Network
Use this network diagram to configure your system. Make sure to replace the IP addresses in the sample environment with the IP addresses in your environment.
Network Diagram
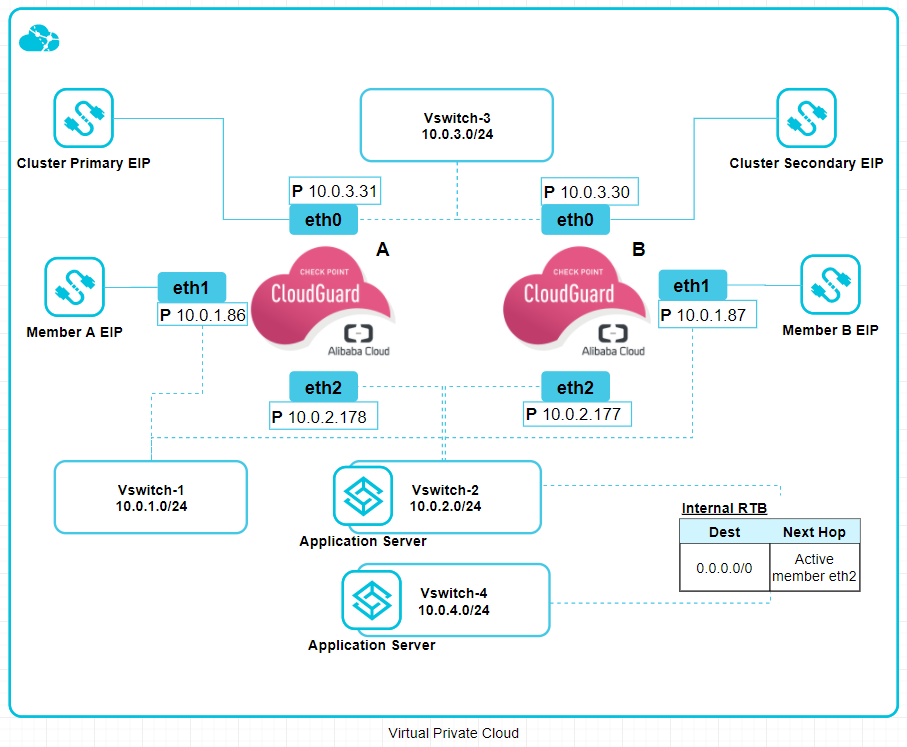
Network routing diagram:
-
Each Cloud Firewall Gateway resides in the same Alibaba Cloud Availability Zone.
-
Each Gateway has a network interface in a vSwitch
 A software abstraction of a physical Ethernet switch. It can connect to physical switches through physical network adapters to join virtual networks with physical networks. It can also be a Distributed Virtual Switch (dvSwitch), for definition and use on multiple ESXi hosts.(subnet in the VPC). The Cloud Firewall High Availability solution inspects inbound traffic from this VPC. Therefore, the Alibaba Cloud Platform Security Group rules must be configured to allow all traffic.
A software abstraction of a physical Ethernet switch. It can connect to physical switches through physical network adapters to join virtual networks with physical networks. It can also be a Distributed Virtual Switch (dvSwitch), for definition and use on multiple ESXi hosts.(subnet in the VPC). The Cloud Firewall High Availability solution inspects inbound traffic from this VPC. Therefore, the Alibaba Cloud Platform Security Group rules must be configured to allow all traffic. -
The cluster
 Two or more Security Gateways that work together in a redundant configuration - High Availability, or Load Sharing.'s public IP address is attached to the network interface of the active gateway in this network.
Two or more Security Gateways that work together in a redundant configuration - High Availability, or Load Sharing.'s public IP address is attached to the network interface of the active gateway in this network. -
Each gateway has a network interface in the vSwitch of the Management VPC. This is the network that manages the gateways.
-
The gateways have a network interface in each of the internal, optionally shared vSwitches that the Cluster secures. In each of the internal vSwitches, an Alibaba Cloud Platform Route that routs all outbound traffic (0.0.0.0/0) to the active member is automatically created.
In the diagram:
-
The Cluster protects two web applications.
