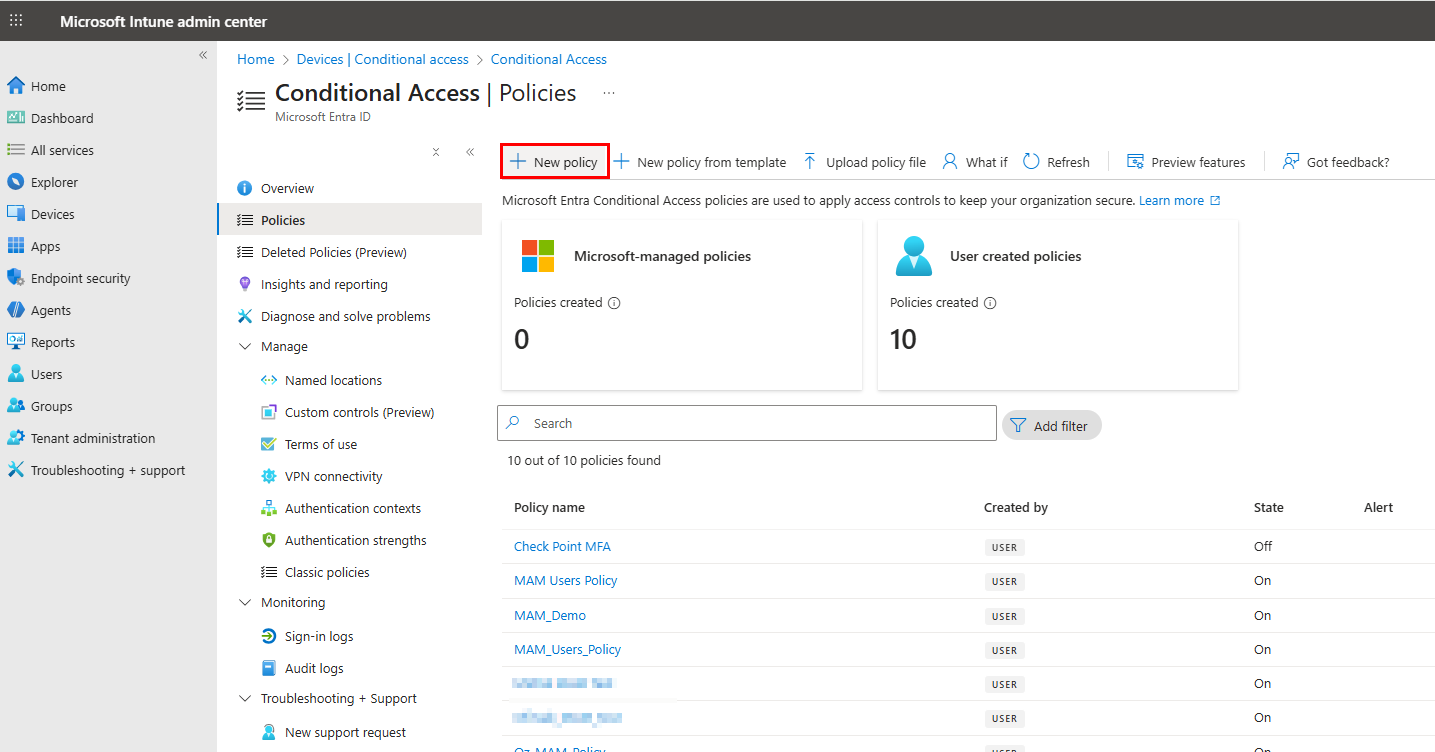
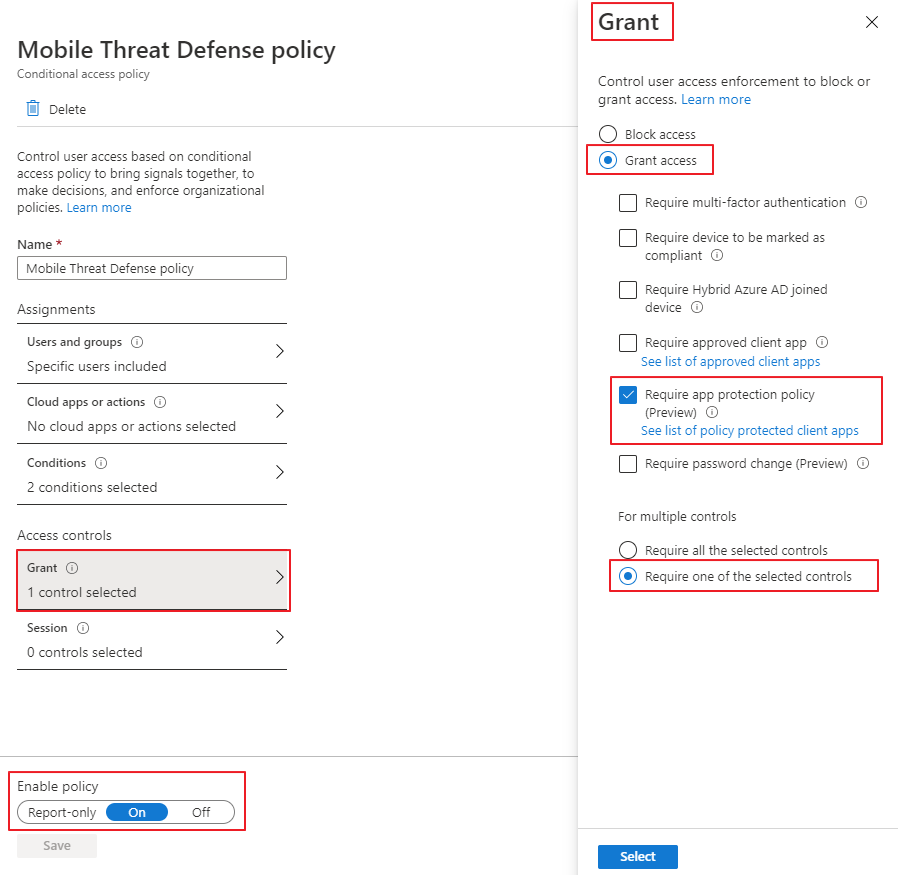
Enter Name as Mobile Threat Defense policy.
-
In the Users or agents section, search