Scaling In and Scaling Out in Cloud Firewall for GCP MIG
Background
Network Diagram
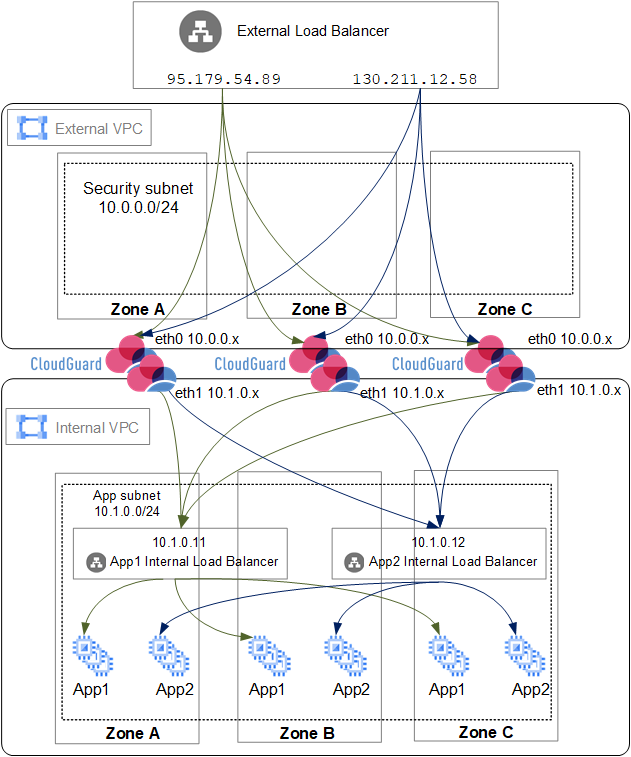
The Google Cloud Platform![]() A suite of products and services that includes hosting, cloud computing, database services and more. Acronym: GCP. (GCP
A suite of products and services that includes hosting, cloud computing, database services and more. Acronym: GCP. (GCP![]() See "Google Cloud Platform".) environment contains two Virtual Private Clouds (VPCs) - an External VPC and an Internal VPC - as shown in the diagram below.
See "Google Cloud Platform".) environment contains two Virtual Private Clouds (VPCs) - an External VPC and an Internal VPC - as shown in the diagram below.
An External Load Balancer directs incoming traffic to an Autoscaling Managed Instance Group (MIG) in the external VPC. Cloud Firewall Gateways in this group inspect the traffic. If allowed by policy, traffic is forwarded to an Internal Load Balancer. The Internal Load Balancer distributes traffic to servers in a more secure internal network.
Cloud Firewall Gateways are managed by the Security Management Server![]() Dedicated Check Point server that runs Check Point software to manage the objects and policies in a Check Point environment within a single management Domain. Synonym: Single-Domain Security Management Server. located in GCP or on-premises.
Dedicated Check Point server that runs Check Point software to manage the objects and policies in a Check Point environment within a single management Domain. Synonym: Single-Domain Security Management Server. located in GCP or on-premises.
GCP Autoscale adjusts the number of Cloud Firewall Gateways in the MIG based on the traffic load.
It uses two main events:
-
Scale Out: Adds Cloud Firewall Gateways to the MIG when the traffic load increases.
-
Scale In: Removes Cloud Firewall Gateways from the MIG when the traffic load decreases.
Default Cloud Firewall Gateway![]() Check Point Virtual Security Gateway that protects dynamic virtual environments with policy enforcement. Cloud Firewall Gateway inspects traffic between Virtual Machines to enforce security, without changing the Virtual Network topology. CPU thresholds to trigger autoscaling events:
Check Point Virtual Security Gateway that protects dynamic virtual environments with policy enforcement. Cloud Firewall Gateway inspects traffic between Virtual Machines to enforce security, without changing the Virtual Network topology. CPU thresholds to trigger autoscaling events:
-
Scale Out: Triggers at 80% CPU use (5-minute average).
-
Scale In: Triggers at 60% CPU use (5-minute average).
Scale Out
When a scale-out event triggers:
-
GCP Autoscale launches new Cloud Firewall Gateways.
-
New Cloud Firewall Gateways automatically run the First Time Configuration Wizard and reboot.
-
The Security Management Server
 Check Point Single-Domain Security Management Server or a Multi-Domain Security Management Server.:
Check Point Single-Domain Security Management Server or a Multi-Domain Security Management Server.:-
Detects new Cloud Firewall Gateway instances.