Each web application has:
-
Web server
-
Application server
|
Name |
Attached to |
Use |
|---|---|---|
|
Cluster primary public address |
The external interface (eth0) of the Active Cluster Member |
VPN and publishing services. Do not disable or delete this resource. |
|
Cluster secondary public IP address |
The external interface (eth0) of the Secondary Cluster Member. |
Gets important Check Point updates. Do not disable or delete this resource. |
|
Member A public address |
Management Network Interface of Member A (eth1). |
External management of Member A Do not disable or delete this resource. |
|
Member B public address |
Management Network Interface of Member B (eth1). |
External management of Member B Do not disable or delete this resource. |
Static IP Addresses:
Use the primary public IP address of the Active member (eth0) to forward traffic that comes from the Internet.
Important - You cannot use these ports:
-
80
-
443
-
444
-
8082
-
8880
Diagram Components
The diagram shows:
-
One VPC in Alibaba Cloud Platform, contains four vSwitches(subnets):
-
Cluster
-
Management
-
Web
-
App
-
Check Point High Availability consists of two Cluster Members - Member 1 and Member 2.
Cluster vSwitch Routes
|
Destination |
Next Hop |
Type |
|---|---|---|
|
10.0.1.0/24 |
- |
System |
|
10.0.2.0/24 |
- |
System |
|
10.0.4.0/24 |
- |
System |
|
100.64.0.0/10 |
- |
System |
Management vSwitch Routes
|
Destination |
Next Hop |
Type |
|---|---|---|
|
10.0.2.0/24 |
- |
System |
|
10.0.3.0/24 |
- |
System |
|
10.0.4.0/24 |
- |
System |
|
100.64.0.0/10 |
- |
System |
Routes for each internal vSwitch
Web Server Internal vSwitch
|
Destination |
Next Hop |
Type |
|---|---|---|
|
10.0.1.0/24 |
- |
System |
|
10.0.3.0/24 |
- |
System |
|
10.0.4.0/24 |
- |
System |
|
100.64.0.0/10 |
- |
System |
|
0.0.0.0/0 |
Active Member eth2 |
Custom |
App Internal vSwitch
|
Destination |
Next Hop |
Type |
|---|---|---|
|
10.0.1.0/24 |
- |
System |
|
10.0.2.0/24 |
- |
System |
|
10.0.3.0/24 |
- |
System |
|
100.64.0.0/10 |
- |
System |
|
0.0.0.0/0 |
Active Member eth2 |
Custom |
Failover
The following occurs during cluster failover:
-
When the active gateway fails, the standby member will identify the failure, and then do the following:
-
Detach the cluster's public IP address from the failed member.
-
-
Detach the cluster's secondary public IP address from the standby member. When the failed members return to standby state, it will attach this address to itself.
-
Attach the cluster's public IP address to itself.
-
All VPCs route tables holding a route to MemberA-eth2 - the route is deleted and re-added pointing to MemberB-eth2.
|
|
Note - This usually happens in less than 40 seconds. This affects East-West, inbound, outbound and VPN tunnel failover. |
These are the expected failover times - based on use cases:
|
Use Case |
Expected Failover Time |
Comments |
|---|---|---|
|
Site-to-Site VPN |
Less than 40 seconds |
Depends on Alibaba Cloud API. |
|
Inbound inspection through primary public IP |
Less than 40 seconds |
Depends on Alibaba Cloud API. |
|
Outbound inspection through primary public IP |
Less than 40 seconds |
Depends on Alibaba Cloud API. |
|
East-West inspection |
Less than 30 seconds |
Depends on Alibaba Cloud API. |
Traffic Flows
|
|
Note - Other ECS instances cannot be deployed in the Check Point solution vSwitches. |
Inbound VPN Traffic
-
Packet enters the frontend network interface (eth0) of the Active Cluster Member.
-
The Active Cluster Member decrypts the packet.
-
The Active Cluster Member forwards the packet to its destination.
Outbound Traffic
-
Traffic travels to an Active Cluster Member based on the route.
-
The Active Cluster Member inspects the traffic and forwards it to the destination.
East-West Traffic
-
Traffic travels from one of the internal servers to the Active Cluster Member.
-
The Active Cluster Member forwards the traffic to the destination.
Intra-Subnet Traffic
Traffic travels freely in the subnet without inspection.