and assign the MTD policy to your group.
-
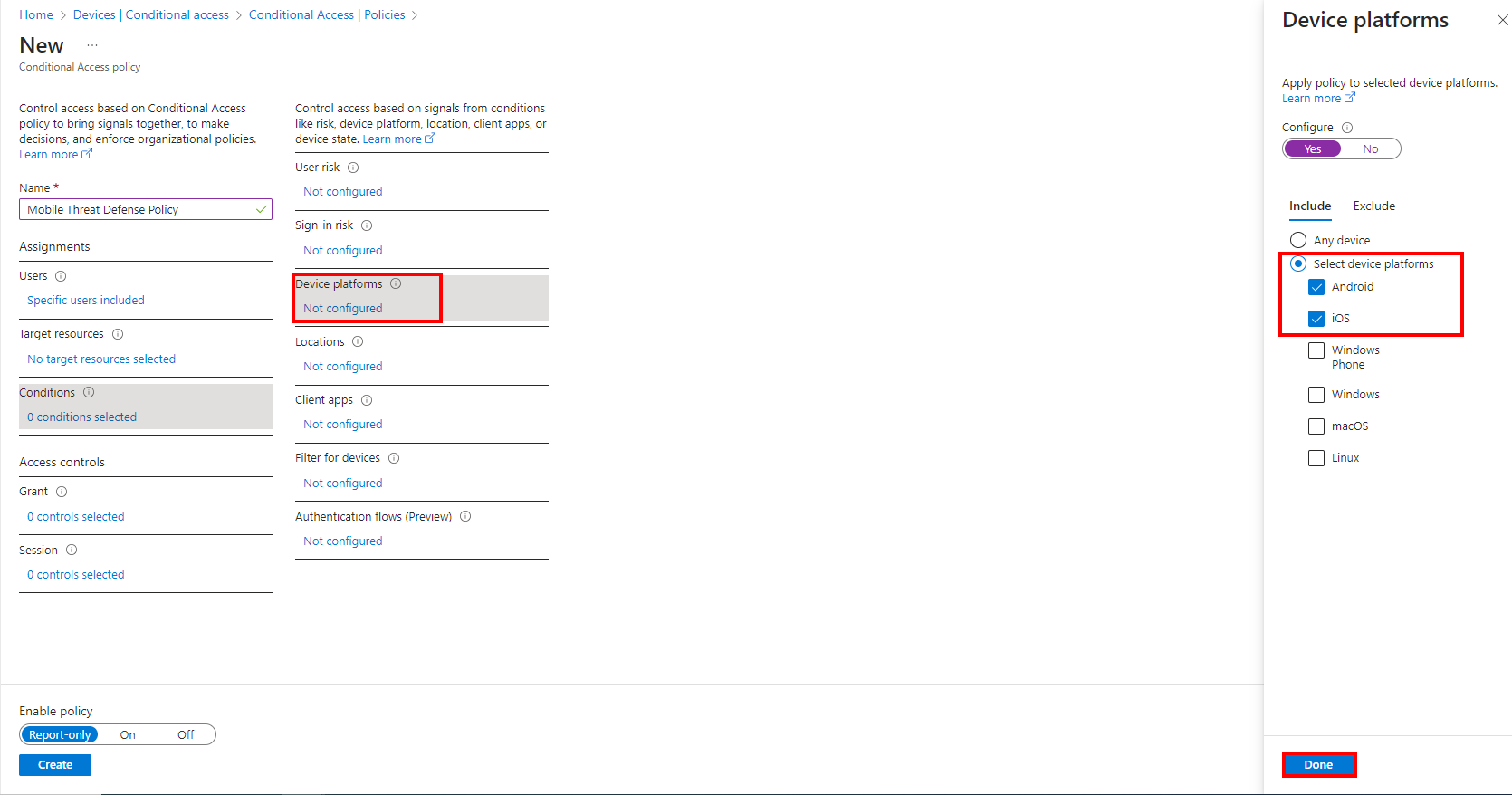
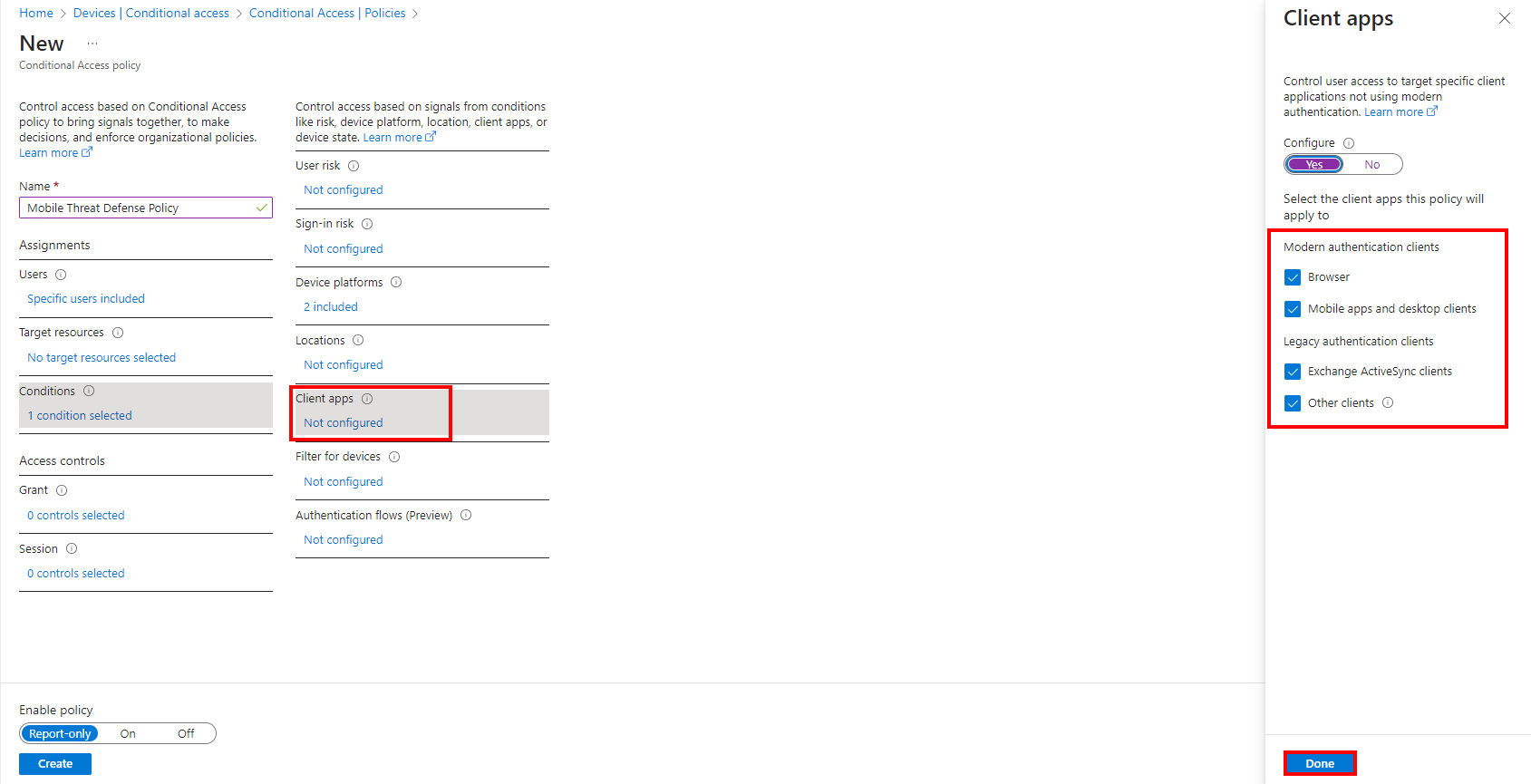
In Conditions:
-
In Grant section, click controls selected and select these:
-
Require app protection policy
-
For multiple controls - Require one of the selected controls
-
Click Select.