-
Establishes a Secure Internal Communication (SIC
 Secure Internal Communication. The Check Point proprietary mechanism with which Check Point computers that run Check Point software authenticate each other over SSL, for secure communication. This authentication is based on the certificates issued by the ICA on a Check Point Management Server.) channel with these Cloud Firewall Gateway instances.
Secure Internal Communication. The Check Point proprietary mechanism with which Check Point computers that run Check Point software authenticate each other over SSL, for secure communication. This authentication is based on the certificates issued by the ICA on a Check Point Management Server.) channel with these Cloud Firewall Gateway instances. -
Installs a Security Policy
 Collection of rules that control network traffic and enforce organization guidelines for data protection and access to resources with packet inspection. on each new Cloud Firewall Gateway.
Collection of rules that control network traffic and enforce organization guidelines for data protection and access to resources with packet inspection. on each new Cloud Firewall Gateway.
-
-
External Load Balancer starts sending traffic to these new Cloud Firewall Gateways.
|
|
Note - For R81.10 and higher, Cloud Firewall Gateways automatically respond to health checks on port 8117 after CME configuration. New Cloud Firewall Gateways report their status and send logs to the Security Management Server. |
|
|
Note - During scale-out events in dual-stack (IPv4/IPv6) deployments, initial Security Policy installation on newly provisioned Cloud Firewall Gateways can fail while network interfaces are not fully initialized and connectivity is not yet established. The Security Management Server automatically retries the policy installation, which typically succeeds within 2–3 minutes and does not require manual intervention. |
Scale In
When a scale-in event triggers:
-
GCP Autoscale marks one or more Cloud Firewall Gateways as candidates for termination.
-
The External Load Balancer stops sending traffic to marked Cloud Firewall Gateways.
-
GCP Autoscale terminates marked Cloud Firewall Gateways.
-
The Security Management Server removes terminated Cloud Firewall Gateways from its database.
|
|
Important - Keep at least two Cloud Firewall Gateways (one in each Availability Zone) running for redundancy and availability. |
Testing Scale-In and Scale-Out Processes
The initial solution deployment process includes these steps:
-
After the Check Point Cloud Firewall for GCP Autoscaling MIG solution is deployed, it creates Cloud Firewall Gateways with the
autoprovtool. -
Each new Cloud Firewall Gateway automatically runs the First Time Configuration Wizard. This usually takes 10 minutes to complete. Large Virtual Machines may require additional time.
-
After configuration is completed, the Security Management Server automatically installs the Security Policy on these Cloud Firewall Gateways.
-
To verify deployment success, use SmartConsole
 Check Point GUI application used to manage a Check Point environment - configure Security Policies, configure devices, monitor products and events, install updates, and so on. to:
Check Point GUI application used to manage a Check Point environment - configure Security Policies, configure devices, monitor products and events, install updates, and so on. to:-
Confirm the Security Policy installation.
-
Verify log generation and transmission by Cloud Firewall Gateways.
-
-
Connect to the Cloud Firewall Gateway command line interface (CLI) over SSH.
-
Enter Expert mode.
-
Create a script to load the CPUs of Cloud Firewall Gateways at
/var/tmp/simulate_cpu_load.sh:[Expert@HostName:0]# vi /var/tmp/simulate_cpu_load.sh#!/bin/bashncores="$(cat /proc/cpuinfo | grep vendor_id | wc -l)"PIDS=()for i in $(seq $ncores)dotaskset ff dd if=/dev/zero of=/dev/null &PIDS+=($!)doneecho "Load started"read -n1 -r -p "Press any key to stop the load..." key
kill ${PIDS[@] } -
Set execute permissions to the script:
[Expert@HostName:0]# chmod u+x /var/tmp/simulate_cpu_load.sh -
Execute the script to simulate a high CPU load:
[Expert@HostName:0]# ./var/tmp/simulate_cpu_load.sh -
Monitor CPU load in a separate terminal (it must be at a high level):
top
Note - After 10 minutes of high CPU load, a scale-out event triggers. GCP Autoscale provisions a new Cloud Firewall Gateway.
-
After the new Cloud Firewall Gateway is provisioned, press any key to stop the simulation script on the original Cloud Firewall Gateway.
-
Monitor CPU load in a separate terminal (it must return to normal levels):
top
Note - After 10 minutes of normal CPU load, a scale-in event triggers. The Cloud Firewall Management Server automatically removes the newly provisioned Cloud Firewall Gateway.