iOS Profiles
iOS Profiles are unique to Apple iOS devices. To assist the mobile device admins, Apple developed a tool called Profiles, which includes Network Configuration Profiles, Provisioning![]() Check Point Software Blade on a Management Server that manages large-scale deployments of Check Point Security Gateways using configuration profiles. Synonyms: SmartProvisioning, SmartLSM, Large-Scale Management, LSM. Profiles, and Certificates. Network profiles are also used by the legitimate VPN applications. The shortcoming of iOS Profiles is that it opens a security hole where an attacker can create and install a malicious network configuration profile. It makes them act as a Man-In-The-Middle and collect all the information flowing from the device.
Check Point Software Blade on a Management Server that manages large-scale deployments of Check Point Security Gateways using configuration profiles. Synonyms: SmartProvisioning, SmartLSM, Large-Scale Management, LSM. Profiles, and Certificates. Network profiles are also used by the legitimate VPN applications. The shortcoming of iOS Profiles is that it opens a security hole where an attacker can create and install a malicious network configuration profile. It makes them act as a Man-In-The-Middle and collect all the information flowing from the device.
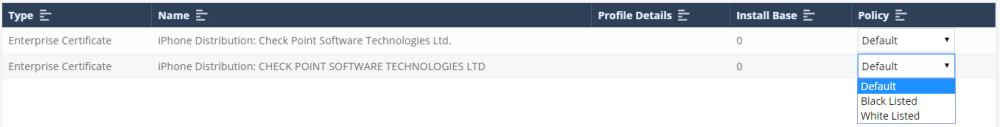
Information About iOS Profiles
The iOS Profiles tab shows the Network Configuration Profiles. It allows the administrator to get a clear view on the profiles installed on the devices in the organization.
|
Item |
Description |
|---|---|
|
Type |
Displays the type of profile – Wi-Fi configuration, VPN, etc. |
|
Name |
Profile name as it appears on the iOS device. |
|
Profile Details |
Profile details indicated the information (properties) of the profile. Including remote address, IP and servers. |
|
Install Base |
Number of devices currently installed with this specific profile. |
|
Policy |
Policy drop down menu allows the Administrator to set the alert level of a specific profile in the dashboard. |
The iOS Profiles tab also shows the Provisioning Profiles that are installed on the organization’s iOS devices.
You can filter and select the profile information presented in the table. Filtering options include Device Type, Device Name, Install Base, and Policy.