-
-
Turn on Enable policy and click Create.
-
-
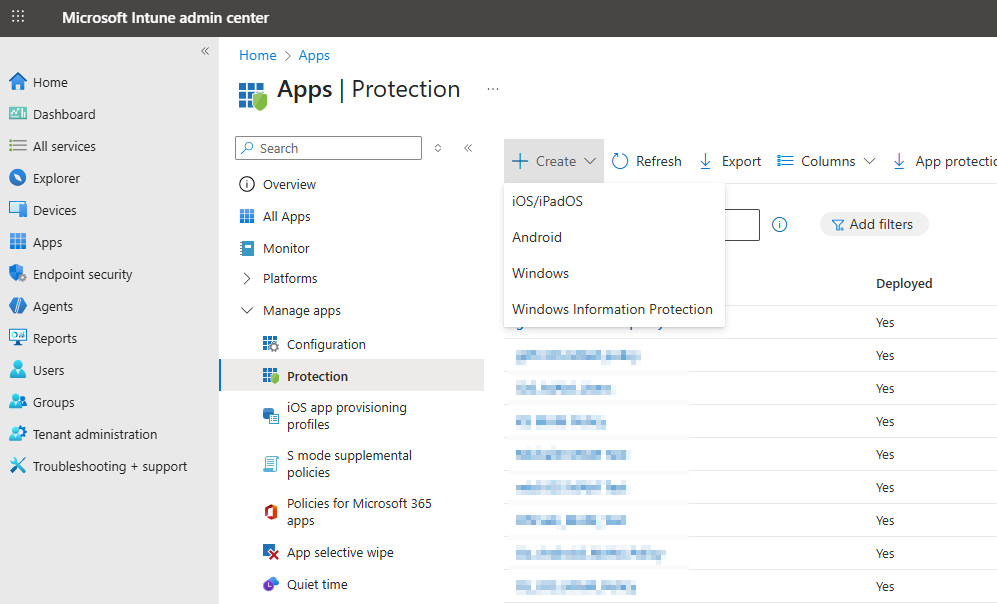
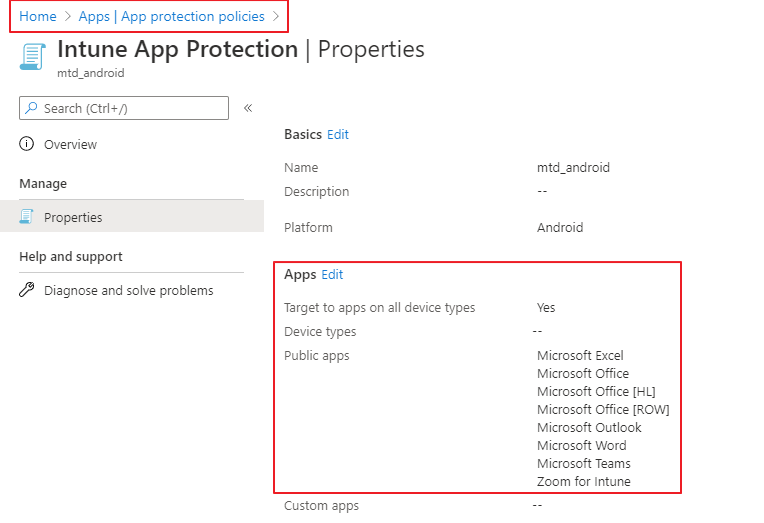
Go to Apps > Protection > Create and select the platform.
-
In the Basics tab, enter a name for your app protection policy.
-
Click Next.
-
In the Apps tab, select the apps that you want to enforce the MAM policy.
-
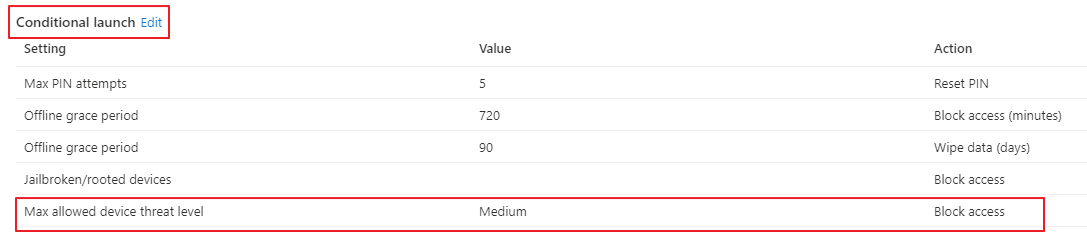
Go to Conditional launch tab > Device conditions and add the Max allowed mobile threat level setting.
The system blocks access to the selected apps if Mobile Security detects a device threat above the Max allowed mobile threat level.
-
In the Assignments tab, under Included groups, click Add groups.
-
Search and select your security group.
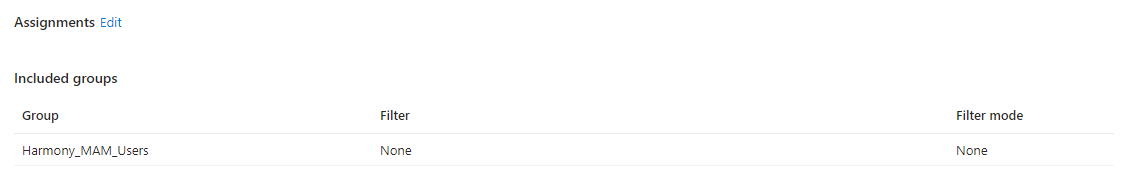
-
Click Next.
-
Review and create the policy.
MAM enforces the App protection policy on your device group.
-
Configuring the Mobile Security Administrator Portal
Prerequisite
Configure Microsoft Intune integration on Mobile Security Administrator Portal. See Configuring the Mobile Security Administrator Portal UEM Integration Settings.
To configure MAM integration:
-
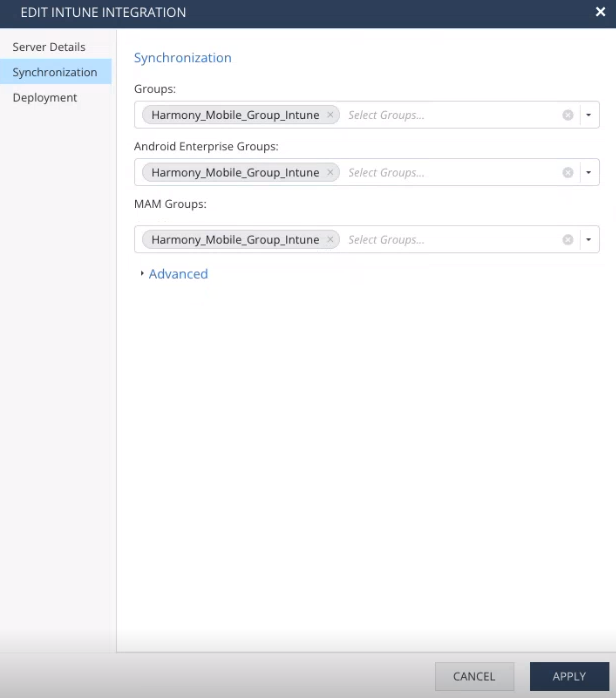
In the Mobile Security Administrator Portal, go to Settings > Integrations > Microsoft Intune > Edit.
-
In the Synchronization section, add the MAM group in both Groups and MAM Groups.
The MAM policy is enforced on these device groups.

Best Practice - Use separate device groups for Microsoft Intune UEM managed devices and MAM devices.

Note - Make sure not to sync the MAM group to the Android Enterprise Groups section.